Written by Ivan Milenkovic, Vice President Danger Expertise EMEA, Qualys
For the higher a part of the final decade,we’ve got engaged in a cushty fiction round safety and growth. If we might solely “shift left” and get builders to take a modicum extra accountability for safety alongside their coding, testing and infrastructure deployment, the digital world would turn out to be a safer, sooner and cheaper place. As a substitute, the elemental battle between velocity and safety has bought worse.
Why did this fail? Builders are beneath crushing stress. The traditional triangle of venture administration – Quick, Good, Low-cost; decide two – has been smashed to items.
Companies demand quick, good, low-cost and safe. When push involves shove, “fast” all the time wins. On the identical time, we pushed an excessive amount of cognitive load onto builders who have been already drowning.
After they select to make use of public container photos to hurry up growth, they’re attempting to fulfill their targets, however they’re additionally open to potential threat. So how can we perceive what the actual drawback is, after which work to unravel that?
Enterprise calls for beat safety suggestions
There’s a pervasive narrative within the safety business that builders are lazy or careless. That is completely not true. Builders will not be lazy; they’re overloaded, pragmatic professionals reacting to the incentives positioned earlier than them. If their bonus relies on transport options by Friday and the safety scan takes 4 hours to run and blocks the construct, they are going to discover a manner across the scan.
Companies demand outcomes sooner and sooner, which has created an atmosphere the place safety protocols are seen as a barrier to productiveness fairly than an integral a part of engineering. When safety instruments are noisy, sluggish, and disconnected from the workflow, they’re a barrier.
Nevertheless, the results of that is that organisations have misplaced management of what’s truly operating of their environments. We’ve pipelines that deploy code routinely, infrastructure that scales up and down with out human intervention, and AI brokers that may now write and execute their very own scripts.
Into this high-speed, automated chaos, we deal with public registries like curated libraries, assuming that as a result of a picture is on Docker Hub, it have to be protected. However pulling a container from a public registry like Docker Hub is a belief resolution.
The likes of Docker, Amazon, Google and Microsoft all function public container registries, so there’s a pure assumption that they’re protected.
This belief is misplaced. By the point that container picture makes it to the deployment pipeline, it’s already a trusted artifact, baked into the appliance.
The 2026 Forrester Wave™ for Cloud-Native Utility Safety Platforms (CNAPP) offers goal evaluation round cloud safety.
Discover out why Qualys is without doubt one of the leaders out there right this moment.
Learn the White Paper
The 34,000 Picture Actuality Verify
Qualys Menace Analysis Unit (TRU) lately performed an exhaustive evaluation of over 34,000 container photos pulled from public repositories to see what is admittedly happening beneath the manifest.
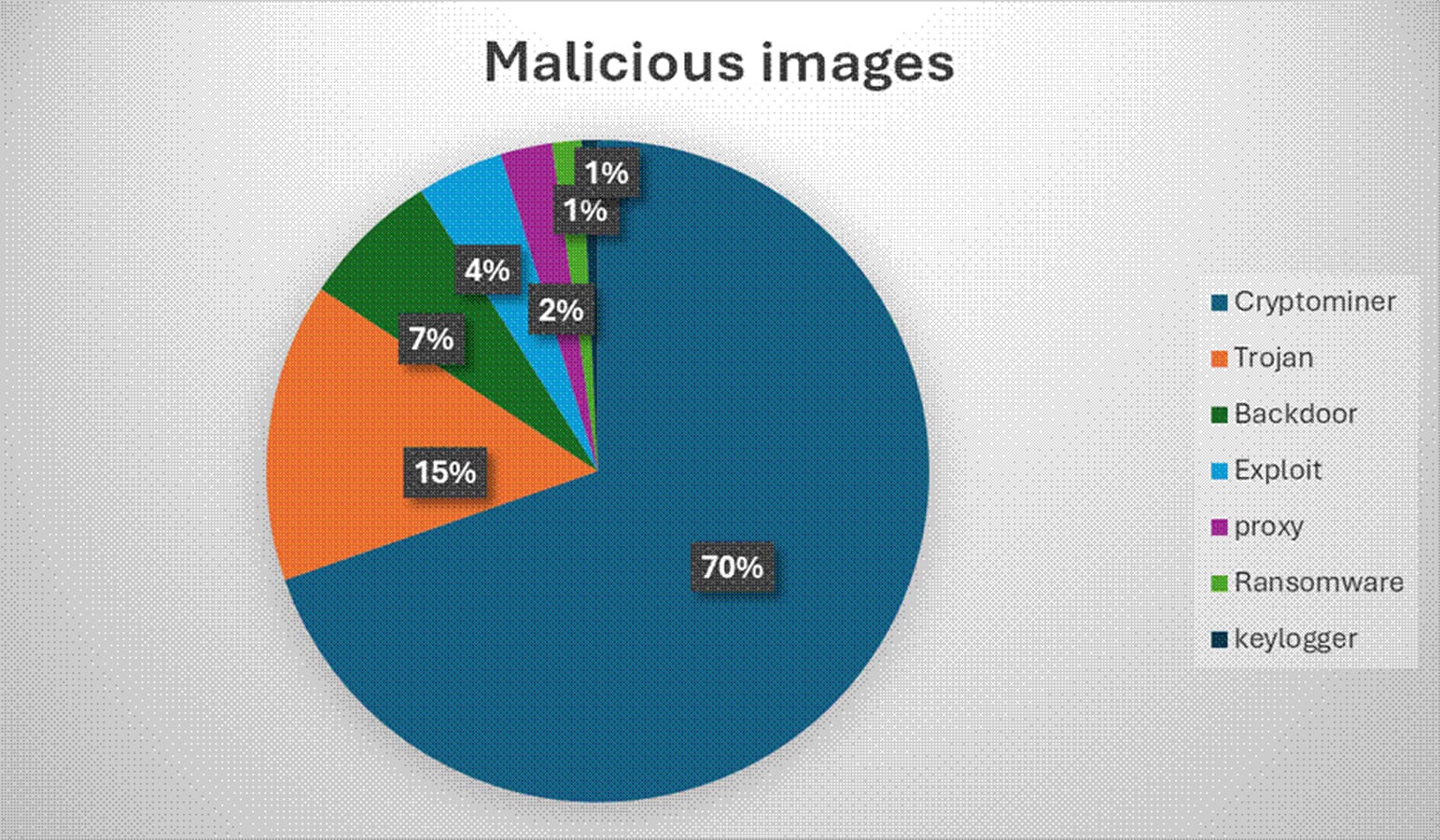
Of that complete, round 2,500 photos – roughly 7.3 % of the pattern – have been malicious. Of the malicious photos, 70 % contained cryptomining software program.
On high of this, 42 % of photos contained greater than 5 secrets and techniques that may very well be used to get entry to different sources or accounts. This contains useful objects like AWS entry keys, GitHub API tokens, and database credentials baked straight into the picture layers.
In our evaluation, the most important points round malicious containers are nonetheless quite simple. Typosquatting is without doubt one of the most typical strategies that attackers use to get their malicious containers downloaded. The usual recommendation to “check the spelling” is crucial, sure, however it is usually a low-energy response to a high-stakes drawback.
Telling a developer to “be more careful” shouldn’t be a safety technique. Whereas public registries are helpful for velocity, we shouldn’t be letting builders pull from public registries in any respect.
In a mature atmosphere, each exterior picture needs to be proxied via an inner artifact repository that acts as a quarantine zone. But that want for velocity shouldn’t be going to go away. As a substitute, we’ve got to work on tips on how to assist builders transfer sooner whereas maintaining safety in place.
This does imply extra work for the infrastructure group, however that work ought to allow builders to maneuver forward sooner and with much less threat.
Shift down
The logic is that it’s cheaper to repair a bug throughout design or coding than in manufacturing. Subsequently, shifting safety earlier within the Software program Improvement Life Cycle (SDLC) ought to scale back dangers later. Whereas this is sensible in principle, it asks builders to scan their very own code, test their very own dependencies, and handle their very own infrastructure.
In actuality, we simply shifted the ache onward. It asks builders to handle vulnerabilities, configuration hardening, secret detection, compliance auditing, and so forth. On the identical time, these builders are measured totally on characteristic velocity.
“Shift left” was purported to make safety collaborative. As a substitute, it merely moved the issue into each developer’s IDE. To repair this drawback, we’ve got to make safety inside infrastructure the default, fairly than by design.
This entails actual collaboration between builders and safety – builders have to know what they need to obtain and what might be required of what they construct, whereas safety must work round these necessities to allow them to be delivered securely. Each groups are accountable, however they each must work on the velocity that the enterprise wants.
In follow, we are able to create a “golden path” for builders. In the event that they use the usual templates, the pre-approved base photos, and the official CI pipelines, safety is free. In the event that they need to go “off-road” and construct one thing customized, then they must do the extra work of safety critiques and handbook configurations.
That is additionally one thing that needs to be flagged again to the enterprise from the beginning, so safety and growth current a united entrance round what the fee is.
Taking this method incentivises safe deployment by making it the trail of least resistance. It strikes the accountability down the stack to the infrastructure layer, managed by a specialised Platform Engineering group. And if one thing totally different is required, that work could be executed collaboratively to make sure it’s proper first time, fairly than resulting in extra points that must be remediated.
For instance, as an alternative of asking a developer to please allow versioning on a selected S3 bucket, the platform group writes a coverage utilizing Terraform modules, Crossplane compositions, or Open Coverage Agent that merely would not permit a bucket to exist with out versioning. The developer actually can not make the error.
The platform corrects it routinely or rejects the request. Equally, builders should not have to recollect container scanning of their workflows, the CI pipeline ought to do it routinely. The admission controller ought to reject non-compliant photos earlier than they ever hit a cluster. The developer would not must know the way the scan works, solely that in the event that they attempt to deploy a essential vulnerability, the door might be locked.
“Shift down” additionally means automating the repair. For example if a vulnerability is present in a base picture, the platform ought to routinely generate a Pull Request to improve it. If a runtime safety device detects a container behaving badly (e.g., spawning a shell for persistence), it should not simply ship an alert. It ought to kill the pod and isolate the node autonomously.
Relatively than sticking with present methods of operating throughout safety and growth, we’ve got to react to what’s taking place. This may imply we essentially change how we function throughout groups.
If we proceed with the “shift left” mentality of piling cognitive load onto builders, we are going to fail. We’ll burn them out, and they’re going to bypass our controls merely to allow them to get what must be executed for the enterprise.
As a substitute, safety needs to be proactive round tips on how to implement and help the proper platforms for the enterprise, to allow them to be made safe routinely.
Sponsored and written by Qualys.



