Most phishing web sites are little greater than static copies of login pages for fashionable on-line locations, and they’re usually shortly taken down by anti-abuse activists and safety companies. However a stealthy new phishing-as-a-service providing lets clients sidestep each of those pitfalls: It makes use of cleverly disguised hyperlinks to load the goal model’s actual web site, after which acts as a relay between the goal and the official website — forwarding the sufferer’s username, password and multi-factor authentication (MFA) code to the official website and returning its responses.
There are numerous phishing kits that would-be scammers can use to get began, however efficiently wielding them requires some modicum of ability in configuring servers, domains, certificates, proxy providers, and different repetitive tech drudgery. Enter Starkiller, a brand new phishing service that dynamically hundreds a stay copy of the true login web page and information all the pieces the person varieties, proxying the information from the official website again to the sufferer.
In line with an evaluation of Starkiller by the safety agency Irregular AI, the service lets clients choose a model to impersonate (e.g., Apple, Fb, Google, Microsoft et. al.) and generates a misleading URL that visually mimics the official area whereas routing visitors by way of the attacker’s infrastructure.
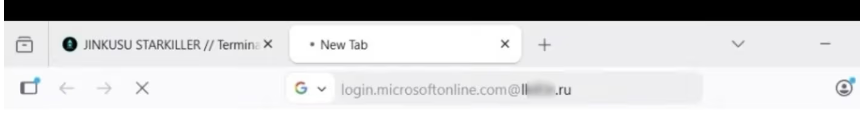
For instance, a phishing hyperlink focusing on Microsoft clients seems as “login.microsoft.com@[malicious/shortened URL here].” The “@” signal within the hyperlink trick is an oldie however goodie, as a result of all the pieces earlier than the “@” in a URL is taken into account username knowledge, and the true touchdown web page is what comes after the “@” signal. Right here’s what it seems to be like within the goal’s browser:
Picture: Irregular AI. The precise malicious touchdown web page is blurred out on this image, however we are able to see it ends in .ru. The service additionally gives the flexibility to insert hyperlinks from completely different URL-shortening providers.
As soon as Starkiller clients choose the URL to be phished, the service spins up a Docker container operating a headless Chrome browser occasion that hundreds the true login web page, Irregular discovered.
“The container then acts as a man-in-the-middle reverse proxy, forwarding the end user’s inputs to the legitimate site and returning the site’s responses,” Irregular researchers Callie Baron and Piotr Wojtyla wrote in a weblog submit on Thursday. “Every keystroke, form submission, and session token passes through attacker-controlled infrastructure and is logged along the way.”
Starkiller in impact gives cybercriminals real-time session monitoring, permitting them to live-stream the goal’s display as they work together with the phishing web page, the researchers stated.
“The platform also includes keylogger capture for every keystroke, cookie and session token theft for direct account takeover, geo-tracking of targets, and automated Telegram alerts when new credentials come in,” they wrote. “Campaign analytics round out the operator experience with visit counts, conversion rates, and performance graphs—the same kind of metrics dashboard a legitimate SaaS [software-as-a-service] platform would offer.”
Irregular stated the service additionally deftly intercepts and relays the sufferer’s MFA credentials, for the reason that recipient who clicks the hyperlink is definitely authenticating with the true website by way of a proxy, and any authentication tokens submitted are then forwarded to the official service in actual time.
“The attacker captures the resulting session cookies and tokens, giving them authenticated access to the account,” the researchers wrote. “When attackers relay the entire authentication flow in real time, MFA protections can be effectively neutralized despite functioning exactly as designed.”
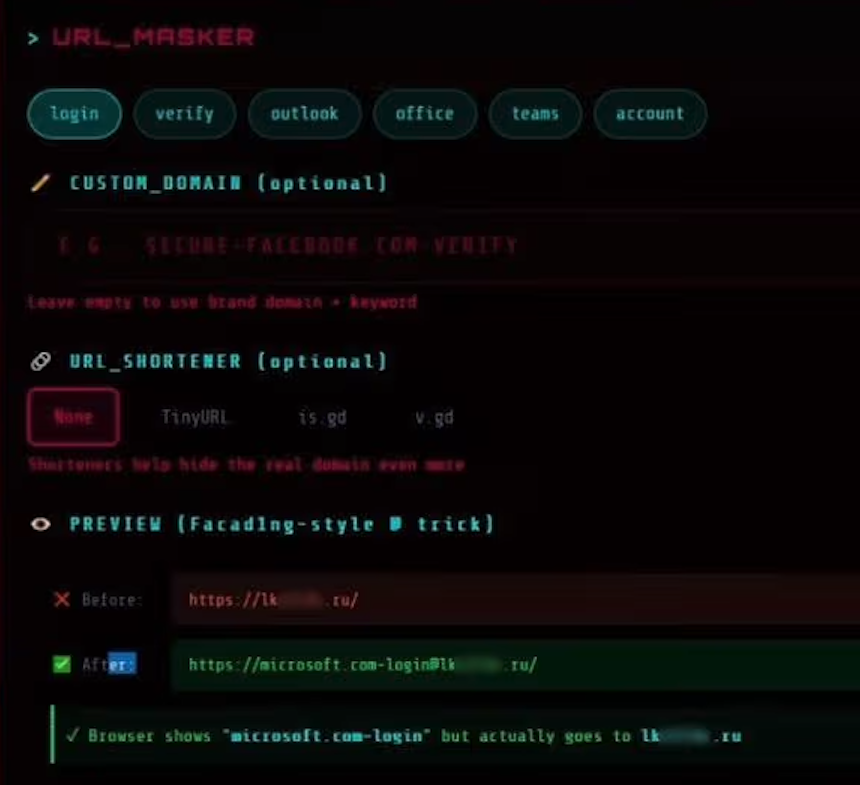
The “URL Masker” characteristic of the Starkiller phishing service options choices for configuring the malicious hyperlink. Picture: Irregular.
Starkiller is only one of a number of cybercrime providers provided by a risk group calling itself Jinkusu, which maintains an lively person discussion board the place clients can talk about strategies, request options and troubleshoot deployments. One a-la-carte characteristic will harvest electronic mail addresses and speak to info from compromised periods, and advises the information can be utilized to construct goal lists for follow-on phishing campaigns.
This service strikes me as a outstanding evolution in phishing, and its obvious success is prone to be copied by different enterprising cybercriminals (assuming the service performs in addition to it claims). In spite of everything, phishing customers this manner avoids the upfront prices and fixed hassles related to juggling a number of phishing domains, and it throws a wrench in conventional phishing detection strategies like area blocklisting and static web page evaluation.
It additionally massively lowers the barrier to entry for novice cybercriminals, Irregular researchers noticed.
“Starkiller represents a significant escalation in phishing infrastructure, reflecting a broader trend toward commoditized, enterprise-style cybercrime tooling,” their report concludes. “Combined with URL masking, session hijacking, and MFA bypass, it gives low-skill cybercriminals access to attack capabilities that were previously out of reach.”