A Brazilian technology company focused on defending networks against distributed denial-of-service (DDoS) attacks has been linked to a botnet carrying out a prolonged wave of massive DDoS strikes targeting other Brazilian internet service providers, according to KrebsOnSecurity. The company’s CEO attributes the harmful activity to a security breach and suspects it may be the work of a rival aiming to damage the firm’s reputation.
An Archer AX21 router from TP-Link. Image: tp-link.com
Over the past few years, cybersecurity researchers have observed a string of large-scale DDoS attacks originating in Brazil and aimed exclusively at Brazilian ISPs. Until recently, the identity or source behind these digital assaults remained uncertain. That uncertainty ended earlier this month when a confidential source—who requested anonymity—provided an intriguing file archive that had been left exposed in a publicly accessible online directory.
This exposed archive contained several malicious programs written in Python in Portuguese. It also included the private SSH login credentials belonging to the CEO of Huge Networks, a Brazilian ISP whose main business is providing DDoS protection services to other Brazilian network operators.
Although Huge Networks was founded in Miami, Florida in 2014, its core operations are based in Brazil. The company initially specialized in shielding gaming servers from DDoS attacks before expanding into offering DDoS mitigation services to other ISPs. There are no public records linking Huge Networks to abuse complaints, nor is it associated with any known DDoS-for-hire operations.
Yet, the exposed archive reveals that a threat actor operating in Brazil had root-level access to Huge Networks’ systems and used it to build a powerful DDoS botnet. This was accomplished by routinely scanning large portions of the internet for vulnerable routers and poorly secured domain name system (DNS) servers that could be recruited into attack campaigns.
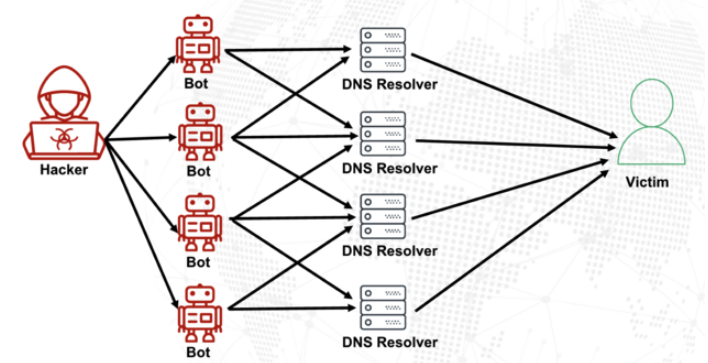
DNS translates human-readable website names into numerical IP addresses so users can easily access online services. Ideally, DNS servers only respond to queries from authorized machines within a trusted network. However, misconfigured DNS servers—often called “open resolvers”—respond to requests from anywhere on the internet. Attackers exploit these misconfigurations by sending forged DNS queries that appear to come from the victim’s address. When the DNS server replies, the response is directed at the target instead of the attacker, flooding it with traffic.
By leveraging an extension to the DNS protocol that supports large messages, attackers can dramatically amplify the volume and impact of such reflection attacks. They craft DNS queries that trigger responses many times larger than the original request—for instance, a sub-100-byte query might produce a reply 60 to 70 times bigger. This amplification becomes especially potent when attackers coordinate tens of thousands of compromised devices to send these spoofed queries at scale.
An illustration of a DNS amplification and reflection attack. Image: veracara.digicert.com
The leaked archive includes command-line logs detailing how the attacker systematically scoured the internet for TP-Link Archer AX21 routers. The botnet specifically targeted TP-Link devices still vulnerable to CVE-2023-1389—a critical command injection flaw that was patched in April 2023.
Additionally, the malicious Python scripts contained DNS lookups to domains like hikylover[.]st and c.loyaltyservices[].[.), both of which were identified in the past year as command-and-control servers for an Internet of Things (IoT) botnet powered by a variant of the Mirai malware.
Evidence in the archive shows that the botmaster managed the scanning and attack operations from a Digital Ocean cloud server that has been repeatedly flagged—over 100 times in the past year—for malicious activity. The Python scripts reference multiple IP addresses owned by Huge Networks, which were used to identify targets and launch coordinated DDoS campaigns. The attacks were narrowly focused on Brazilian IP address ranges, and the scripts reveal that each targeted IP prefix was bombarded for just 10 to 60 seconds using four parallel processes before the botnet shifted to its next target.
Crucially, the leaked files demonstrate that these attack scripts relied on the private SSH keys belonging to Huge Networks’ CEO, Erick Nascimento. When contacted about the discovery, Mr. Nascimento stated he did not create the malicious programs and claimed he was unaware of the full scale of the DDoS operations until KrebsOnSecurity reached out.
“We reported and alerted several major upstream providers about extremely large DDoS attacks targeting small ISPs,” Nascimento said. “We didn’t investigate deeply enough at first, but what you shared makes the situation clear.”
He explained that the unauthorized access likely stems from a security breach detected in January 2026, which compromised two of the company’s development servers along with his personal SSH keys. However, he emphasized that there is no evidence those keys were used after January.
“We immediately notified the team in writing, shut down the affected servers, and rotated all keys,” Nascimento shared, along with a screenshot of a January 11 alert from Digital Ocean. “Everything was documented internally.”
Mr. Nascimento confirmed that Huge Networks has since hired an independent network forensics firm to conduct a thorough investigation.
“Based on what we’ve found so far, this appears to have stemmed from a single internal breach—one access point that allowed the attacker to move laterally into other systems, including an older personal cloud server I once used,” he wrote.
“The intrusion occurred through a jump server that multiple team members had access to,” Nascimento added. “Digital Ocean flagged the server on January 11, noting it had been compromised due to a leaked SSH key. I was traveling then and handled it upon my return. That server was promptly decommissioned and deleted, and it was never part of Huge Networks’ official infrastructure.”
The malware powering the botnet of TP-Link devices used in these DDoS attacks is derived from Mirai—a notorious strain of malware that first gained attention in September 2016 when it unleashed a record-breaking DDoS attack that took KrebsOnSecurity offline for four days. In January 2017, KrebsOnSecurity traced Mirai’s creators to two co-founders of a DDoS mitigation firm who had allegedly used the botnet to attack gaming servers and drum up new clients.
In May 2025, KrebsOnSecurity was struck again by another Mirai-powered DDoS attack, which Google described as the largest it had ever mitigated. That investigation pointed to a young Brazilian man who operated both a DDoS protection company and several DDoS-for-hire platforms, all of which have since been shut down by the FBI.
Nascimento firmly denied any involvement in launching DDoS attacks against Brazilian ISPs to promote his company’s services.
“We do not carry out DDoS attacks on Brazilian operators to sell our protection services,” he wrote in response to inquiries. “Our sales approach is primarily inbound—through channel partners, distributors, and integrators—not aggressive outreach triggered by market incidents. The victims listed in the scripts you have are mostly small regional providers; the vast majority are neither current customers nor part of our sales pipeline. This can be independently verified using public databases like QRator.”
Nascimento also claims to possess “strong blockchain-based evidence” implicating a competitor. While he declined to name the suspect, he hinted at a possible motive.
“I’d love to share the details, but publishing them now would spoil the surprise aimed at my unethical competitor,” he said. “Interestingly, your inquiry came just one week ahead of a major industry event—one this competitor has never attended before, despite its long-standing tradition in the sector. Now, for the first time, they’re participating. Seems suspicious, doesn’t it?”
Indeed, it does.



