For the previous week, the huge “Internet of Things” (IoT) botnet often called Kimwolf has been disrupting The Invisible Web Challenge (I2P), a decentralized, encrypted communications community designed to anonymize and safe on-line communications. I2P customers began reporting disruptions within the community across the identical time the Kimwolf botmasters started counting on it to evade takedown makes an attempt in opposition to the botnet’s management servers.
Kimwolf is a botnet that surfaced in late 2025 and rapidly contaminated hundreds of thousands of programs, turning poorly secured IoT units like TV streaming packing containers, digital image frames and routers into relays for malicious site visitors and abnormally massive distributed denial-of-service (DDoS) assaults.
I2P is a decentralized, privacy-focused community that permits individuals to speak and share info anonymously.
“It works by routing data through multiple encrypted layers across volunteer-operated nodes, hiding both the sender’s and receiver’s locations,” the I2P web site explains. “The result is a secure, censorship-resistant network designed for private websites, messaging, and data sharing.”
On February 3, I2P customers started complaining on the group’s GitHub web page about tens of 1000’s of routers immediately overwhelming the community, stopping current customers from speaking with professional nodes. Customers reported a quickly growing variety of new routers becoming a member of the community that had been unable to transmit knowledge, and that the mass inflow of latest programs had overwhelmed the community to the purpose the place customers might now not join.
I2P customers complaining about service disruptions from a quickly growing variety of routers immediately swamping the community.
When one I2P consumer requested whether or not the community was below assault, one other consumer replied, “Looks like it. My physical router freezes when the number of connections exceeds 60,000.”
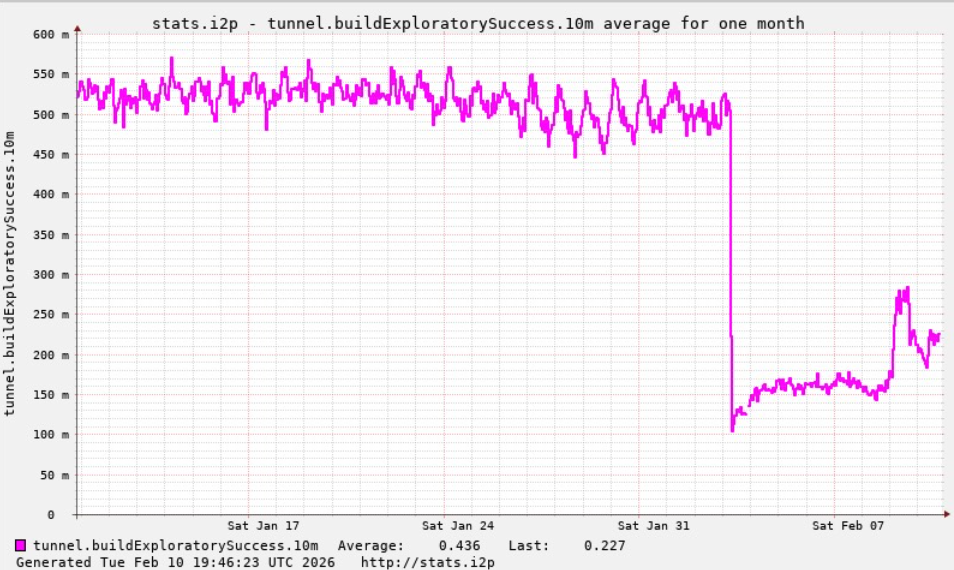
A graph shared by I2P builders exhibiting a marked drop in profitable connections on the I2P community across the time the Kimwolf botnet began making an attempt to make use of the community for fallback communications.
The identical day that I2P customers started noticing the outages, the people in command of Kimwolf posted to their Discord channel that that they had unintentionally disrupted I2P after making an attempt to affix 700,000 Kimwolf-infected bots as nodes on the community.
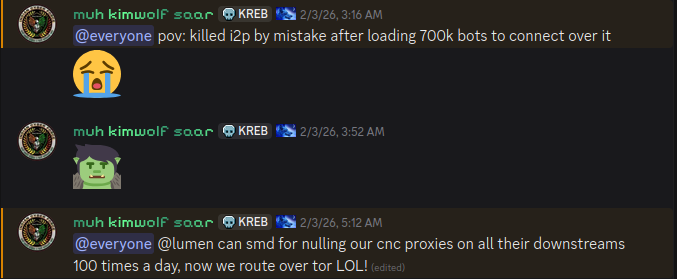
The Kimwolf botmaster brazenly discusses what they’re doing with the botnet in a Discord channel with my identify on it.
Though Kimwolf is called a potent weapon for launching DDoS assaults, the outages prompted this week by some portion of the botnet making an attempt to affix I2P are what’s often called a “Sybil attack,” a risk in peer-to-peer networks the place a single entity can disrupt the system by creating, controlling, and working a lot of faux, pseudonymous identities.
Certainly, the variety of Kimwolf-infected routers that attempted to affix I2P this previous week was many occasions the community’s regular measurement. I2P’s Wikipedia web page says the community consists of roughly 55,000 computer systems distributed all through the world, with every participant appearing as each a router (to relay site visitors) and a shopper.
Nevertheless, Lance James, founding father of the New York Metropolis primarily based cybersecurity consultancy Unit 221B and the unique founding father of I2P, informed KrebsOnSecurity all the I2P community now consists of between 15,000 and 20,000 units on any given day.
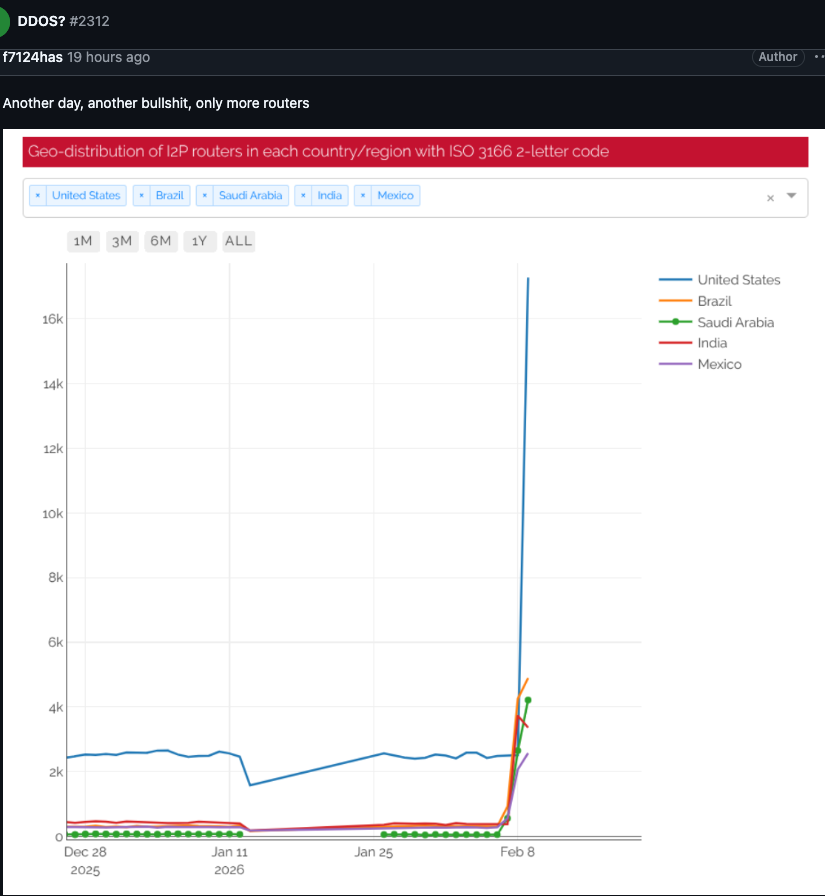
An I2P consumer posted this graph on Feb. 10, exhibiting tens of 1000’s of routers — largely from the US — immediately making an attempt to affix the community.
Benjamin Brundage is founding father of Synthient, a startup that tracks proxy companies and was the primary to doc Kimwolf’s distinctive spreading strategies. Brundage mentioned the Kimwolf operator(s) have been making an attempt to construct a command and management community that may’t simply be taken down by safety firms and community operators which are working collectively to fight the unfold of the botnet.
Brundage mentioned the individuals in command of Kimwolf have been experimenting with utilizing I2P and the same anonymity community — Tor — as a backup command and management community, though there have been no stories of widespread disruptions within the Tor community not too long ago.
“I don’t think their goal is to take I2P down,” he mentioned. “It’s more they’re looking for an alternative to keep the botnet stable in the face of takedown attempts.”
The Kimwolf botnet created challenges for Cloudflare late final 12 months when it started instructing hundreds of thousands of contaminated units to make use of Cloudflare’s area identify system (DNS) settings, inflicting management domains related to Kimwolf to repeatedly usurp Amazon, Apple, Google and Microsoft in Cloudflare’s public rating of essentially the most ceaselessly requested web sites.
James mentioned the I2P community remains to be working at about half of its regular capability, and {that a} new launch is rolling out which ought to deliver some stability enhancements over the subsequent week for customers.
In the meantime, Brundage mentioned the excellent news is Kimwolf’s overlords seem to have fairly not too long ago alienated a few of their extra competent builders and operators, resulting in a rookie mistake this previous week that prompted the botnet’s general numbers to drop by greater than 600,000 contaminated programs.
“It seems like they’re just testing stuff, like running experiments in production,” he mentioned. “But the botnet’s numbers are dropping significantly now, and they don’t seem to know what they’re doing.”



