The current breach of the European Fee’s cloud infrastructure was contained rapidly sufficient that Europa.eu web sites stayed on-line all through. By most seen measures, it regarded like a restricted incident. The forensic image that has emerged since tells a distinct story.
CERT-EU printed its technical breakdown on April 3. Attackers acquired an AWS API key on March 19 via the Trivy provide chain compromise–a safety scanner the Fee was operating as a part of its cloud tooling. That single compromised key granted management over different AWS accounts affiliated with the Fee. From there, the attackers used TruffleHog to scan for extra secrets and techniques and validate credentials earlier than starting reconnaissance.
ShinyHunters, the group linked to current provide chain assaults throughout a number of instruments, has since been confirmed as accountable. Roughly 340GB of information was stolen and subsequently leaked. What made the breach doable was not a niche within the Fee’s perimeter.
It was the complexity of its cloud atmosphere, the sprawl of instruments, accounts, and credential dependencies that, when one ingredient is compromised, can cascade throughout the remainder. The Fee had a safety scanner. That scanner was compromised. The scanner had entry to API keys.
These keys had entry to different accounts. The investigation discovered no proof of lateral motion between accounts, however the pathway existed. That is exactly the structural drawback of the 2026 State of Cloud Safety Report, sponsored by Fortinet and produced by Cybersecurity Insiders from a survey of 1,163 safety professionals worldwide, which was described three months in the past, earlier than the Fee breach occurred.
The anatomy of a complexity hole
The Fortinet-sponsored report recognized what it calls a cloud safety complexity hole: not a funding shortfall, not a know-how failure, however a structural mismatch between how briskly cloud environments develop and the way properly safety groups can truly see and management them.
Virtually 70% of organisations cite device sprawl and visibility gaps as the highest boundaries to efficient cloud safety. Safety options have expanded alongside cloud adoption, however incessantly with out coordination, leading to disconnected instruments, inconsistent controls, and restricted end-to-end visibility.
Groups are pressured to manually correlate alerts from programs that weren’t designed to work collectively. The Fee breach matches this sample exactly. A 3rd-party safety device sitting contained in the cloud atmosphere, with the credentials wanted to do its job, grew to become the entry level.
The device was doing what it was imagined to do. The issue was that no person had a full image of what that device might attain. 88% of organisations now function in hybrid or multi-cloud environments, up from 82% the earlier yr. Amongst them, 81% depend on two or extra cloud suppliers for crucial workloads, and 29% are utilizing greater than three.
Every extra supplier, service, and power creates new credential dependencies and permission paths. The infrastructure scales by design. The assault floor scales with it.
Stretched groups, machine-speed threats
The Fortinet report identifies two additional reinforcing elements behind the complexity hole. 74% of these surveyed report an lively scarcity of certified cybersecurity professionals, whereas 59% say their organisations are nonetheless within the early levels of cloud safety maturity. Understaffed groups managing overcomplicated environments are slower to detect anomalies and slower nonetheless to hint them throughout disconnected programs.
The Fee’s Cybersecurity Operations Centre detected uncommon API exercise on March 24. However the preliminary entry had occurred 5 days earlier, on March 19. The breach was detected by the EC’s safety operations centre on March 24, and CERT-EU was notified on March 25. 5 days of undetected entry in a cloud atmosphere the place credential misuse had already begun.
The hole between intrusion and detection is just not a failure of effort; it’s what occurs when environments are complicated sufficient that ordinary appears to be like indistinguishable from irregular till one thing flags it.
Risk actors are using automation to uncover misconfigurations, map permission paths, and establish uncovered information quicker than human-led defences can reply. 66% of cybersecurity professionals say they lack sturdy confidence of their potential to detect and reply to cloud threats in actual time.
Extra instruments, not higher outcomes
The instinctive response to a breach like that is so as to add extra monitoring, extra scanning, extra tooling. The Fortinet report suggests this response is a part of the issue it’s meant to resolve.
When requested how they’d design their cloud safety technique if ranging from scratch, 64% of respondents mentioned they’d construct round a single-vendor platform unifying community, cloud, and software safety–not due to vendor choice, however as a result of the combination overhead of managing a number of disconnected instruments is itself a safety legal responsibility. Each extra device is one other credential. One other permission set. One other potential Trivy.
The Fee breach is just not an outlier that reveals a novel institutional vulnerability. It’s an illustration of situations that the Fortinet information suggests exist throughout the vast majority of enterprise cloud environments proper now. The complexity is the chance. And the complexity continues to be rising.
Fortinet shall be exhibiting on the Cybersecurity & Cloud Expo at TechEx North America, going down 18–19 Might 2026 on the San Jose McEnery Conference Centre.
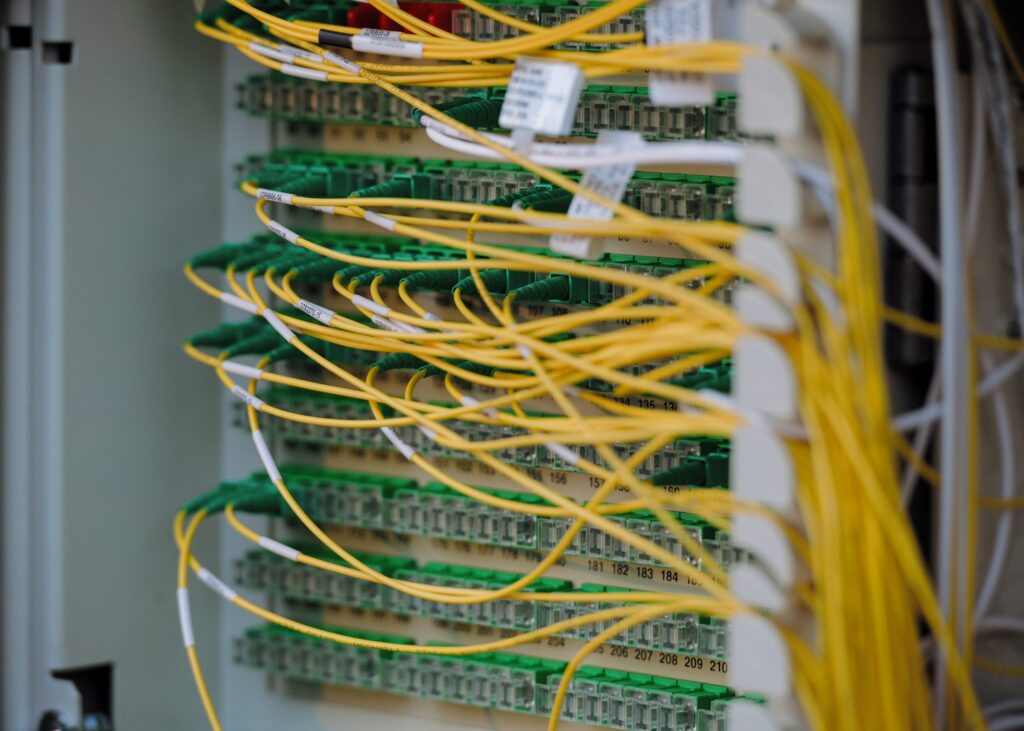
(Photograph by Albert Stoynov)
See additionally: 10 real-life cloud safety failures and what we will study from them

Wish to study extra about Cloud Computing from trade leaders? Take a look at Cyber Safety & Cloud Expo going down in Amsterdam, California, and London. The excellent occasion is a part of TechEx and is co-located with different main know-how occasions, click on right here for extra info.
CloudTech Information is powered by TechForge Media. Discover different upcoming enterprise know-how occasions and webinars right here.