Fraudulent telephone calls have turn into a each day actuality for thousands and thousands of individuals worldwide. From faux regulation enforcement officers to financial institution representatives and impersonated tech assist brokers, victims are more and more focused via direct, real-time conversations designed to create urgency accompanied by excessive psychological stress to extract delicate info or cash theft.
Experiences present that one of these cybercrime considerably impacts society each financially and emotionally. Based on the FBI, US aged residents (60+) misplaced $3.4B in 2023. One other report exhibits that vishing elevated by 449% in 2025 and the typical loss per rip-off name is $3,690.
On this article, we shine a light-weight on what may be described as “Caller-as-a-Service”, which is an under-explored but quickly evolving side of recent cybercrime. We study how, very like legit gross sales organizations, risk actors have adopted structured, business-like working fashions, full with specialization, scalability, and performance-driven execution.
These ecosystems are not advert hoc. They’re composed of distinct roles and capabilities, with completely different actors specializing in particular phases of the assault lifecycle: from infrastructure and tooling to social engineering execution.
We discover how these networks function, together with their recruitment methods, outlined roles and duties, and even tailor-made compensation fashions—all of which intently mirror legit market dynamics.
The result’s a extremely organized, service-driven financial system that professionalizes fraud at scale, reducing the barrier to entry whereas growing each effectivity and affect.
A Structured Organized Market
The rip-off name ecosystem has turn into extremely professionalized and segmented, mirroring legit enterprise operations. Distinct roles now exist throughout the worth chain, together with malware builders, distributors, phishing equipment builders, infrastructure operators, log sellers, information analysts, sufferer listing merchants, and at last, rip-off callers who execute the assaults.
This division of labor permits every participant to specialize. For callers, who’re solely centered on interacting with victims, the emphasis shifts towards recruitment high quality and operational professionalism relatively than technical functionality.
Consequently, the barrier to entry is considerably lowered. People not must develop malware or handle infrastructure, and so they can give attention to refining communication expertise, persuasion methods, and social engineering ways.
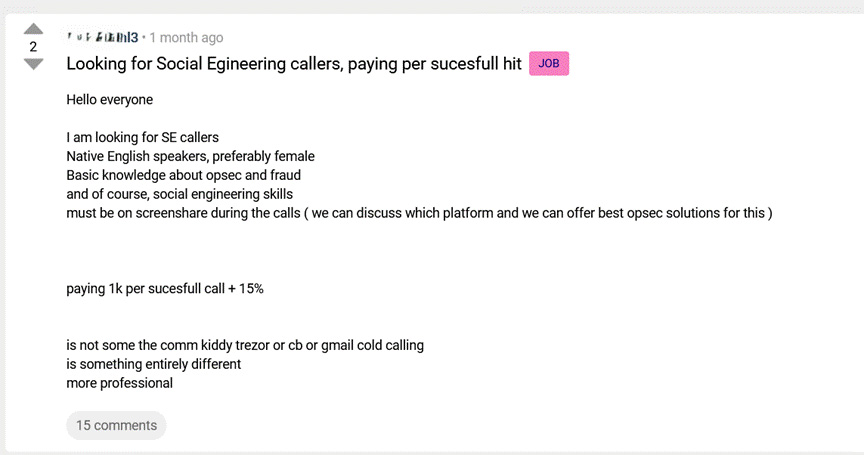
Recruitment posts mirror this specialization. They sometimes define clear necessities corresponding to native English proficiency, familiarity with operational safety (OPSEC), and prior fraud expertise. Notably, some roles require individuals to stay on display share throughout stay calls.
This requirement is especially revealing. It signifies that operators are usually not merely outsourcing duties, however actively supervising efficiency in actual time. This introduces a degree of high quality management and operational oversight extra generally related to legit name facilities than with conventional cybercrime.
Such supervision serves a number of functions: guaranteeing adherence to scripts, bettering conversion charges, and stopping inside fraud or information leakage. In the end, this layered and managed mannequin highlights how trendy fraud operations are managed with the identical logic, construction, and effectivity as legit companies.
Structured fraud operations depend on leaked credentials and sufferer lists sourced from underground markets.
Flare displays 1000’s of darkish net boards, Telegram channels, and marketplaces, so your crew can detect uncovered information earlier than it fuels the following rip-off marketing campaign.
Sustain with risk actors without cost.
Underground Recruitment Techniques
When legit firms wish to entice potential staff, they illustrate robust monetary spine, buyer testimonials, and even happy staff photos.
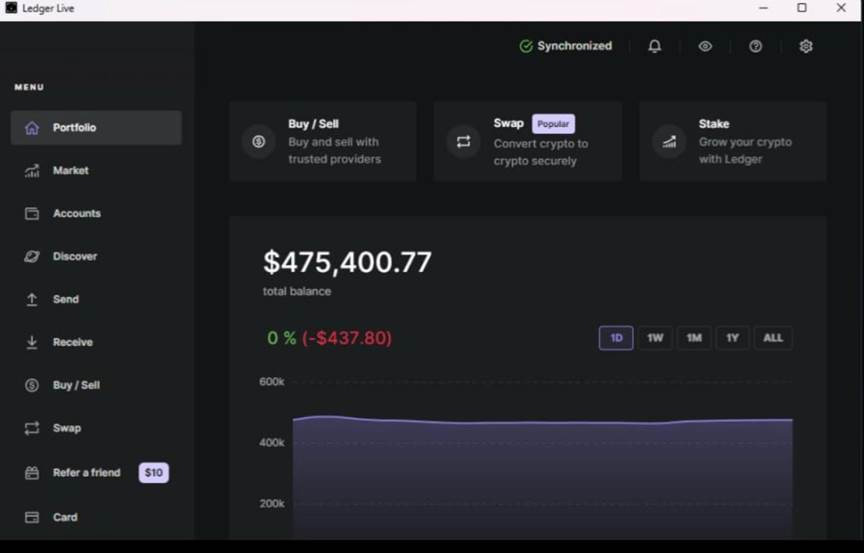
Within the underground, a screenshot of a excessive steadiness of the corporate’s cryptocurrency pockets is sufficient. A steadiness of roughly $475,000 serves as a recruitment support designed to draw recruitments. Such “proof-of-profit” visuals are generally utilized in underground communities to determine credibility and display potential earnings. Whether or not genuine or fabricated, their goal is to scale back skepticism and encourage participation.
This tactic displays broader tendencies in cybercriminal ecosystems, the place fame and perceived success play a major position in recruitment and collaboration.
Rip-off Callers Compensation Fashions
Flare’s evaluation signifies that numerous compensation fashions exist together with fastened funds, success-based funds and a hybrid method that mixes each fastened funds and success-based funds.
In a single mannequin, callers obtain a proportion of extracted funds, with larger percentages awarded for bigger payouts. In one other mannequin, operators provide a set fee of $1,000 per profitable name, supplemented by a further proportion.
Conversations between risk actors present insights concerning the compensation mannequin. One operator explains that profitable social engineering doesn’t all the time translate into speedy monetization, thus the compensation can be delayed or conditioned.
This distinction is vital. It signifies that the fraud course of extends past the preliminary name, involving further steps to transform entry or info into monetary achieve. Consequently, operators compensate callers for profitable engagement whereas retaining management over downstream monetization processes.
Individuals do not merely settle for phrases. They ask questions, examine presents, and weigh compensation earlier than committing. It is a dynamic indistinguishable from any legit job market.
Rip-off Callers Job Necessities, Roles and Obligations
Very similar to job postings on LinkedIn, underground operators craft well-defined and extremely focused recruitment advertisements. These postings are removed from generic, and so they clearly define the required traits, duties, and expertise for every position, reflecting a degree of maturity sometimes related to legit organizations.
For rip-off callers, the emphasis goes past technical functionality. Candidates are anticipated to display robust gentle expertise, together with clear communication, emotional intelligence, and superior psychological manipulation methods. At their core, these roles revolve across the capacity to construct belief, create urgency, and persuade victims into actions that result in monetary loss or account compromise.
A notable sample is the desire for native English audio system, indicating deliberate concentrating on of particular geographic areas. This highlights the significance positioned on cultural alignment and linguistic fluency to maximise success charges.
When mixed with real-time supervision and efficiency suggestions, these operations resemble structured gross sales flooring, the place social engineering isn’t solely executed, however repeatedly refined and optimized for larger conversion.
Shift Towards Industrialized Social Engineering
The convergence of recruitment, supervision, structured incentives, and modular workflows displays a broader shift towards industrialized fraud operations. This mannequin mirrors developments seen in ransomware-as-a-service (RaaS) and preliminary entry brokerage, the place specialization and division of labor drive effectivity.
Nevertheless, on this case, the first assault vector is human interplay, making it each accessible and tough to detect.
Implications for Defenders and People
These threats mirror a transparent shift towards structured, scalable fraud operations, posing rising challenges for each organizations and people.
The decentralized nature of those ecosystems makes disruption inherently tough. Eradicating particular person callers has restricted affect, as vital elements (sufferer information, operators, and monetization channels) are distributed and resilient.
On the similar time, the reliance on compromised information sources reinforces a key actuality: upstream breaches straight gasoline downstream fraud.
Compounding that is the growing degree of professionalism. With components corresponding to real-time supervision, outlined workflows, and structured compensation fashions, these operations have gotten extra constant, environment friendly, and tougher to detect.
To counter this, defenders ought to prioritize:
- Stronger identification verification mechanisms
- Behavioral anomaly detection
- Consumer consciousness centered on real-time social engineering eventualities
For people, it’s vital to know that fraudulent calls are not often random, they’re usually a part of coordinated, data-driven campaigns.
Be cautious of unsolicited calls that:
- Create a way of urgency
- Request delicate or monetary info
- Stress you into speedy motion
Even when a caller seems credible, by no means share passwords, verification codes, or monetary particulars over the telephone.
If one thing feels off, the most secure method is straightforward: dangle up and speak to the group straight via official channels.
Lastly, enabling multi-factor authentication (MFA) can considerably scale back the affect of compromised credentials, including a vital layer of safety in opposition to account takeover.
How Flare Can Assist
Flare offers early visibility into fraud operations earlier than they attain victims. By monitoring underground boards, Telegram channels, and marketplaces, Flare detects leaked information, sufferer lists, and recruitment exercise tied to Caller-as-a-Service campaigns.
This enables organizations to proactively reply (reset credentials, alert customers, and strengthen defenses) earlier than attackers strike, decreasing each threat and affect.
Be taught extra by signing up for our free trial.
Sponsored and written by Flare.



