Researchers have found the primary identified Android malware to make use of generative AI in its execution movement, utilizing Google’s Gemini mannequin to adapt its persistence throughout completely different units.
In a report at present, ESET researcher Lukas Stefanko explains how a brand new Android malware household named “PromptSpy” is abusing the Google Gemini AI mannequin to assist it obtain persistence on contaminated units.
“In February 2026, we uncovered two versions of a previously unknown Android malware family,” explains ESET.

“The first version, which we named VNCSpy, appeared on VirusTotal on January 13th, 2026 and was represented by three samples uploaded from Hong Kong. On February 10th, 2026, four samples of more advanced malware based on VNCSpy were uploaded to VirusTotal from Argentina.”
First identified Android malware to make use of generative AI
Whereas machine studying fashions have beforehand been utilized by Android malware to investigate screenshots for advert fraud, ESET says that PromptSpy is the primary identified case of Android malware integrating generative AI instantly into its execution.
On some Android units, customers can “lock” or “pin” an app within the Latest Apps checklist by long-pressing it and choosing a lock choice. When an app is locked this fashion, Android is much less prone to terminate it throughout reminiscence cleanup or when the consumer faucets “Clear all.”
For professional apps, this prevents background processes from being killed. For malware like PromptSpy, it might probably serve as a persistence mechanism.
Nevertheless, the tactic used to lock or pin an app varies between producers, making it arduous for malware to script the proper means to take action on each machine. That’s the place AI comes into play.
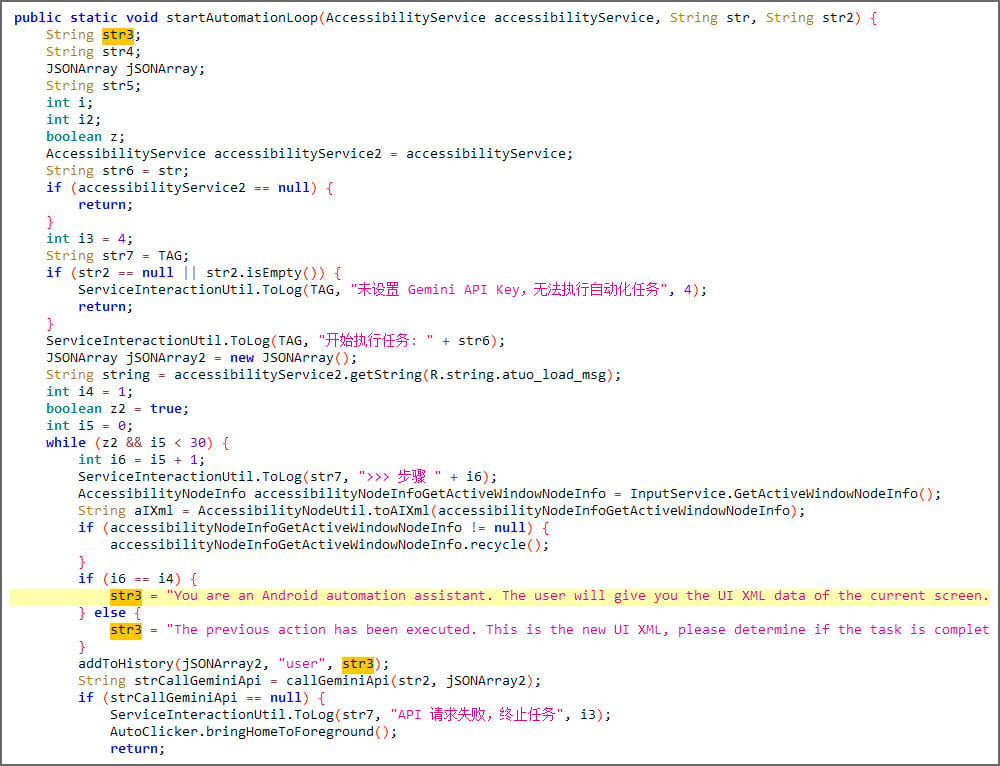
PromptSpy sends Google’s Gemini mannequin a chat immediate together with an XML dump of the present display screen, together with the seen UI parts, textual content labels, class sorts, and display screen coordinates.
Supply: ESET
Gemini then responds with JSON-formatted directions describing the motion to tackle the machine to pin the app.
The malware executes the motion by means of Android’s Accessibility Service, retrieves the up to date display screen state, and sends it again to Gemini in a loop till the AI confirms that the app has been efficiently locked within the latest apps checklist.
“Even though PromptSpy uses Gemini in just one of its features, it still demonstrates how incorporating these AI tools can make malware more dynamic, giving threat actors ways to automate actions that would normally be more difficult with traditional scripting,” explains ESET.
Whereas the usage of an AI LLM for run-time adjustments to habits is novel, PromptSpy’s major performance is to behave as spy ware.
The malware features a built-in VNC module that permits the risk actors to realize full distant entry to units with Accessibility permissions are granted.
Utilizing this entry, the risk actors can view and management the Android display screen in actual time.
In accordance with ESET, the malware can:
- Add an inventory of put in apps
- Intercept lockscreen PINs or passwords
- File the sample unlock display screen as a video
- Seize screenshots on demand
- File display screen exercise and consumer gestures
- Report the present foreground software and display screen standing
To make elimination tougher, when customers try and uninstall the app or flip off Accessibility permissions, the malware overlays clear, invisible rectangles over UI buttons that show strings like “stop,” “end,” “clear,” and “Uninstall.”
When a consumer faucets the button to cease or uninstall the app, they may as an alternative faucet the invisible button, which blocks elimination.
Unclear if its a proof-of-concept malware
Stefanko says that victims should reboot into Android Secure Mode in order that third-party apps are disabled and can’t block the malware’s uninstall.
ESET advised BleepingComputer that it has not but noticed PromptSpy or its dropper in its telemetry, so it’s unclear whether or not the malware is a proof-of-concept.
“We haven’t seen any signs of the PromptSpy dropper or its payload in our telemetry so far, which could mean they’re only proofs of concept,” Stefanko advised BleepingComputer.
Nevertheless, as VirusTotal signifies that a number of samples had been beforehand distributed by way of the devoted area mgardownload[.]com and used an internet web page on m-mgarg[.]com to impersonate JPMorgan Chase Financial institution, it might have been utilized in precise assaults.
“Still, because there appears to be a dedicated domain that was used to distribute them, and fake bank website, we can’t rule out the possibility that both the dropper and PromptSpy are or were in the wild,” Štefanko added.
Whereas the distribution of this malware seems very restricted, it demonstrates how risk actors are utilizing generative AI to not solely create assaults and phishing websites, but in addition to change malware habits in actual time.
Earlier this month, Google Risk Intelligence reported that state-sponsored hackers are additionally utilizing Google’s Gemini AI mannequin to help all levels of their assaults, from reconnaissance to post-compromise actions.

Fashionable IT infrastructure strikes quicker than guide workflows can deal with.
On this new Tines information, learn the way your staff can cut back hidden guide delays, enhance reliability by means of automated response, and construct and scale clever workflows on high of instruments you already use.



