New analysis from the Citizen Lab has discovered indicators that Kenyan authorities used a business forensic extraction software manufactured by Israeli firm Cellebrite to interrupt right into a distinguished dissident’s telephone, making it the newest case of abuse of the expertise focusing on civil society.
The interdisciplinary analysis unit on the College of Toronto’s Munk College of World Affairs & Public Coverage stated it discovered the indications on a private telephone belonging to Boniface Mwangi, a Kenyan pro-democracy activist who has introduced plans to run for president in 2027.
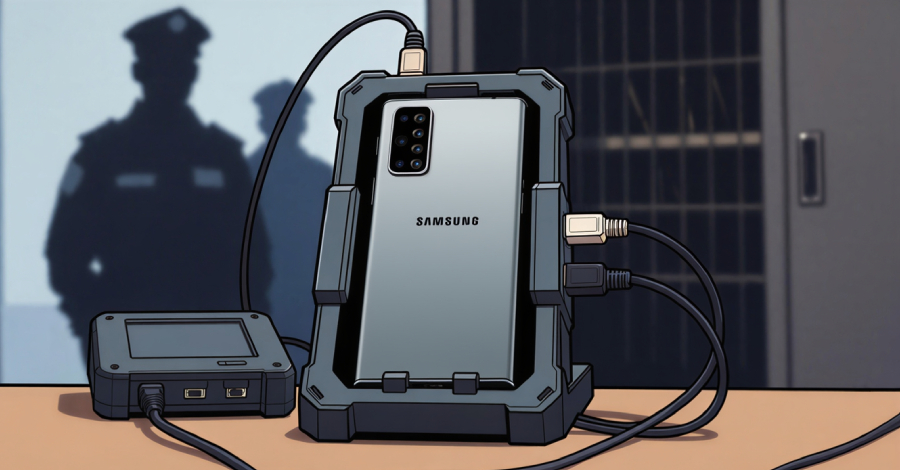
Particularly, it has emerged that Cellebrite’s forensic extraction instruments have been used on his Samsung telephone whereas it was in police custody following his arrest in July 2025.
The telephone was returned to him practically two months later, in September, at which level Mwangi discovered that the telephone was not password-protected and may very well be unlocked with out requiring a password. It has been assessed with excessive confidence that Cellebrite’s expertise was used on the telephone on or round July 20 and July 21, 2025.
“The use of Cellebrite could have enabled the full extraction of all materials from Mwangi’s device, including messages, private materials, personal files, financial information, passwords, and other sensitive information,” the Citizen Lab stated.
The newest findings observe a separate report launched final month, through which the researchers stated officers in Jordan possible used Cellebrite to extract info from the cell phones of activists and human rights defenders who had been crucial of Israel and spoke out in assist of Palestinians in Gaza.
The gadgets have been seized by Jordanian authorities throughout detentions, arrests, and interrogations, and subsequently returned to them. The documented incidents befell between late 2023 and mid-2025, the Citizen Lab stated.
In response to the findings, a spokesperson for Cellebrite instructed The Guardian that the corporate’s expertise is used to “access private data only in accordance with legal due process or with appropriate consent to aid investigations legally after an event has occurred.”
The 2 instances add to a rising physique of proof documenting the misuse of Cellebrite expertise by authorities shoppers. It additionally displays a broader ecosystem of surveillance abuses by varied governments around the globe to allow highly-targeted surveillance utilizing mercenary adware like Pegasus and Predator.
Predator Spy ware Targets Angolan Journalist

The event additionally coincides with one other report from Amnesty Worldwide, which found proof that the iPhone belonging to Teixeira Cândido, an Angolan journalist and press freedom advocate, was efficiently focused by Intellexa’s Predator adware in Could 2024 after he opened an an infection hyperlink obtained through WhatsApp.
The iPhone was working iOS 16.2, an outdated model of the working system with recognized safety points. It is presently not recognized what exploit was used to set off the an infection. In a number of reviews printed final yr, Recorded Future revealed that it has noticed suspected Predator operations in Angola courting again to 2024.
“This is the first forensically confirmed case of the Predator spyware being used to target civil society in Angola,” the worldwide human rights group stated. “Once the spyware was installed, the attacker could gain unrestricted access to Teixeira Cândido’s iPhone.”
“The Predator spyware infection appears to have lasted less than one day, with the infection being removed when Teixeira Cândido’s phone was restarted in the evening of 4 May 2024. From that time until 16 June 2024, the attackers made 11 new attempts to re-infect the device by sending him new malicious Predator infection links. All of these subsequent attack attempts appear to have failed, likely due to the links simply not being opened.”

Based on an evaluation printed by French offensive safety firm Reverse Society, Predator is a business adware product “built for reliable, long-term deployment” and permits operators to selectively allow or disable modules based mostly heading in the right direction exercise, granting them real-time management over surveillance efforts.
Predator has additionally been discovered to include varied undocumented anti-analysis mechanisms, together with a crash reporter monitoring system for anti-forensics and SpringBoard hooking to suppress recording indicators from victims when the microphone or digital camera is activated, illustrating the sophistication of the adware. On high of that, it has specific checks to keep away from working in U.S. and Israeli locales.
“These findings demonstrate that Predator’s operators have granular visibility into failed deployments, […] enabling them to adapt their approaches for specific targets,” Jamf Risk Labs researchers Shen Yuan and Nir Avraham stated. “This error code system transforms failed deployments from black boxes into diagnostic events.”