A joint international crackdown by American and Chinese authorities has resulted in the detention of at least 276 individuals and the closure of nine fraud hubs involved in cryptocurrency investment scams aimed at U.S. citizens, which caused losses running into millions of dollars.
The operation was spearheaded by the Dubai Police, under the umbrella of the United Arab Emirates (UAE) Ministry of Interior, working alongside the U.S. Federal Bureau of Investigation (FBI) and the Chinese Ministry of Public Security. Among those taken into custody are nationals from Burma and Indonesia, who were detained by authorities in Dubai and Thailand.
Thet Min Nyi, 27, Wiliang Awang, 23, Andreas Chandra, 29, Lisa Mariam, 29, and two fugitive associates have been formally charged in the United States with offenses related to fraud and money laundering.
“Those who swindle Americans from beyond U.S. borders will not escape accountability, regardless of where on the globe they operate,” stated Assistant Attorney General A. Tysen Duva of the Justice Department’s Criminal Division. “The architects and perpetrators of these scams, whether targeting Americans or others, will be held to account — in American courtrooms and beyond. In today’s interconnected world, fraud knows no frontiers, and neither does the law enforcement effort dedicated to stopping it.”
Court documents allege that the accused were responsible for managing, staffing, and recruiting personnel into three entities — Ko Thet Company, Sanduo Group, and Giant Company — which are said to have run multiple scam operations. Thet Min Nyi is identified as a manager and recruiter for Ko Thet Company.
The fraudulent scheme followed a well-known pattern: victims were lured into parting with their savings via fake cryptocurrency investment opportunities after scammers built personal trust, often through deceptive friendships or romantic entanglements — a method widely referred to as “pig butchering” or romance baiting. The criminal enterprise is deeply connected to human trafficking, as foreign nationals were lured with promises of lucrative employment and then forced to carry out the scams under conditions akin to modern-day slavery.
“Once trust was established, the fraudsters pushed cryptocurrency investment schemes, helping victims create accounts and transfer digital currencies to what appeared to be investment platforms,” the DoJ explained. “Unbeknownst to the victims, these platforms were entirely fraudulent. The scammers flaunted their supposed investment profits and urged victims to put in even more money, going so far as to pressure them to borrow from loved ones or take out additional loans to ‘invest’ further.”
However, as soon as the money was sent to these platforms, it was quickly funneled into other cryptocurrency wallets — many of which belonged directly to the scammers themselves.
The DoJ reported that the FBI has reached out to nearly 9,000 victims and managed to prevent an estimated $562 million in losses as of April 2026. This progress follows the launch of Operation Level Up, an initiative that began in January 2024 with the goal of proactively identifying and warning potential targets of cryptocurrency investment fraud.
Two Chinese Nationals Indicted for Crypto Scam Activities
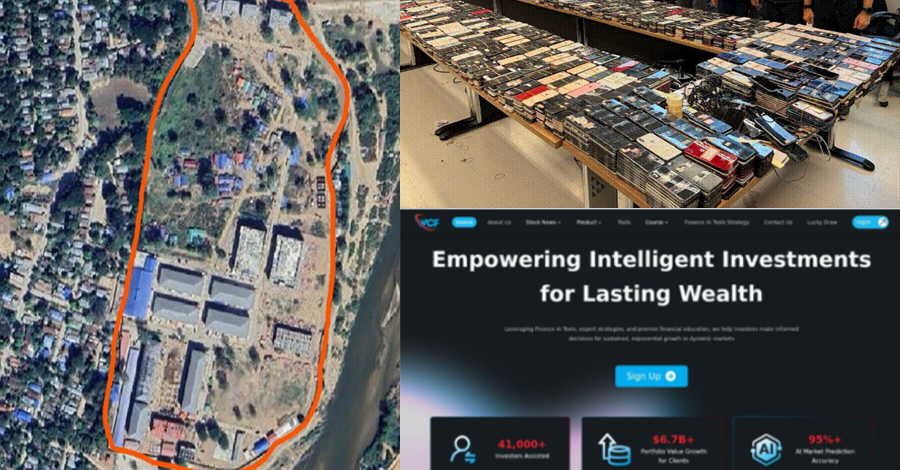
The unsealing of the indictment follows shortly after the DoJ brought charges against two Chinese citizens — Jiang Wen Jie (also known as Jiang Nan) and Huang Xingshan (also known as Ah Zhe and Huang Xing Saan) — for their prominent roles in a major cryptocurrency investment fraud ring and for allegedly overseeing the Shunda scam compound located in Min Let Pan, Myanmar. The pair are also accused of plotting to establish a second scam hub in Cambodia after Burmese authorities shut down the first facility in November 2025.
Huang is believed to have served as a senior manager at Shunda and is alleged to have personally taken part in physically punishing trafficked workers at the compound. Jiang reportedly held a leadership role, supervising teams tasked specifically with targeting American victims. Both were apprehended by Thai authorities in early 2026 while traveling from Cambodia to Burma.

“The compound utilized fraudulent websites and mobile apps that were made to look like legitimate investment platforms in order to deceive victims, including Americans,” the DoJ stated. “The workers inside the compound were trafficking victims who were held captive and compelled to carry out fraud against their will, under threats of violence and torture.”
The broader enforcement effort also led to the takedown of a Telegram channel (@pogojobhiring2023) with more than 6,500 subscribers, which had been used to recruit human trafficking victims to a scam compound in Cambodia to work on a law enforcement impersonation scam. Additionally, authorities dismantled a network of 503 counterfeit investment websites that had been exploiting American victims. A U.S. government Scam Center Strike Force also froze more than $701 million in cryptocurrency alleged to be connected to the laundering of proceeds from these scams.
U.S. Treasury Imposes Sanctions on Cambodian Senator
In a parallel move, the U.S. Treasury Department has imposed sanctions on a Cambodian senator at the center of a sprawling network of cyber fraud compounds, while the State Department announced rewards of up to $10 million for information leading to the seizure or recovery of assets tied to the Tai Chang scam center in Myanmar.
The sanctions are aimed at Cambodian Senator Kok An, Cambodian businessman Rithy Raksmei, their associates, and their related business interests, including holding companies such as K99 Group, which operates scam centers. Kok An is believed to have fled Thailand; authorities issued arrest warrants for him and his children last July.
“Kok An and his associates’ network of scam hubs, housed in casinos and office parks repurposed for fraudulent operations, launders money stolen from victims and serves as a launchpad for targeting U.S. citizens while enabling human rights abuses without consequence,” the Office of Foreign Assets Control (OFAC) stated.
Kok An is the second Cambodian senator to face U.S. Treasury sanctions, following Ly Yong Phat, who was sanctioned in September 2024 for his alleged involvement in trafficking individuals into forced labor at online scam operations.
The rapidly expanding, industrial-scale fraud industry has pushed Cambodia’s parliament to enact its first-ever law specifically aimed at combating scam centers operating within the country. The legislation, designed to prevent scam operations from re-emerging after enforcement actions, carries prison sentences of five to 10 years for those convicted, along with fines of up to $250,000.
Cambodian Scam Compound Tied to Android Malware-as-a-Service
Adding to the findings, researchers have uncovered an Android banking trojan — believed to be operating from multiple locations, including the K99 Triumph City compound owned by Cambodia’s K99 Group — that is capable of conducting real-time surveillance, stealing credentials, extracting data, and carrying out financial fraud. This malware has reportedly been in active use since at least 2023.
According to a joint report, the advanced malware-as-a-service (MaaS) platform shares infrastructure and behavioral patterns with activities previously linked to threat actors known as Vigorish Viper and Vault Viper.
The campaign is still ongoing, with about 35 new domains created each month. These include both algorithm-generated domains and lookalike ones, mimicking real organizations and government services to spread the malware, according to researchers.
The domains imitate banks, pension funds, social security bodies, utility companies, and various agencies for revenue, immigration, telecom, and law enforcement. Recently, the scam has broadened in scope—both geographically and thematically—to target airlines, e-commerce platforms, and countries in Africa and Latin America as well.
In total, 400 malicious lure domains were registered in 2025 to trick and infect victims in what appears to be a well-coordinated operation. The attack process works as follows –
- Harmful URLs are sent to users through SMS or emails that appear to be from government officials.
- Fake Google Play Store app listing pages or government service websites are visited by victims.
- After the APK is installed and opened, it gains elevated permissions to maintain persistence.
- The malware connects to an external server, allowing the operator to remotely monitor the victim device and collect data.
- Attackers place counterfeit overlay screens over online banking apps to capture login credentials and then use the access to transfer funds to accounts they control.
“The activity tied to this infrastructure continues to evolve and grow, sustaining large-scale campaigns targeting countries like Thailand, Indonesia, the Philippines, and Vietnam, while increasingly expanding into Africa and Latin America,” noted Infoblox and Chong Lua Dao.
“With access to large multilingual workforces, advancing technical skills, and enormous profits, they are not only embracing but customizing malware, infrastructure, and social engineering methods into flexible and scalable attack frameworks. What emerges is an ecosystem that is agile, experimental, and profit-driven – where tools are constantly repurposed, improved, and redeployed to maximize impact and earnings.”
Operation Atlantic Seizes $12M
These developments come in the context of Operation Atlantic, which has successfully frozen about $12 million from a cybercriminals’ operation targeting cryptocurrency and investment scammers. The criminals used a technique known as “approval phishing” to gain access to crypto wallets and drain their funds.
Approval phishing is a type of cryptocurrency fraud where victims are tricked into signing a blockchain transaction that gives a scammer full control over their wallet, enabling them to steal all their assets. According to TRM Labs, these phishing attacks are “often bundled with investment scams or romance fraud.”
“This tactic is frequently used in online investment fraud, commonly known as pig butchering, to lure victims into sending ever-larger amounts to scammers,” the U.S. Secret Service said in a statement.
More than 20,000 victims have been identified across 30 countries, including Canada, the U.K., and the U.S. Authorities have also seized over 120 domains used by the threat actors behind the scheme for phishing and identified an additional $33 million in funds believed to be connected to investment fraud operations globally.
In early April, the Treasury Department’s Office of Cybersecurity and Critical Infrastructure Protection (OCCIP) launched a new information-sharing initiative to bolster cybersecurity across the digital asset industry. As part of the effort, U.S. digital asset firms and industry groups meeting the Treasury’s criteria will be eligible to receive actionable cybersecurity information at no additional cost.
“The initiative will deliver timely, actionable cybersecurity information to eligible U.S. digital asset firms and industry groups, helping them better detect, prevent, and respond to cyber threats targeting their customers and networks,” the Treasury Department said.