Written by Ran Geva, CEO at Webz.io & Lunarcyber.com
In 2026, stolen credentials are a top-tier safety precedence. They’re additionally a paradox: regardless that they’re thought-about a big danger, enterprises nonetheless go for checkbox options and generic instruments to mitigate the issue.
Based on a current survey commissioned by Lunar, a dark-web monitoring platform powered by Webz.io, 85% of organizations rank stolen credentials as a excessive or very excessive danger, with 62% saying they’re of their top-three safety priorities.
On the identical time, I’ve spoken with dozens of organizations utilizing Lunar’s group platform, who’ve informed me issues like, “we have MFA everywhere, so we’re covered”, and “our EDR and zero-trust stack already protects our employees.”
They fail to understand that EDR and zero-trust measures provide no safety when an worker logs right into a vital SaaS service from an unmanaged residence machine.
The implications of failing to detect stolen credentials in time may be catastrophic. Based on IBM’s Value of a Knowledge Breach Report, a breach involving compromised credentials prices between $4.81-4.88 million.
Contemplating that Lunar noticed 4.17 billion compromised credentials in 2025 alone, the potential international price of those assaults is staggering. All of because of this easy breach monitoring is now not sufficient.
An enterprise mindset shift is required to create a programmatic protection technique that tackles the ever-evolving menace of infostealers.
Checkbox Monitoring and The Risks of Utilizing Generic Options
When talking with organizations, I at all times ask how they mitigated the infostealer menace earlier than onboarding Lunar. The solutions I get comply with the identical sample: Uncovered credentials are a major problem and we devoted sources to options to mitigate the menace.
What they didn’t understand is that these options have been missing and primarily consisted of:
-
A give attention to information breaches as an alternative of infostealers
-
ULPs and non-forensic infostealer information
-
Excessive latency and off information sources
-
No automation, integrations, or investigation capabilities
Our analysis lays out simply how critical the issue is. Solely 32% of enterprises that we surveyed use devoted credential monitoring options, whereas 17% haven’t any tooling in any respect.
In the meantime, greater than 60% of organizations verify for uncovered credentials month-to-month, not often, or under no circumstances.
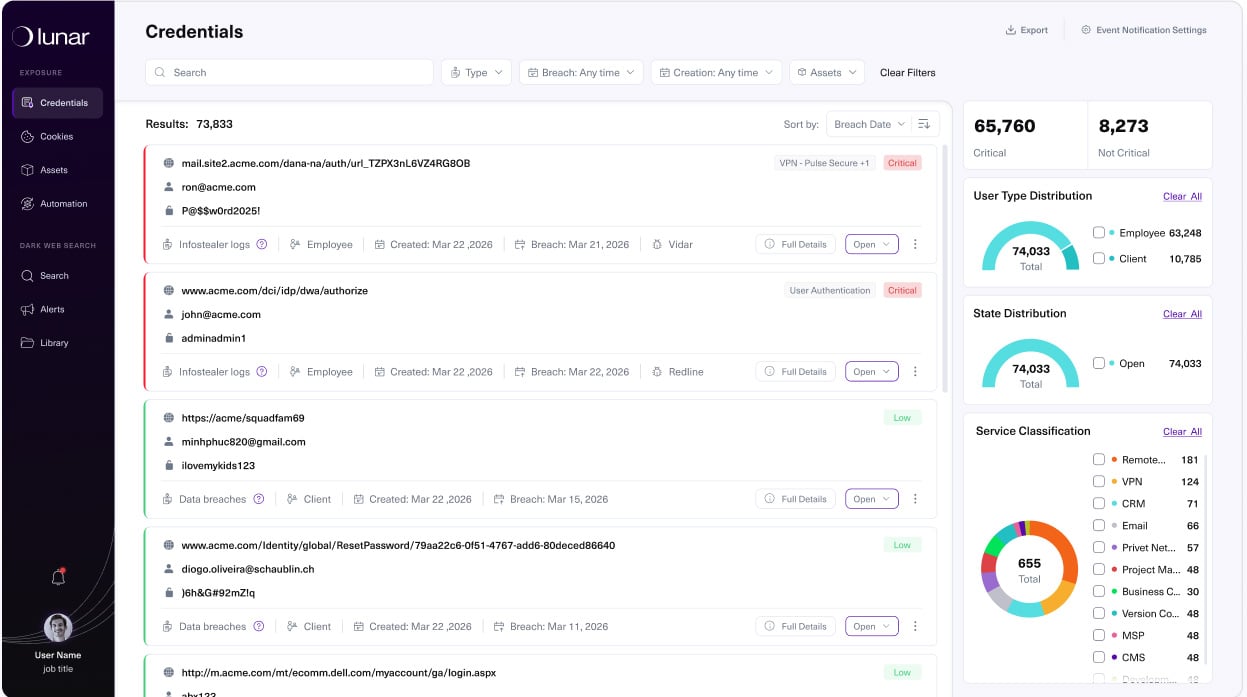
We’ve seen firsthand how these options carry out. When new organizations onboard Lunar, many are shocked to understand that whereas their earlier instruments informed them {that a} breach had occurred, they by no means received the instruments to correctly examine the way it occurred.
The forensic particulars, together with the accounts that have been compromised, the units contaminated, the SaaS apps that might be impacted, to not point out the session cookies that have been stolen, have been merely not there.
Whereas the checkbox strategy is healthier than no safety in any respect, it not often offers the forensic element that enterprises have to efficiently mitigate the infostealer menace. So, what’s holding them again from scaling their operations?
See the place your organization’s credentials and session cookies are already uncovered.
Lunar repeatedly screens breaches and infostealer logs to your domains and surfaces actionable exposures in a free, enterprise‑grade dashboard.
Signal Up Free
The Infostealer Menace is A lot Larger Than Enterprises Suppose
That is the place the infostealer paradox enters into our conversations. Whereas everybody is aware of in regards to the risks of uncovered credentials, they both fail to prioritize budgets or just don’t know what sorts of options efficiently mitigate the issue.
Moreover, they don’t at all times perceive simply how prevalent credential theft really is, the environments they aim, and the data they will entry.
From the 4.17 billion compromised-credential data we collected in 2025, we analyzed infostealer logs, stealer-derived combolists, marketplaces, and Telegram channels. Infostealers like LummaC2, Rhadamanthys, Vidar, Acreed, and others persistently slipped previous enterprise monitoring, even in environments that thought-about themselves mature.
And whereas many new Lunar customers thought that the macOS was safer than Home windows, they have been shocked to listen to about households like Atomic macOS Stealer (AMOS), Odyssey, MacSync, MioLab, and Atlas.
There’s additionally an consciousness downside concerning the info infostealers exfiltrate, which fits far past easy username/password pairs. With fashionable infostealers now offered as full-fledged merchandise, with subscription tiers, dashboards, and documentation tuned to harvesting cookies, session tokens, and SaaS entry at scale, organizations are actually in a rush to catch up and defend their networks.
For menace actors, session cookies don’t simply present entry. They successfully open the entrance door, letting them skip login pages completely: no password immediate, no MFA problem, and sometimes no apparent hint in customary authentication logs.
That’s the piece of the puzzle that many organizations are solely now internalizing.
What Does a Typical Infostealer Assault Look Like?
After we speak about what an infostealer assault appears like, and why checkbox safety is ineffective, we regularly break it down into the next course of:
-
Goal is contaminated: The sufferer’s machine is compromised by an infostealer delivered by means of vectors akin to zero-day exploits, ClickFix campaigns, rogue browser extensions, unverified or pirated software program, recreation mods, or malicious open-source tasks.
-
Credentials are exfiltrated: The infostealer extracts the browser for logins and cookies, together with these from third-party portals, and sends them again to the malware operator.
-
Credentials are bundled and offered: The stolen credentials are bundled into logs and offered on underground markets and personal channels.
-
Attackers entry the enterprise community: The attacker who purchases the logs accesses the goal community, together with third-party portals, utilizing a sound session token.
This whole chain of occasions may be accomplished in hours. In the meantime, lots of the organizations we communicate with run credential checks as soon as a month or depend on outdated information.
By the point something exhibits up of their legacy monitoring instruments, attackers have had loads of time to discover and exfiltrate no matter information they need.
Creating a Mature Breach Monitoring Program
Organizations we work with that make the swap to a mature breach monitoring program have the instruments they should acquire info from channels like stealer logs, Telegram teams, and marketplaces. As a substitute of counting on ad-hoc checks, they give attention to three sensible capabilities:
-
Steady monitoring and normalization of key sources (breaches, stealer logs, combolists, marketplaces, and related channels), so safety groups have a transparent and deduplicated view of breach exposures.
-
Focused automation that reduces false positives and noise, guaranteeing that analysts spend time on identities and classes that truly matter.
-
Integrations into current safety and id stacks (SIEM, SOAR, IDP) that execute playbooks end-to-end, resetting credentials, invalidating classes, and blocking accounts as quickly as exposures are confirmed.
Amongst Lunar customers, we’ve seen a transparent mindset shift as soon as they get this proper. They deal with the infostealer menace as its personal area, full with possession, metrics, and playbooks, as an alternative of managing their breach monitoring utilizing unrelated instruments.
This all goes again to Lunar’s core mission, which is to offer a free breach monitoring answer to any group, no matter funds, that delivers enterprise-grade protection of compromised credentials, infostealers, and session cookies.
Our philosophy is to brazenly present enriched compromised credential intelligence, enabling organizations to regain true visibility and resilience.
Redefining Breach Monitoring in 2026
Even seasoned and educated safety groups can fall into the breach monitoring paradox, the place they know the menace however behave as if month-to-month checks, MFA, and EDR are sufficient. However in 2026, infostealers transfer at a velocity and scale that checkbox monitoring options have been by no means designed to deal with.
Treating breach monitoring as vital program, as an alternative of a one-off product, offers your enterprise with the visibility wanted to view compromised credentials wherever they seem, the context to grasp what these exposures imply, and the playbooks to routinely react when an assault is detected.
To see how Lunar can assist you discover your group’s compromised credentials, join free entry.
Sponsored and written by Lunar.