A safety researcher has printed detailed proof exhibiting that some Instagram personal profiles returned hyperlinks to consumer photographs to unauthenticated guests.
Instagram’s personal account characteristic is designed to limit photographs, movies, tales, and reels to authorised followers. Nonetheless, the researcher’s findings present that, in sure circumstances, personal profile content material was embedded in publicly accessible server responses.
Based on the researcher, Meta fastened the difficulty after his report was submitted however later closed it as “not relevant,” stating the vulnerability couldn’t be reproduced.

Personal Instagram profiles leaking photographs
Safety researcher Jatin Banga has not too long ago demonstrated how sure personal Instagram profiles had been leaking hyperlinks to non-public photographs from these accounts—within the HTML response physique itself.
When accessed by an unauthenticated consumer from sure cell units, personal Instagram profiles (such because the researcher-created https://instagram.com/jatin.py) show the usual message: “This account is personal. Comply with to see their photographs and movies.”

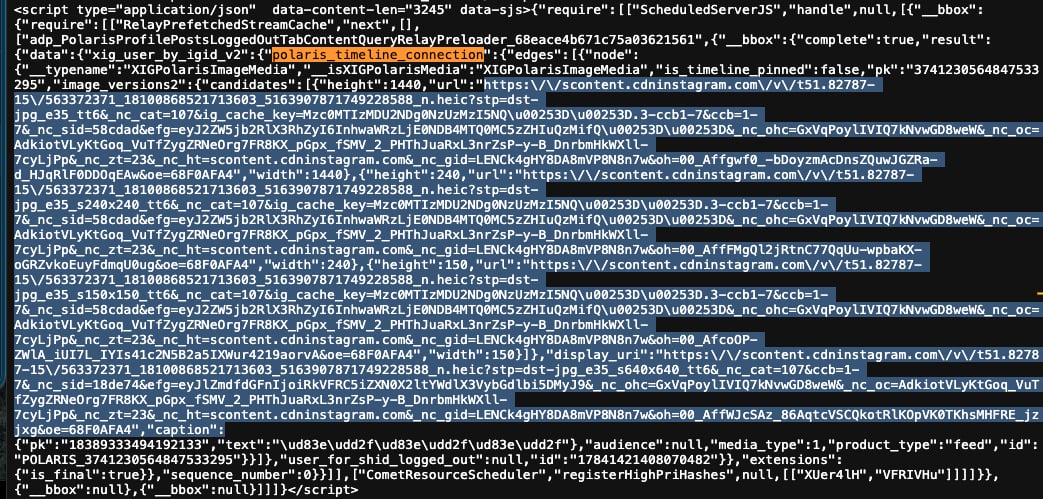
Nonetheless, within the HTML supply code for affected profiles, hyperlinks to some personal photographs in addition to captions had been embedded within the web page response.
In Banga’s instance, the polaris_timeline_connection JSON object returned within the HTML contained encoded CDN hyperlinks to photographs that ought to not have been accessible.
The video proof-of-concept (PoC) shared by Banga and embedded beneath demonstrates the info leak vulnerability in motion.
By limiting the formal testing to non-public check profiles Banga had created or had express permission to make use of, he discovered that a minimum of 28% of those accounts had been returning captions and hyperlinks to non-public photographs:
Meta quietly fastened the difficulty after report, researcher says
The researcher states that he shared his findings with Instagram’s guardian firm, Meta, as early as October 12, 2025.
Meta initially categorised the difficulty as a CDN caching downside, a characterization the researcher disputed.
“This wasn’t a CDN caching subject — Instagram’s backend was failing to test authorization earlier than populating the response,” Banga wrote, describing it as a server-side authorization failure.
Banga created a second bug report clarifying the difficulty, however didn’t attain a passable decision with the corporate regardless of a prolonged dialogue spanning days.
Based on the researcher, after repeated exchanges, the case was closed as “not relevant” however the exploit stopped working round October 16.
“The usual coordinated disclosure window is 90 days. I gave Meta 102 days and a number of escalation makes an attempt. The exploit stopped engaged on all accounts I examined — although with out root trigger evaluation from Meta, there is not any affirmation the underlying subject is really resolved,” he continues.
Along with his disclosure and the GitHub repository documenting intensive proof of the flaw and communications with Meta, Banga shared extra supplies with BleepingComputer to reveal the existence of the flaw.
We requested Banga why he didn’t archive the check personal profile utilizing a public service just like the Web Archive’s Wayback Machine, which may have preserved the HTML supply code with the hyperlinks to non-public photographs current, thereby indisputably confirming the presence of a bug.
“The Wayback Machine does not ship the precise Cell Consumer-Agent and Headers required to set off this server-side leak, so their crawlers could not seize it,” the researcher clarified to BleepingComputer.
Within the printed correspondence, a Meta vulnerability triage analyst wrote:
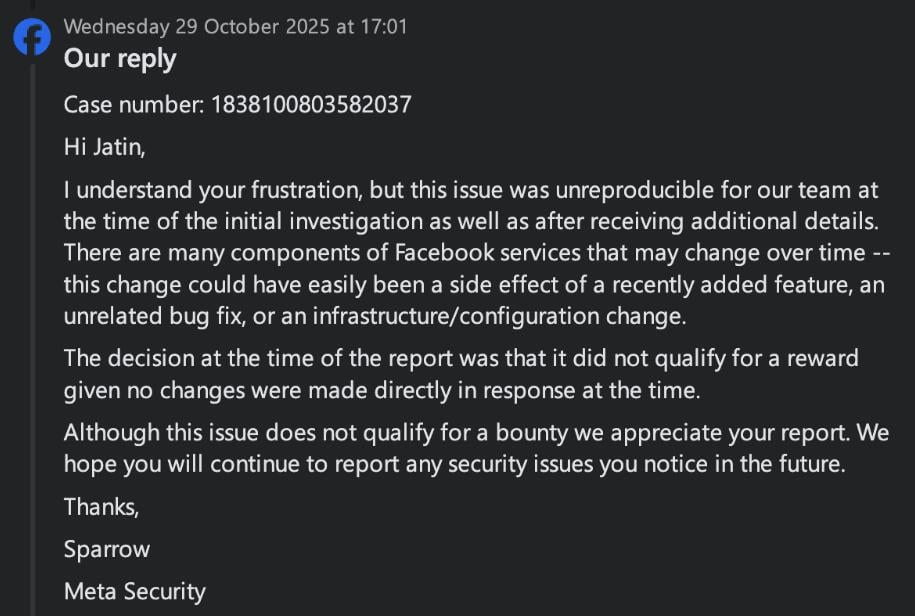
Finally, throughout the course of the dialog, the analyst is seen stating:
“The truth that an unreproducible subject was fastened does not change the truth that it was not reproducible on the time. Even when the difficulty had been reproducible, it is doable {that a} change was made to repair a unique subject and this subject was fastened as an unintended aspect impact.”
“I wish to emphasize that I’m not chasing a bounty right here. By going public with this disclosure, I’ve forfeited any probability of a reward,” Banga advised BleepingComputer by way of electronic mail.
“The objective is transparency. Meta patched a vital privateness leak 48-96 hours after my report however refused to acknowledge it, dismissing it as an ‘unintended aspect impact.’ Their negligence and reluctance to analyze the precise root trigger—regardless of having the logs—is the actual subject.”
“No person is aware of how lengthy this has been really exploited for, because it was not so exhausting to search out.”
BleepingComputer contacted Meta for touch upon three separate events effectively prematurely of publication however didn’t obtain a response.

Trendy IT infrastructure strikes sooner than handbook workflows can deal with.
On this new Tines information, learn the way your workforce can cut back hidden handbook delays, enhance reliability by means of automated response, and construct and scale clever workflows on high of instruments you already use.



