Cybersecurity researchers have found 5 malicious Rust crates that masquerade as time-related utilities to transmit .env file knowledge to the risk actors.
The Rust packages, printed to crates.io, are listed beneath –
- chrono_anchor
- dnp3times
- time_calibrator
- time_calibrators
- time-sync
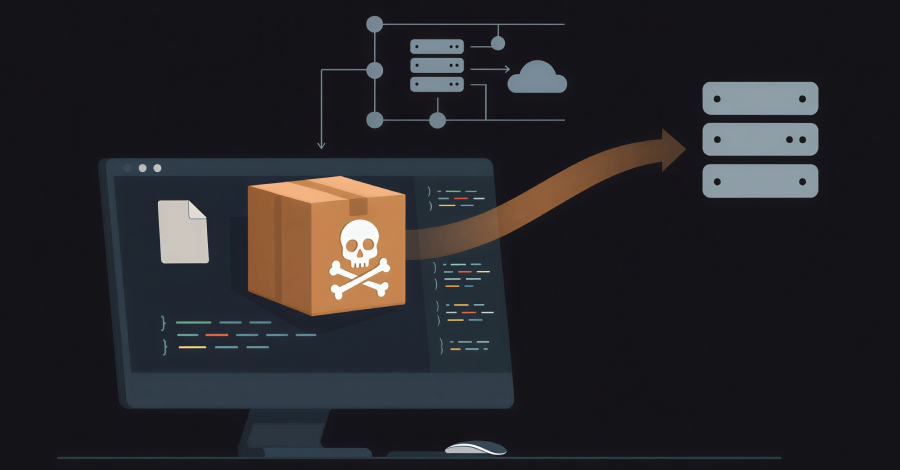
The crates, per Socket, impersonate timeapi.io and had been printed between late February and early March 2026. It is assessed to be the work of a single risk actor primarily based on using the identical exfiltration methodology and the lookalike area (“timeapis[.]io”) to stash the stolen knowledge.
“Although the crates pose as local time utilities, their core behavior is credential and secret theft,” safety researcher Kirill Boychenko mentioned. “They attempt to collect sensitive data from developer environments, most notably .env files, and exfiltrate it to threat actor-controlled infrastructure.”
Whereas 4 of the aforementioned packages exhibit pretty simple capabilities to exfiltrate .env recordsdata, “chrono_anchor” goes a step additional by implementing obfuscation and operational adjustments in order to keep away from detection. The crates had been marketed as a strategy to calibrate native time with out counting on the Community Time Protocol (NTP).
“Chrono_anchor” incorporates the exfiltration logic inside a file named “guard.rs” that is invoked from an “optional sync” helper operate in order to keep away from elevating developer suspicions. Not like different malware, the code noticed on this case doesn’t goal to arrange persistence on the host via a service or scheduled job.
As an alternative, the crate makes an attempt to repeatedly exfiltrate .env secrets and techniques each time the developer of a Steady Integration (CI) workflow calls the malicious code.
The focusing on of .env recordsdata isn’t any accident, because it’s sometimes used to carry API keys, tokens, and different secrets and techniques, permitting an attacker to compromise downstream customers and achieve deeper entry to their environments, together with cloud providers, databases, and GitHub and registry tokens.
Whereas the packages have since been faraway from crates.io, customers who might have by accident downloaded them are suggested to imagine attainable exfiltration, rotate keys and tokens, audit CI/CD jobs that run with publish or deploy credentials, and restrict outbound community entry the place attainable.
“This campaign shows that low-complexity supply chain malware can still deliver high-impact when it runs inside developer workspaces and CI jobs,” Socket mentioned. “Prioritize controls that stop malicious dependencies before they execute.”
AI-Powered Bot Exploits GitHub Actions
The disclosure follows the invention of an automatic assault marketing campaign that focused CI/CD pipelines spanning main open-source repositories, with a synthetic intelligence (AI)-powered bot known as hackerbot-claw scanning public repositories for exploitable GitHub Actions workflows to reap developer secrets and techniques.
Between February 21 and February 28, 2026, the GitHub account, which described itself as an autonomous safety analysis agent, focused at least seven repositories belonging to Microsoft, Datadog, and Aqua Safety, amongst others.
The assault unfolds as follows –
- Scan public repositories for misconfigured CI/CD pipelines
- Fork goal repository and prepared a malicious payload
- Open a pull request with a trivial change resembling a typo repair, whereas concealing the primary payload within the department title, file title, or a CI script
- Set off the CI pipeline by profiting from the truth that workflows are routinely activated on each pull request, inflicting the malicious code to be executed on the construct server
- Steal secrets and techniques and entry tokens
One of many highest-profile targets of the assault was the repository “aquasecurity/trivy,” a well-liked safety scanner from Aqua Safety that searches for recognized vulnerabilities, misconfigurations, and secrets and techniques.
“Hackerbot-claw exploited a pull_request_target workflow to steal a Personal Access Token (PAT),” provide chain safety firm StepSecurity mentioned. “The stolen credential was then used to take over the repository.”
In an announcement issued final week, Aqua Safety’s Itay Shakury revealed that the attacker leveraged the GitHub Actions workflow to push a malicious model of Trivy’s Visible Studio Code (VS Code) extension to the Open VSX registry to leverage native AI coding brokers to gather and exfiltrate delicate info.
Socket, which additionally investigated the extension compromise, mentioned the injected logic in variations 1.8.12 and 1.8.13 executes native AI coding assistants, together with Claude, Codex, Gemini, GitHub Copilot CLI, and Kiro CLI, in extremely permissive modes, instructing them to carry out in depth system inspection, generate a report of found info, and save the outcomes to a GitHub repository named “posture-report-trivy” utilizing the sufferer’s personal authenticated GitHub CLI session.
Aqua has since eliminated the artifacts from {the marketplace} and revoked the token used to publish them. Customers who put in the extensions are suggested to instantly take away them, test for the presence of surprising repositories, and rotate setting secrets and techniques. The malicious artifact has been eliminated. No different affected artifacts have been recognized. The incident is being tracked below the CVE identifier CVE-2026-28353.
It is price declaring that for a system to be impacted by the difficulty, the next stipulations have to be fulfilled –
- Model 1.8.12 or 1.8.13 was put in from Open VSX
- No less than one of many focused AI coding CLIs was put in regionally
- The CLI accepted the permissive execution flags offered
- The agent was in a position to entry delicate knowledge on disk
- The GitHub CLI was put in and authenticated (for model 1.8.13)
“The progression from .12 to .13 looks like iteration,” Socket mentioned. “The first prompt scatters data across random channels with no reliable way for the attacker to collect the output. The second fixes that problem by using the victim’s own GitHub account as a clean exfiltration channel, but its vague instructions might cause the agent to push secrets to a private repo the attacker can’t see.”