Cybersecurity researchers have taken the wraps off a gateway-monitoring and adversary-in-the-middle (AitM) framework dubbed DKnife that is operated by China-nexus menace actors since no less than 2019.
The framework includes seven Linux-based implants which are designed to carry out deep packet inspection, manipulate site visitors, and ship malware through routers and edge units. Its major targets appear to be Chinese language-speaking customers, an evaluation based mostly on the presence of credential harvesting phishing pages for Chinese language electronic mail providers, exfiltration modules for fashionable Chinese language cellular purposes like WeChat, and code references to Chinese language media domains.
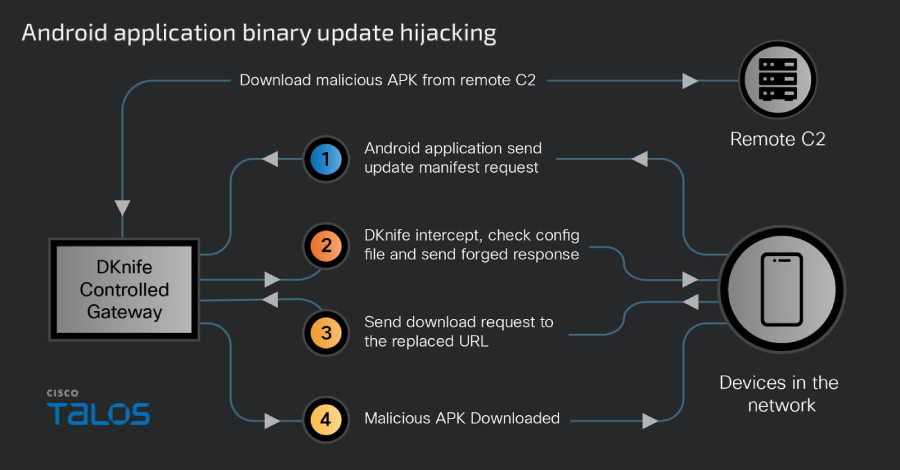
“DKnife’s attacks target a wide range of devices, including PCs, mobile devices, and Internet of Things (IoT) devices,” Cisco Talos researcher Ashley Shen famous in a Thursday report. “It delivers and interacts with the ShadowPad and DarkNimbus backdoors by hijacking binary downloads and Android application updates.”
The cybersecurity firm mentioned it found DKnife as a part of its ongoing monitoring of one other Chinese language menace exercise cluster codenamed Earth Minotaur that is linked to instruments just like the MOONSHINE exploit package and the DarkNimbus (aka DarkNights) backdoor. Curiously, the backdoor has additionally been put to make use of by a 3rd China-aligned superior persistent menace (APT) group known as TheWizards.
An evaluation of DKnife’s infrastructure has uncovered an IP tackle internet hosting WizardNet, a Home windows implant deployed by TheWizards through an AitM framework known as Spellbinder. Particulars of the toolkit have been documented by ESET in April 2025.
The focusing on of Chinese language-speaking customers, Cisco mentioned, hinges on the invention of configuration information obtained from a single command-and-control (C2) server, elevating the likelihood that there might be different servers internet hosting related configurations for various regional focusing on.
That is important in gentle of infrastructural connections between DKnife and WizardNet, as TheWizards is understood to focus on people and the playing sector throughout Cambodia, Hong Kong, Mainland China, the Philippines, and the United Arab Emirates.
 |
| Features of seven DKnife elements |
In contrast to WizardNet, DKnife is engineered to be run on Linux-based units. Its modular structure allows operators to serve a variety of features, starting from packet evaluation to site visitors manipulation. Delivered via an ELF downloader, it accommodates seven totally different elements –
- dknife.bin – The central nervous system of the framework answerable for deep packet inspection, person actions reporting, binary obtain hijacking, and DNS hijacking
- postapi.bin – An information reporter module that acts as a relay by receiving site visitors from DKnife and reporting to distant C2
- sslmm.bin – A reverse proxy module modified from HAProxy that performs TLS termination, electronic mail decryption, and URL rerouting
- mmdown.bin – An updater module that connects to a hard-coded C2 server to obtain APKs used for the assault
- yitiji.bin – A packet forwarder module that creates a bridged TAP interface on the router to host and route attacker-injected LAN site visitors
- distant.bin – A peer-to-peer (P2P) VPN shopper module that creates a communication channel to distant C2
- dkupdate.bin – An updater and watchdog module that retains the assorted elements alive
“DKnife can harvest credentials from a major Chinese email provider and host phishing pages for other services,” Talos mentioned. “For harvesting email credentials, the sslmm.bin component presents its own TLS certificate to clients, terminates and decrypts POP3/IMAP connections, and inspects the plaintext stream to extract usernames and passwords.”
“Extracted credentials are tagged with ‘PASSWORD,’ forwarded to the postapi.bin component, and ultimately relayed to remote C2 servers.”
The core element of the framework is “dknife.bin,” which takes care of deep packet inspection, permitting operators to conduct site visitors monitoring campaigns starting from “covert monitoring of user activity to active in-line attacks that replace legitimate downloads with malicious payloads.” This contains –
- Serving up to date C2 to Android and Home windows variants of DarkNimbus malware
- Conducting Area Identify System (DNS)-based hijacking over IPv4 and IPv6 to facilitate malicious redirects for JD.com-related domains
- Hijacking and changing Android utility updates related to Chinese language information media, video streaming, picture enhancing apps, e-commerce platforms, taxi-service platforms, gaming, and pornography video streaming apps by intercepting their replace manifest requests
- Hijacking Home windows and different binary downloads based mostly on sure pre-configured guidelines to ship through DLL side-loading the ShadowPad backdoor, which then masses DarkNimbus
- Interfering with communications from antivirus and PC-management merchandise, together with 360 Complete Safety and Tencent providers
- Monitoring person exercise in real-time and reporting it again to the C2 server
“Routers and edge devices remain prime targets in sophisticated targeted attack campaigns,” Talos mentioned. “As threat actors intensify their efforts to compromise this infrastructure, understanding the tools and TTPs they employ is critical. The discovery of the DKnife framework highlights the advanced capabilities of modern AitM threats, which blend deep‑packet inspection, traffic manipulation, and customized malware delivery across a wide range of device types.”