Fashionable infostealers have expanded credential theft far past usernames and passwords. Over the previous 12 months, campaigns have accelerated, concentrating on customers with little distinction between company workers and people on private gadgets.
These infections routinely harvest credentials alongside broader session knowledge and consumer exercise. The ensuing datasets are aggregated and offered by preliminary entry brokers, then reused throughout assaults concentrating on each private and enterprise environments.
To raised perceive the scope and implications of this exercise, Specops researchers analyzed greater than 90,000 leaked infostealer dumps, comprising over 800 million rows of knowledge collected throughout energetic infections.
The datasets included credentials, browser cookies, searching historical past, and system-level recordsdata saved domestically on compromised machines.
What emerges is a transparent image of how infostealer dumps permit attackers to affiliate technical knowledge with actual customers, organizations, and behavioral patterns, making a single an infection helpful lengthy after the preliminary compromise.
When stolen credentials change into identification knowledge
The most important danger is how simply infostealer knowledge ties a number of accounts and behaviors again to 1 actual individual. These dumps routinely expose reused account names throughout providers, Home windows usernames, recordsdata saved in consumer directories, energetic session knowledge, and detailed information of exercise throughout environments.
Mixed, these alerts let attackers transfer from a single compromised credential to figuring out a person, their employer, and probably their position inside a corporation.
This convergence collapses the boundary between private {and professional} identification that many safety fashions nonetheless assume exists. What could begin as a compromise on a private machine can rapidly escalate into enterprise-level danger.
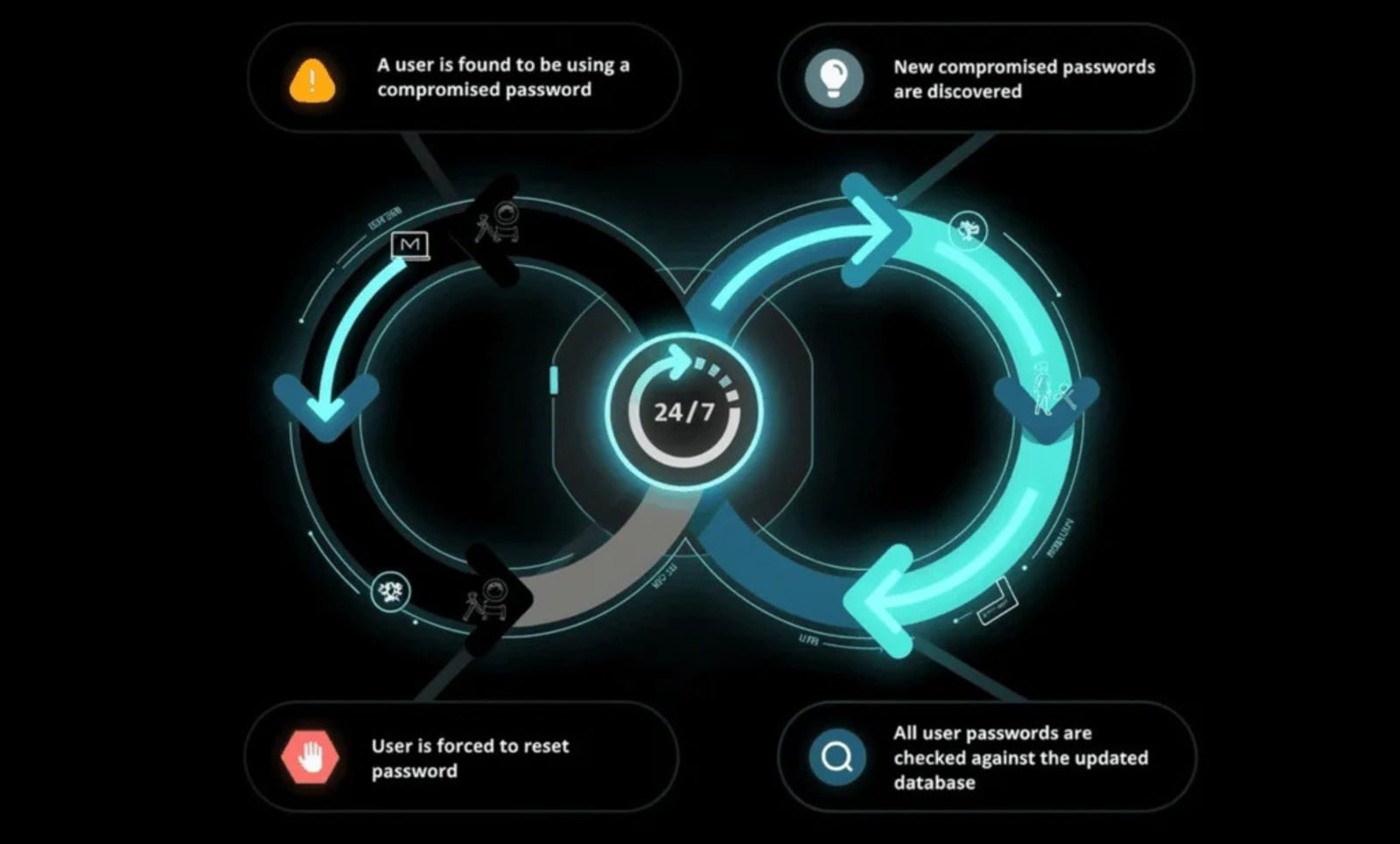
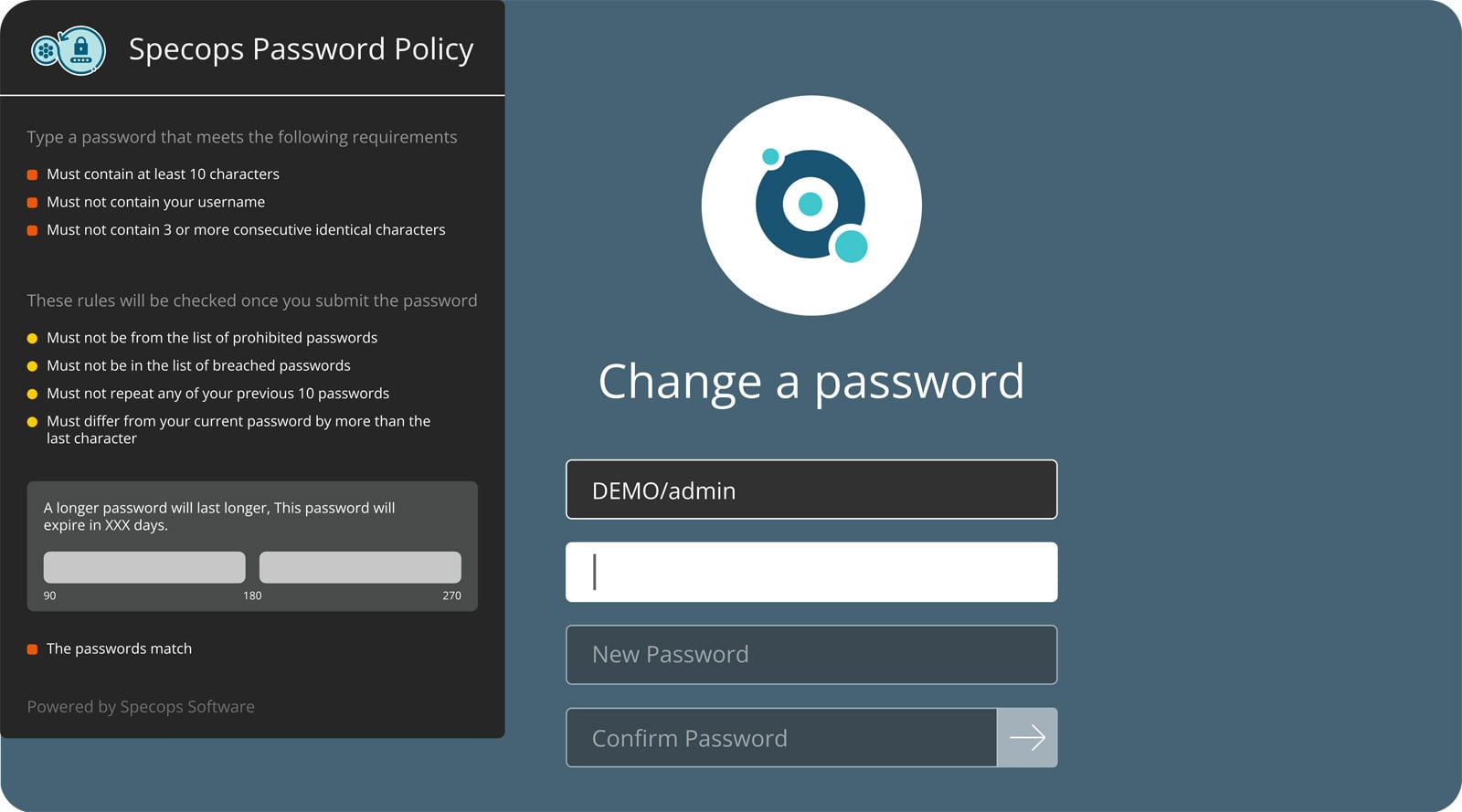
Specops Password Coverage helps organizations break this hyperlink by constantly scanning Lively Listing in opposition to a database of greater than 5.4 billion known-compromised credentials, moderately than solely checking passwords at creation or reset.
Credentials which have already been uncovered are blocked from being set or reused, even when they technically adjust to coverage, decreasing the danger of compromised passwords being reused throughout private and company accounts.
Verizon’s Information Breach Investigation Report discovered stolen credentials are concerned in 44.7% of breaches.
Effortlessly safe Lively Listing with compliant password insurance policies, blocking 4+ billion compromised passwords, boosting safety, and slashing assist hassles!
Strive it at no cost
The place infostealers get your knowledge and the way they abuse it
The dataset contained credentials and session knowledge related to a variety of providers, illustrating how infostealer knowledge exposes each identification and entry.
Skilled and enterprise-linked providers
LinkedIn, GitHub, Microsoft Groups, Outlook, and company domains appeared incessantly within the dataset. LinkedIn alone accounted for practically 900,000 information, offering a direct path from stolen knowledge to actual names, job titles, and organizational affiliations.
For menace actors, this info permits focused phishing, social engineering, and prioritization of entry which will lead deeper into enterprise environments, particularly the place password reuse exists.
Private identification and social platforms
YouTube, Fb, and related social media platforms additionally made high-volume appearances. These providers typically include actual names, pictures, and social connections, making it simpler to validate the identification of a compromised consumer and hyperlink them to different accounts.
This correlation makes focused exploitation far simpler.
Delicate and high-risk providers
The dataset additionally included credentials and cookies related to delicate providers, together with authorities and tax-related domains such because the IRS and the Canada Income Company, in addition to grownup content material platforms. Entry to those providers introduces dangers past conventional account takeover.
In earlier incidents, menace actors have used knowledge from grownup platforms as leverage for extortion and blackmail. When that exercise might be linked again to a person’s actual identification and employer, the potential influence escalates rapidly.
Safety-aware but nonetheless uncovered
Domains similar to Shodan and even mil.gov appeared throughout the dataset, reinforcing an uncomfortable actuality: technical consciousness doesn’t equal immunity.
Safe practices adopted in company environments don’t all the time lengthen to non-public techniques, but publicity on these techniques can nonetheless create enterprise danger.
Why infostealers stay so efficient
Infostealer publicity isn’t pushed by a single failure, however by a mixture of widespread behaviors repeated at scale. Customers set up purposes from illicit sources, reuse passwords throughout private and company accounts, and depend on browser-based credential storage for comfort.
Browser-stored credentials and cost knowledge are particularly helpful to attackers.
When an infostealer compromises a system, these shops present attackers with rapid entry to high-value info, considerably rising the influence of a single an infection.
Lowering influence after credential theft
As soon as infostealer knowledge has been collected and circulated, prevention is now not the one problem. The true query is how rapidly defenders can neutralize it earlier than it’s reused for lateral motion, account takeover, or ransomware deployment.
As a result of infostealer dumps typically flow into for weeks or months earlier than detection, efficient mitigation should assume that some credentials are already uncovered.
Password reuse stays one of the dependable methods attackers operationalize infostealer knowledge. Credentials harvested from private gadgets are routinely examined in opposition to company environments, cloud providers, and distant entry techniques, typically with success even when these passwords meet customary complexity necessities.
Disrupting reuse immediately reduces the operational worth of infostealer datasets and shortens their window of exploitation.
Mixed with stronger password insurance policies that assist longer passphrases and steady enforcement, these controls shift password safety from a static configuration train to an energetic containment measure.
Identification publicity more and more begins exterior the company perimeter, so decreasing the reuse and downstream influence of stolen credentials stays one of the efficient methods to interrupt infostealer-driven assault chains.
To see how Specops Password Coverage helps block compromised passwords and cut back credential reuse in Lively Listing, request a stay demo from a Specops professional.
Sponsored and written by Specops Software program.



