Cybersecurity researchers have disclosed particulars of a brand new marketing campaign that mixes ClickFix-style pretend CAPTCHAs with a signed Microsoft Utility Virtualization (App-V) script to distribute an info stealer referred to as Amatera.
“As a substitute of launching PowerShell immediately, the attacker makes use of this script to regulate how execution begins and to keep away from extra frequent, simply acknowledged execution paths,” Blackpoint researchers Jack Patrick and Sam Decker stated in a report revealed final week.
In doing so, the thought is to rework the App-V script right into a living-off-the-land (LotL) binary that proxies the execution of PowerShell by way of a trusted Microsoft element to hide the malicious exercise.
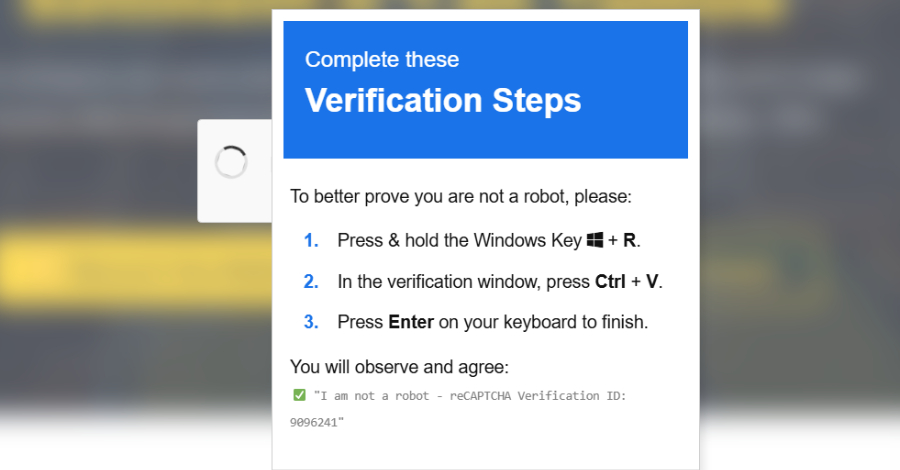
The place to begin of the assault is a pretend CAPTCHA verification immediate that seeks to trick customers into pasting and executing a malicious command on the Home windows Run dialog. However right here is the place the assault diverges from conventional ClickFix assaults.
The provided command, somewhat than invoking PowerShell immediately, abuses “SyncAppvPublishingServer.vbs,” a signed Visible Fundamental Script related to App-V to retrieve and execute an in-memory loader from an exterior server utilizing “wscript.exe.”
It is price noting that the misuse of “SyncAppvPublishingServer.vbs” isn’t new. In 2022, two totally different risk actors from China and North Korea, tracked as DarkHotel and BlueNoroff, have been noticed leveraging the LOLBin exploit to stealthily execute a PowerShell script. However that is the primary time it has been noticed in ClickFix assaults.
“Adversaries might abuse SyncAppvPublishingServer.vbs to bypass PowerShell execution restrictions and evade defensive counter measures by ‘residing off the land,'” MITRE notes in its ATT&CK framework. “Proxying execution might operate as a trusted/signed different to immediately invoking ‘powershell.exe.'”
Using an App-V script can be vital because the virtualization answer is constructed solely into Enterprise and Training editions of Home windows 10 and Home windows 11, together with fashionable Home windows Server variations. It is not accessible for Home windows Dwelling or Professional installations.
In Home windows working methods the place App-V is both absent or not enabled, the execution of the command fails outright. This additionally signifies that enterprise managed methods are seemingly the first targets of the marketing campaign.
The obfuscated loader runs checks to make sure that it isn’t run inside sandboxed environments, after which proceeds to fetch configuration information from a public Google Calendar (ICS) file, primarily turning a trusted third-party service right into a useless drop resolver.

“By externalizing configuration on this approach, the actor can quickly rotate infrastructure or regulate supply parameters with out redeploying earlier phases of the chain, decreasing operational friction and lengthening the lifespan of the preliminary an infection vector,” the researchers identified.
Parsing the calendar occasion file results in the retrieval of further loader phases, together with a PowerShell script that features as an intermediate loader to execute the following stage, one other PowerShell script, immediately in reminiscence. This step, in flip, ends in the retrieval of a PNG picture from domains like “gcdnb.pbrd[.]co” and “iili[.]io” through WinINet APIs that conceals an encrypted and compressed PowerShell payload.
The ensuing script is decrypted, GZip decompressed in reminiscence, and run utilizing Invoke-Expression, finally culminating within the execution of a shellcode loader that is designed to launch Amatera Stealer.
“What makes this marketing campaign attention-grabbing is not any single trick, however how fastidiously thought-out the whole lot is when chained collectively,” Blackpoint concluded. “Every stage reinforces the final, from requiring handbook person interplay, to validating clipboard state, to pulling reside configuration from a trusted third-party service.”
“The result’s an execution stream that solely progresses when it unfolds (virtually) precisely because the attacker expects, which makes each automated detonation and informal evaluation considerably tougher.”
The Evolution of ClickFix: JackFix, CrashFix, and GlitchFix
The disclosure comes as ClickFix has turn out to be probably the most extensively used preliminary entry strategies within the final 12 months, accounting for 47% of the assaults noticed by Microsoft.

Latest ClickFix campaigns have focused social media content material creators by claiming they’re eligible totally free verified badges, instructing them through movies to repeat authentication tokens from their browser cookies right into a pretend kind to finish the supposed verification course of. The embedded video additionally informs the person to “not log off for at the very least 24 hours” to maintain the authentication tokens legitimate.
The marketing campaign, lively since at the very least September 2025, is estimated to have used 115 net pages throughout the assault chain and eight exfiltration endpoints, per Hunt.io. The principle targets of the exercise embrace creators, monetized pages, and companies looking for verification, with the tip objective being to facilitate account takeover following token theft.
“Defending in opposition to the ClickFix approach is uniquely difficult as a result of the assault chain is constructed virtually totally on official person actions and the abuse of trusted system instruments,” Martin Zugec, technical options director at Bitdefender, stated in a report final month. “In contrast to conventional malware, ClickFix turns the person into the preliminary entry vector, making the assault look benign from an endpoint protection perspective.”

ClickFix can be consistently evolving, using variants like JackFix and CrashFix to deceive the victims into infecting their very own machines. Whereas operators use a number of strategies to aim to persuade a goal to carry out command execution, the rising recognition of the social engineering approach has paved the best way for ClickFix builders which can be marketed on hacker boards for wherever between $200 to $1,500 monthly.
The most recent entrant to this risk panorama is ErrTraffic, a site visitors distribution system (TDS) that is particularly designed for ClickFix-like campaigns by inflicting compromised web sites injected with malicious JavaScript to glitch after which suggesting a repair to handle the non-existent drawback. This method has been codenamed GlitchFix.
The malware-as-a-service (MaaS) helps three totally different file distribution modes that contain utilizing pretend browser replace alerts, pretend “system font required” dialogs, and bogus lacking system font errors to set off the execution of malicious instructions. ErrTraffic is explicitly blocked from operating on machines situated within the Commonwealth of Unbiased States (CIS) nations.

“ErrTraffic does not simply present a pretend replace immediate, it actively corrupts the underlying web page to make victims consider one thing is genuinely improper,” Censys stated. “It additionally applies CSS transformations that make the whole lot look damaged.”
ClickFix has additionally been adopted by risk actors behind the ClearFake marketing campaign, which is thought to contaminate websites with pretend net browser replace decoys on compromised WordPress to distribute malware. ClearFake’s use of ClickFix was first recorded in Could 2024, leveraging CAPTCHA challenges for delivering Emmenhtal Loader (aka PEAKLIGHT), which then drops Lumma Stealer.
The assault chain additionally makes use of one other identified approach known as EtherHiding to retrieve the next-stage JavaScript code utilizing good contracts on Binance’s BNB Good Chain (BSC) and finally inject the ClickFix pretend CAPTCHA obtained from a special good contract into the net web page. On the identical time, the ultimate stage avoids re-infecting already contaminated victims.

Like within the case of the Amatera Stealer assault, the ClickFix command copied to the clipboard abuses “SyncAppvPublishingServer.vbs” to acquire the ultimate payload hosted on the jsDelivr content material supply community (CDN). Expel’s evaluation of the ClearFake marketing campaign exhibits that as many as 147,521 methods have seemingly been contaminated since late August 2025.
“One in all many components safety merchandise use to resolve if conduct is malicious or not is whether or not stated conduct is being carried out by a trusted software,” safety researcher Marcus Hutchins stated. “On this case, ‘SyncAppvPublishingServer.vbs’ is a default Home windows element, and the file can solely be modified by TrustedInstaller (a extremely privileged system account used internally by the working system). Due to this fact, the file and its conduct alone wouldn’t usually be suspect.”
“Organizations and EDR are unlikely to outright block ‘SyncAppvPublishingServer.vbs’ from launching PowerShell in hidden mode, as it could stop the element from getting used for its meant function. Consequently, by abusing the command line injection bug in ‘SyncAppvPublishingServer.vbs,’ attackers can execute arbitrary code through a trusted system element.”

Expel additionally characterised the marketing campaign as extremely subtle and really evasive, owing to the usage of in-memory PowerShell code execution, coupled with its reliance on blockchain and fashionable CDNs, thus guaranteeing that it doesn’t talk with any infrastructure that is not a official service.
Censys has described the broader pretend CAPTCHA ecosystem as a “fragmented, fast-changing abuse sample that makes use of trusted net infrastructure because the supply floor,” whereby Cloudflare-style challenges act as a conduit for clipboard-driven execution of PowerShell instructions, VB Scripts, MSI installers, and even hand-offs to browser-native frameworks like Matrix Push C2.
“This aligns with a broader shift towards Residing Off the Internet: systematic reuse of security-themed interfaces, platform-sanctioned workflows, and conditioned person conduct to ship malware,” the assault floor administration agency stated. “Attackers don’t must compromise trusted providers; they inherit belief by working inside acquainted verification and browser workflows that customers and tooling are skilled to just accept.”