A newly found and complicated Android malware referred to as Keenadu has been discovered embedded in firmware from a number of machine manufacturers, enabling it to compromise all put in purposes and acquire unrestricted management over contaminated gadgets.
In line with a report from cybersecurity firm Kaspersky, Keenadu has a number of distribution mechanisms, together with compromised firmware photographs delivered over-the-air (OTA), through different backdoors, embedded in system apps, modified apps from unofficial sources, and even by apps on Google Play.
There are a number of variants of Keenadu, every with its personal set of capabilities, essentially the most potent of them being the firmware-based model.

As of February 2026, Kaspersky has confirmed 13,000 contaminated gadgets, many situated in Russia, Japan, Germany, Brazil, and the Netherlands.
The safety researchers evaluate Keenadu to Triada, one other Android malware household they noticed in counterfeit Android gadgets final yr, largely low-cost telephones that undergo shady provide chain routes.
In its firmware-integrated variant, Keenadu doesn’t activate if the language or timezone is related to China, which can signify a possible clue about its origin. The malware additionally stops if the Google Play Retailer and Play Providers aren’t discovered on the machine.
Though its operators are at the moment centered on advert fraud operations, Kaspersky notes that the malware’s capabilities go far past, as it’s able to broad-range knowledge theft and dangerous actions on the compromised machine.
.png)
“Keenadu is a fully functional backdoor that provides the attackers with unlimited control over the victim’s device,” Kaspersky informed BleepingComputer.
“It can infect every app installed on the device, install any apps from APK files, and give them any available permissions.”
“As a result, all information on the device, including media, messages, banking credentials, location, etc. can be compromised. The malware even monitors search queries that the user inputs into the Chrome browser in incognito mode,” the researchers stated.
The Keenadu variant embedded in system apps is extra restricted in performance. Nevertheless, its elevated privileges enable it to put in any app with out alerting the consumer.
Kaspersky researchers discovered the malware embedded in a system app for facial recognition, sometimes used for unlocking the machine and numerous authorization and authentication actions.
The researchers additionally discovered the malware on Google Play, in good residence digital camera apps that had 300,000 downloads, that are not out there within the official Android retailer.
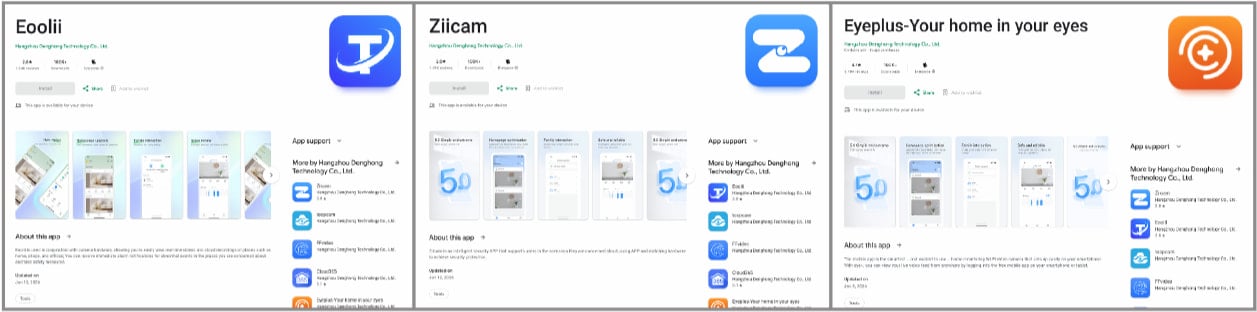
Supply: Kaspersky
When opened, the apps launched invisible internet browser tabs inside the host app, which navigated to web sites within the background. Kaspersky notes that this resembles comparable exercise to APKs found by Dr.Net earlier this yr.
In line with the researchers, Keenadu is current within the firmware of Android tablets from a number of makers. On one product, the Alldocube iPlay 50 mini Professional (T811M) pill, the malicious firmware was dated August 18, 2023.
After a buyer in March 2024 said that Alldocube’s OTA server had been compromised and a risk actor inserted malware within the firmware, the firm acknowledged “a virus attack through OTA software” however didn’t present info on the kind of risk.
Kaspersky revealed an in depth technical evaluation for the Keenadu backdoor, explaining how the malware compromised the libandroid_runtime.so part, a core library within the Android system, which permits the malware to function “within the context of every app on the device.”
The researchers warn that as a result of the malware is embedded so deeply within the firmware, it’s unimaginable to take away it utilizing normal Android OS instruments. They advocate customers to seek out and set up a clear firmware model for his or her machine.
An alternate is to put in firmware from a good third-party, though this comes with the potential danger of bricking the machine in case of incompatibility.
One of many most secure choices is to cease utilizing the machine and change it with a product from trusted distributors and licensed distributors.
Replace 2/18 – Google confirmed to BleepingComputer through an announcement that the malicious apps have been faraway from Google Play.
“Android users are automatically protected from known versions of this malware by Google Play Protect, which is on by default on Android devices with Google Play Services. Google Play Protect can warn users and disable apps known to exhibit Keenadu associated behavior, even when those apps come from sources outside of Play. As a best security practice, we recommend users ensure their device is Play Protect certified.” – A Google spokesperson

Trendy IT infrastructure strikes quicker than handbook workflows can deal with.
On this new Tines information, learn the way your group can cut back hidden handbook delays, enhance reliability by automated response, and construct and scale clever workflows on high of instruments you already use.



