Microsoft says menace actors are more and more utilizing synthetic intelligence of their operations to speed up assaults, scale malicious exercise, and decrease technical boundaries throughout all features of a cyberattack.
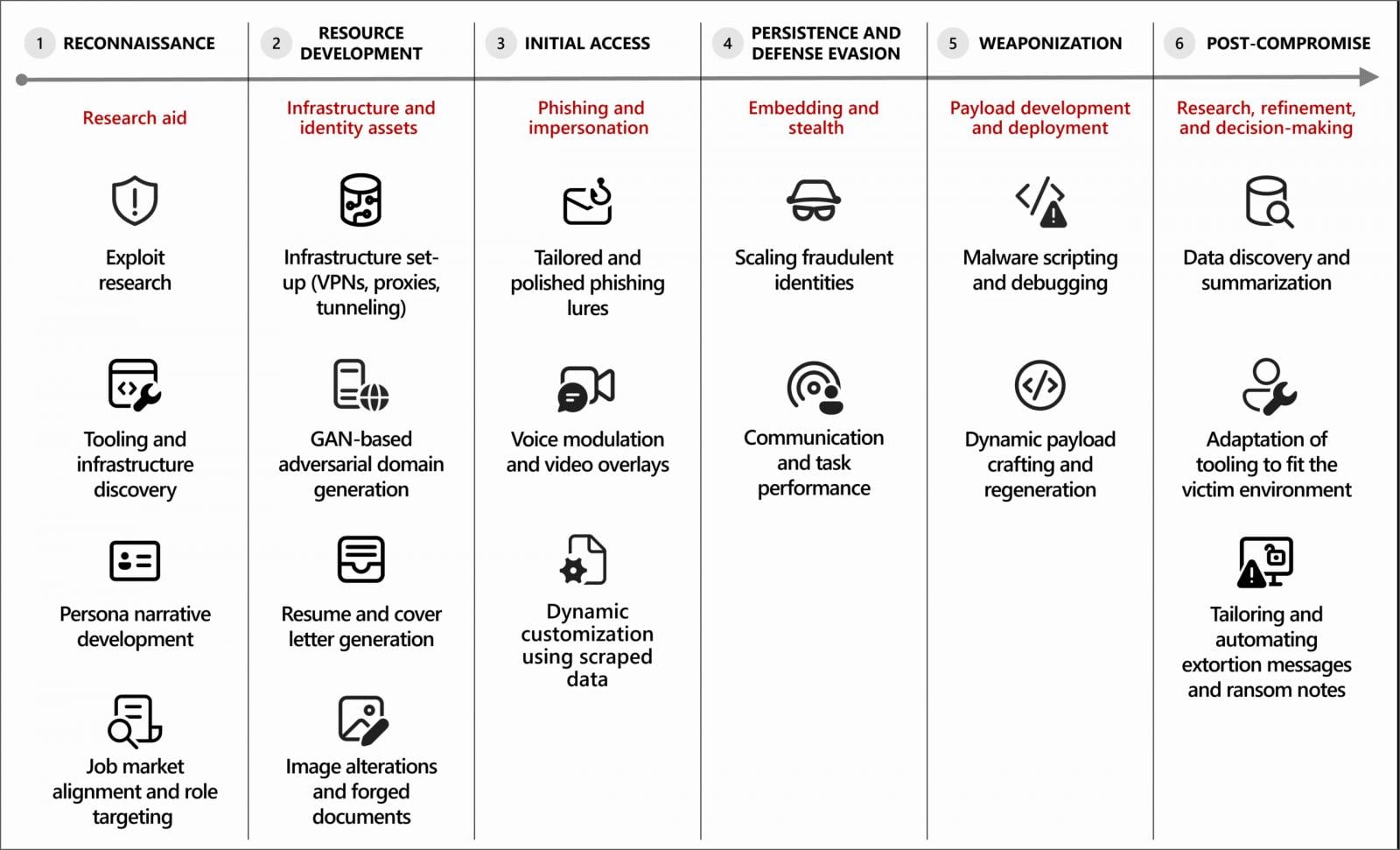
In response to a brand new Microsoft Menace Intelligence report, attackers are utilizing generative AI instruments for a variety of duties, together with reconnaissance, phishing, infrastructure growth, malware creation, and post-compromise exercise.
In lots of circumstances, AI is used to draft phishing emails, translate content material, summarize stolen information, debug malware, and help with scripting or infrastructure configuration.
“Microsoft Threat Intelligence has observed that most malicious use of AI today centers on using language models for producing text, code, or media. Threat actors use generative AI to draft phishing lures, translate content, summarize stolen data, generate or debug malware, and scaffold scripts or infrastructure,” warns Microsoft.
“For these uses, AI functions as a force multiplier that reduces technical friction and accelerates execution, while human operators retain control over objectives, targeting, and deployment decisions.”
Supply: Microsoft
AI used to energy cyberattacks
Microsoft has noticed a number of menace teams incorporating AI into their cyberattacks, together with North Korean actors tracked as Jasper Sleet (Storm-0287) and Coral Sleet (Storm-1877), who use the know-how as a part of distant IT employee schemes.
In these operations, AI instruments assist generate lifelike identities, resumes, and communications to realize employment at Western corporations and preserve entry as soon as employed.
Jasper Sleet leverages generative AI platforms to streamline the event of fraudulent digital personas. For instance, Jasper Sleet actors have prompted AI platforms to generate culturally applicable title lists and e-mail tackle codecs to match particular identification profiles. For instance, menace actors would possibly use the next forms of prompts to leverage AI on this state of affairs:
Instance immediate 1: “Create a list of 100 Greek names.”
Instance immediate 2: “Create a listing of e-mail tackle codecs utilizing the title Jane Doe.“
Jasper Sleet additionally makes use of generative AI to overview job postings for software program growth and IT-related roles on skilled platforms, prompting the instruments to extract and summarize required abilities. These outputs are then used to tailor faux identities to particular roles.
❖ Microsoft Menace Intelligence
The report additionally describes how AI is getting used to help with malware growth and infrastructure creation, with menace actors utilizing AI coding instruments to generate and refine malicious code, troubleshoot errors, or port malware elements to completely different programming languages.
Some malware experiments present indicators of AI-enabled malware that dynamically generate scripts or modify habits at runtime.
Microsoft additionally noticed Coral Sleet utilizing AI to shortly generate faux firm websites, provision infrastructure, and check and troubleshoot their deployments.
When AI safeguards try to stop the usage of AI in these duties, Microsoft says menace actors are utilizing jailbreaking methods to trick LLMs into producing malicious code or content material.
Along with generative AI use, Microsoft researchers have begun to see menace actors experiment with agentic AI to carry out duties autonomously and adapt to outcomes.
Nevertheless, Microsoft says AI is at present used primarily for decision-making relatively than for autonomous assaults.
As a result of many IT employee campaigns depend on the abuse of professional entry, Microsoft advises organizations to deal with these schemes and related exercise as insider dangers.
Moreover, as these AI-powered assaults mirror typical cyberattacks, defenders ought to deal with detecting irregular credential use, hardening identification programs towards phishing, and securing AI programs which will change into targets in future assaults.
Microsoft is just not alone in seeing menace actors more and more utilizing synthetic intelligence to energy assaults and decrease boundaries to entry.
Google lately reported that menace actors are abusing Gemini AI throughout all levels of cyberattacks, mirroring what Amazon noticed on this marketing campaign.
Amazon and the Cyber and Ramen safety weblog additionally lately reported on a menace actor utilizing a number of generative AI providers as a part of a marketing campaign that breached greater than 600 FortiGate firewalls.

Malware is getting smarter. The Pink Report 2026 reveals how new threats use math to detect sandboxes and conceal in plain sight.
Obtain our evaluation of 1.1 million malicious samples to uncover the highest 10 methods and see in case your safety stack is blinded.



