Leaked API keys are nothing new, however the scale of the issue in front-end code has been largely a thriller – till now. Intruder’s analysis workforce constructed a brand new secrets and techniques detection methodology and scanned 5 million functions particularly on the lookout for secrets and techniques hidden in JavaScript bundles.
What we discovered revealed a large hole in how the business secures single-page functions.
42,000 secrets and techniques hidden in plain sight
The outcomes of making use of our new detection methodology at scale had been staggering. The output file alone was over 100MB of plain textual content, containing greater than 42,000 uncovered tokens throughout 334 completely different secret varieties.
These weren’t simply low-value take a look at keys or useless tokens. We discovered lively, essential credentials sitting in manufacturing code, successfully bypassing the safety controls most organizations depend on.
Here’s a breakdown of essentially the most essential dangers we uncovered.
Commonplace instruments scan your repositories, however they usually miss what will get baked into your construct.
Intruder inspects your JavaScript bundles to uncover the API keys and credentials hiding in plain sight—discovering them earlier than hackers do.
Guide a Demo
Code Repository Tokens
Essentially the most impactful exposures had been tokens for code repository platforms similar to GitHub and GitLab. In whole, we discovered 688 tokens, a lot of which had been nonetheless lively and gave full entry to repositories.
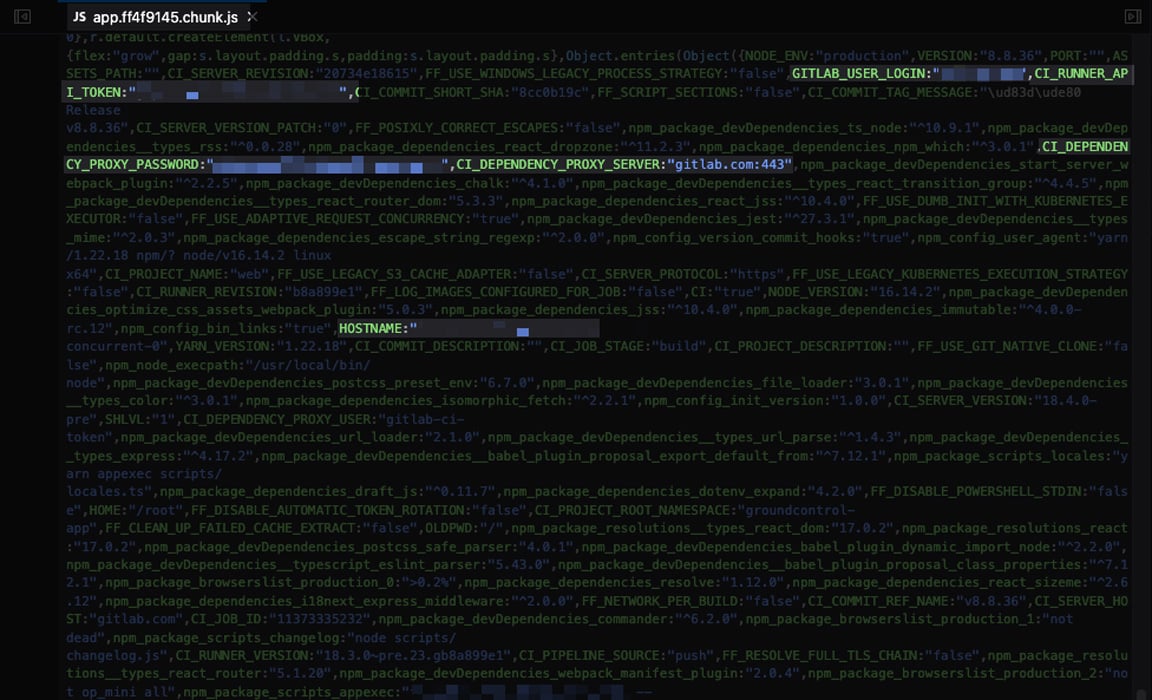
In a single case (proven under) a GitLab private entry token was embedded straight in a JavaScript file. The token was scoped to permit entry to all personal repositories throughout the group, together with CI/CD pipeline secrets and techniques for onward providers similar to AWS and SSH.
Mission Administration API Keys
One other vital publicity concerned an API key for Linear, a challenge administration software, embedded straight in front-end code:

The token uncovered the group’s whole Linear occasion, together with inside tickets, initiatives, and hyperlinks to downstream providers and SaaS initiatives.
Every little thing else
We recognized uncovered secrets and techniques throughout a variety of different providers, together with:
CAD software program APIs – entry to person information, challenge metadata, and constructing designs, together with a hospital
E mail platforms – entry to mailing lists, campaigns, and subscriber information
Webhooks for chat and automation platforms – 213 Slack, 2 Microsoft Groups, 1 Discord, and 98 Zapier, all of them lively
PDF converters – entry to third-party doc technology instruments
Gross sales intelligence and analytics platforms – entry to scraped firm and speak to information
Hyperlink shorteners – potential to create and enumerate hyperlinks
Why are these secrets and techniques being missed?
Conventional scanners don’t “speak” JavaScript
The standard, absolutely automated method to detecting software secrets and techniques is to go looking a set of identified paths and apply common expressions to match identified secret codecs.
Whereas this methodology is beneficial and might catch some exposures, it has clear limitations and won’t detect all forms of leaks, significantly people who require the scanner to spider the appliance or authenticate.
instance of that is Nuclei’s GitLab private entry token template. The scanner is fed a base URL, for instance inflicting the template to:
-
Make an HTTP GET request to https://portal.intruder.io/
-
Examine the direct response to that single request, ignoring different pages and sources similar to JavaScript information
-
Try to establish the sample of a GitLab private entry token
-
If discovered, make a follow-up request to GitLab’s public API to verify whether or not the token is lively
-
If lively, elevate a difficulty
That is clearly a easy instance, however this method is efficient. Particularly so when templates outline many paths the place secrets and techniques are generally uncovered.
This format is typical of infrastructure scanners, which don’t run a headless browser. When the scanner is given the bottom URL to scan (for instance, subsequent requests that may be made by a browser (such because the JavaScript information required to render the web page, e.g. is not going to be made utilizing this old-school method.
The “build process” blind spot
Static Utility Safety Testing (SAST) instruments analyze supply code to establish vulnerabilities and are a major technique to detect secrets and techniques in code earlier than they attain manufacturing. They’re efficient at catching hardcoded credentials and stopping some courses of publicity.
However we discovered that SAST strategies don’t cowl the total image: some secrets and techniques inside JavaScript bundles slipped by the gaps in a means that static evaluation couldn’t detect.
The DAST dilemma
Dynamic Utility Safety Testing (DAST) instruments are typically a extra strong technique to scan functions, and have a tendency to have extra complicated performance – permitting for full spidering of functions, help for authentication, and a wider functionality at detecting software layer weaknesses.
DAST scanners could seem the pure choice for secrets and techniques detection in software front-ends and there ought to be nothing holding again such a scanner from discovering out there JavaScript information, or scanning for secrets and techniques inside them.
Nevertheless, DAST is dearer, requires in-depth configuration, and in actuality is normally reserved for a small variety of high-value functions. For instance, you might be unlikely to configure a DAST scanner for each software you’ve throughout a large digital property. Plus, many DAST instruments don’t implement a large sufficient vary of standard expressions in comparison with well-known command line secrets and techniques.
This leaves a transparent hole which ought to be lined by the standard infrastructure scanner however isn’t – and in all chance can be not being lined by DAST scanners due to deployment, finances, and upkeep limitations.
Maintain your secrets and techniques secret
Shift-left controls matter. SAST, repository scanning, and IDE guardrails catch actual points and stop whole courses of publicity. However as this analysis reveals, they don’t cowl each path a secret can take into manufacturing.
Secrets and techniques launched throughout construct and deployment can bypass these safeguards and find yourself in front-end code, lengthy after the purpose the place shift-left controls have already run. And this downside will solely develop as automation and AI-generated code develop into extra frequent.
That’s why single-page software spidering is required to catch secrets and techniques earlier than they attain manufacturing. We’ve constructed automated SPA secrets and techniques detection into Intruder so groups can really catch this.
Study extra.
Writer
Ben Marr, Safety Engineer, Intruder
Ben is a Safety Engineer at Intruder, the place he automates offensive safety scanning and carries out safety analysis. His background is as an OSWE licensed penetration tester and PHP software program engineer.
Sponsored and written by Intruder.



