Passwords stay a persistent level of stress between usability and safety. Controls designed to strengthen authentication usually introduce complexity, which inspires customers to depend on acquainted patterns quite than genuinely unpredictable credentials. In apply, this continuously leads to passwords derived from a corporation’s personal language.
Attackers have lengthy acknowledged this behavioral sample and proceed to use it. Somewhat than counting on synthetic intelligence or refined guessing algorithms, many credential assaults start with one thing far less complicated: harvesting contextual language and changing it into extremely focused password guesses.
Instruments resembling Customized Phrase Checklist turbines (CeWL) make this course of environment friendly and repeatable with out introducing further technical complexity, considerably bettering success charges whereas decreasing noise and detection threat.
This attacker conduct helps clarify why NIST SP 800-63B explicitly advises in opposition to using context-specific phrases in passwords, together with service names, usernames, and associated derivatives. Imposing that steerage, nevertheless, requires an understanding of how attackers assemble and operationalize these wordlists in real-world assaults.
This distinction issues as a result of many defensive methods nonetheless assume that password guessing depends on broad, generic datasets.
The place focused wordlists actually come from
CeWL is an open-source internet crawler that extracts phrases from web sites and compiles them into structured lists. It’s included by default in broadly used penetration testing distributions resembling Kali Linux and Parrot OS, which lowers the barrier to entry for each attackers and defenders.
Attackers use CeWL to crawl a corporation’s public-facing digital presence and accumulate terminology that displays how that group communicates externally.
This sometimes contains firm service descriptions, inner phrasing surfaced in documentation, and industry-specific language that might not seem in generic password dictionaries.
The effectiveness of this method lies not in novelty, however in relevance. The ensuing wordlists intently mirror the vocabulary customers already encounter of their day-to-day work and are due to this fact extra more likely to affect password development.
Verizon’s Knowledge Breach Investigation Report discovered stolen credentials are concerned in 44.7% of breaches.
Effortlessly safe Lively Listing with compliant password insurance policies, blocking 4+ billion compromised passwords, boosting safety, and slashing assist hassles!
Attempt it at no cost
From public-facing content material to password guesses
CeWL could be configured to manage crawl depth and minimal phrase size, permitting attackers to exclude low-value outcomes. When harvested on this manner, the output kinds reasonable password candidates via predictable transformations.
For a healthcare group, for instance, a hospital, public-facing content material could expose phrases such because the identify of the group, references to its location, or the providers or remedies it provides.
These phrases are hardly ever used as passwords in isolation however as a substitute function a foundational candidate set that attackers systematically modify utilizing frequent patterns resembling numeric suffixes, capitalization, or appended symbols to generate believable password guesses.
As soon as attackers acquire password hashes, usually via third-party breaches or infostealer infections, instruments resembling Hashcat apply these mutation guidelines at scale. Hundreds of thousands of focused candidates could be generated and examined effectively in opposition to compromised information.
The identical wordlists will also be used in opposition to dwell authentication providers, the place attackers could depend on throttling, timing, or low-and-slow guessing methods to cut back the probability of detection or account lockout.
Why password complexity guidelines nonetheless fail
A key problem is that many passwords generated on this manner fulfill commonplace complexity necessities.
Specops evaluation of greater than six billion compromised passwords means that organizations proceed to wrestle with this distinction, even the place consciousness and coaching packages are in place. When passwords are constructed from acquainted organizational language, added size or character selection does little to offset the lowered uncertainty launched by extremely contextual base phrases.
A password resembling HospitalName123! illustrates this downside extra clearly. Whereas it exceeds default Lively Listing complexity necessities, it stays a weak selection inside a healthcare setting.
CeWL-derived wordlists readily determine group names and abbreviations harvested from public-facing content material, permitting attackers to reach at believable password variants via minimal and systematic modification.
Defending in opposition to focused wordlist assaults
Decreasing publicity to wordlist-based assaults requires controls that deal with password development quite than complexity alone.
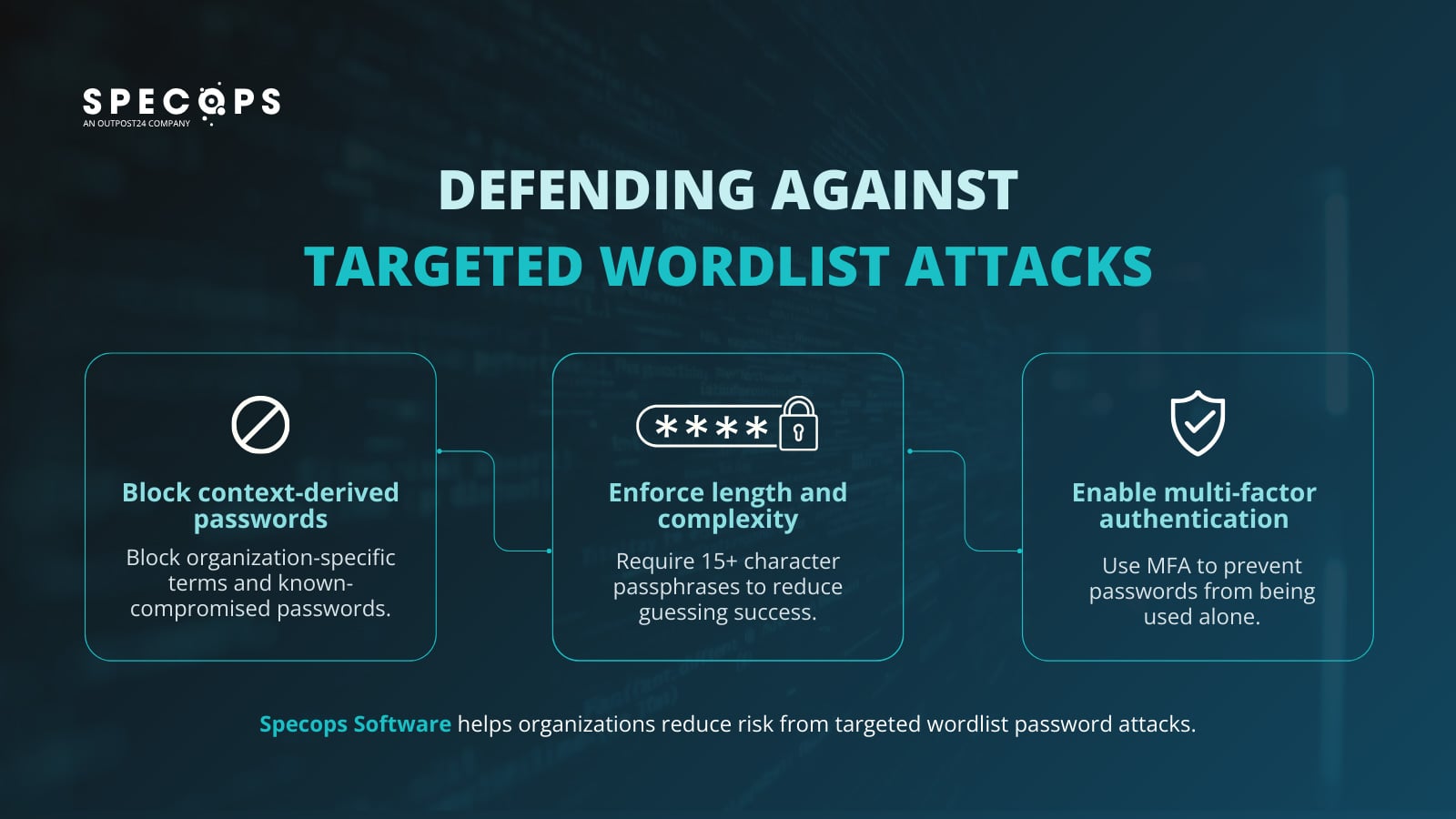
Block context-derived and known-compromised passwords
Stop customers from creating passwords based mostly on organization-specific language resembling firm and product names, inner mission phrases, {industry} vocabulary, and customary attacker substitutions, whereas additionally blocking credentials which have already appeared in information breaches.
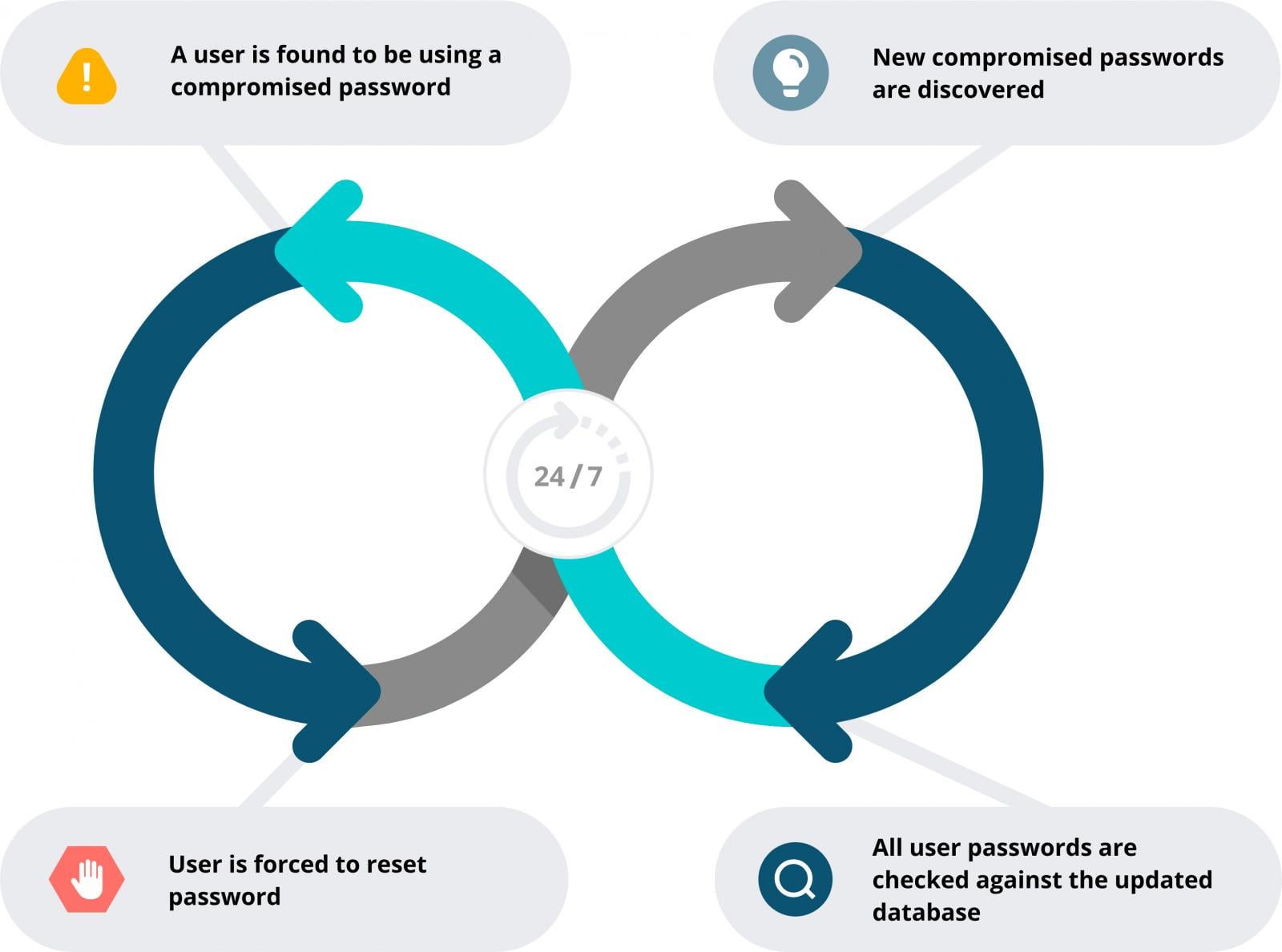
Specops Password Coverage can implement customized exclusion dictionaries and repeatedly scans Lively Listing in opposition to greater than 5.4 billion known-compromised passwords, disrupting CeWL-style wordlist assaults and decreasing the reuse of uncovered credentials.
Implement minimal size and complexity
Require no less than 15-character passphrases, as size and unpredictability supply the most effective safety in opposition to brute-force methods. Passphrases are one of the simplest ways to get customers to create sturdy, lengthy passwords.
Allow multi-factor authentication (MFA)
Should you haven’t already, that is the apparent place to start out. Contemplate a easy, efficient MFA answer resembling Specops Safe Entry that may shield Home windows Logon, VPNs, and RDP connections.
Whereas MFA doesn’t stop password compromise, it considerably limits the affect of credential publicity by stopping passwords from getting used as a standalone authentication issue.
Align password coverage with real-world assaults
Deal with passwords as an energetic safety management quite than a static compliance requirement. Imposing insurance policies that stop context-derived, beforehand uncovered, or simply inferred passwords reduces the worth attackers achieve from focused wordlists, whereas MFA offers a crucial second line of protection when credentials are compromised.
Collectively, these controls type a extra resilient authentication technique that displays how password assaults really happen.
Converse with certainly one of our specialists to find out how Specops can assist stronger, extra resilient password safety with out including pointless complexity for customers.
Sponsored and written by Specops Software program.



