For years, identification has been handled as the muse of workforce safety. If a company may reliably verify who a consumer was, the idea adopted that entry might be granted with confidence.
That logic labored when staff accessed company networks from company gadgets beneath predictable situations. At this time, that now not displays how entry is definitely used or abused.
The fashionable workforce operates throughout a number of places, networks, and time zones. Workers routinely swap between company laptops, private gadgets, and third-party endpoints.
Entry is now not anchored to a single setting or machine, but safety groups are anticipated to assist this flexibility with out rising publicity or disrupting productiveness, even because the indicators used to make entry selections turn into noisier, extra fragmented, and tougher to belief on their very own.
Because of this, identification is being requested to hold accountability it was by no means designed to carry alone. Authentication can verify who a consumer claims to be, nevertheless it doesn’t present adequate perception into how dangerous that entry could also be as soon as machine situation and context are taken under consideration. In fashionable environments, the core difficulty is just not identification failure, however the over-reliance on identification as a proxy for belief.
Identification tells us who, not how dangerous the entry is
A official consumer accessing methods from a safe, compliant machine represents a essentially completely different danger from the identical consumer connecting from an outdated, unmanaged, or compromised endpoint. But many entry fashions proceed to deal with these eventualities as equal, granting entry totally on identification whereas machine situation stays secondary or static.
This method fails to account for the way rapidly machine danger modifications after authentication. Endpoints recurrently shift state as configurations drift, safety controls are disabled, or updates are delayed, usually lengthy after entry has already been granted.
When entry selections stay tied to the situations current at login, belief persists even because the underlying danger profile degrades.
These gaps are most seen throughout entry paths that fall exterior fashionable conditional entry protection, together with legacy protocols, distant entry instruments, and non-browser-based workflows. In these circumstances, entry selections are sometimes made with restricted context, and belief is prolonged past the purpose the place it’s justified.
Attackers are more and more exploiting these blind spots by reusing misplaced belief slightly than breaking authentication, stealing session tokens, abusing compromised endpoints, or working round multi-factor authentication.
In any case, it’s simpler to log in than break in. A sound identification introduced from the unsuitable machine stays one of the dependable methods to bypass fashionable controls and fly beneath the radar.
Verizon’s Knowledge Breach Investigation Report discovered stolen credentials are concerned in 44.7% of breaches.
Effortlessly safe Energetic Listing with compliant password insurance policies, blocking 4+ billion compromised passwords, boosting safety, and slashing assist hassles!
Strive it without spending a dime
Why Zero Belief usually falls quick
Zero Belief is extensively accepted as a safety precept, however far much less persistently utilized throughout workforce entry. Whereas identification controls have matured, progress continuously stalls on the machine layer, notably throughout entry paths exterior browser-based or fashionable conditional entry frameworks that inherit belief by default.
Establishing machine belief introduces complexity that identification alone can not tackle. Unmanaged and private gadgets are tough to evaluate persistently, compliance checks are sometimes static slightly than steady, and enforcement varies relying on how entry is initiated.
These challenges are compounded when identification and endpoint indicators are dealt with by separate instruments that had been by no means designed to work collectively. The result’s fragmented visibility and inconsistent selections.
Over time, entry insurance policies can harden and turn into static, creating extra alternatives for identification abuse. When entry is granted with out ongoing checks, conventional controls are sluggish to detect and reply to malicious conduct.
From identification checks to steady entry verification
Addressing static, identity-centric entry controls requires mechanisms that stay efficient after authentication and adapt as situations change.
Options similar to Infinipoint operationalize this mannequin by extending belief selections past identification and sustaining enforcement as situations evolve.
The next measures give attention to closing the commonest entry failure factors with out disrupting how folks work.
- Confirm each consumer and machine constantly: This method reduces the effectiveness of stolen credentials, session tokens, and multi-factor authentication bypass methods by making certain entry is tied to a trusted endpoint slightly than granted on identification alone.
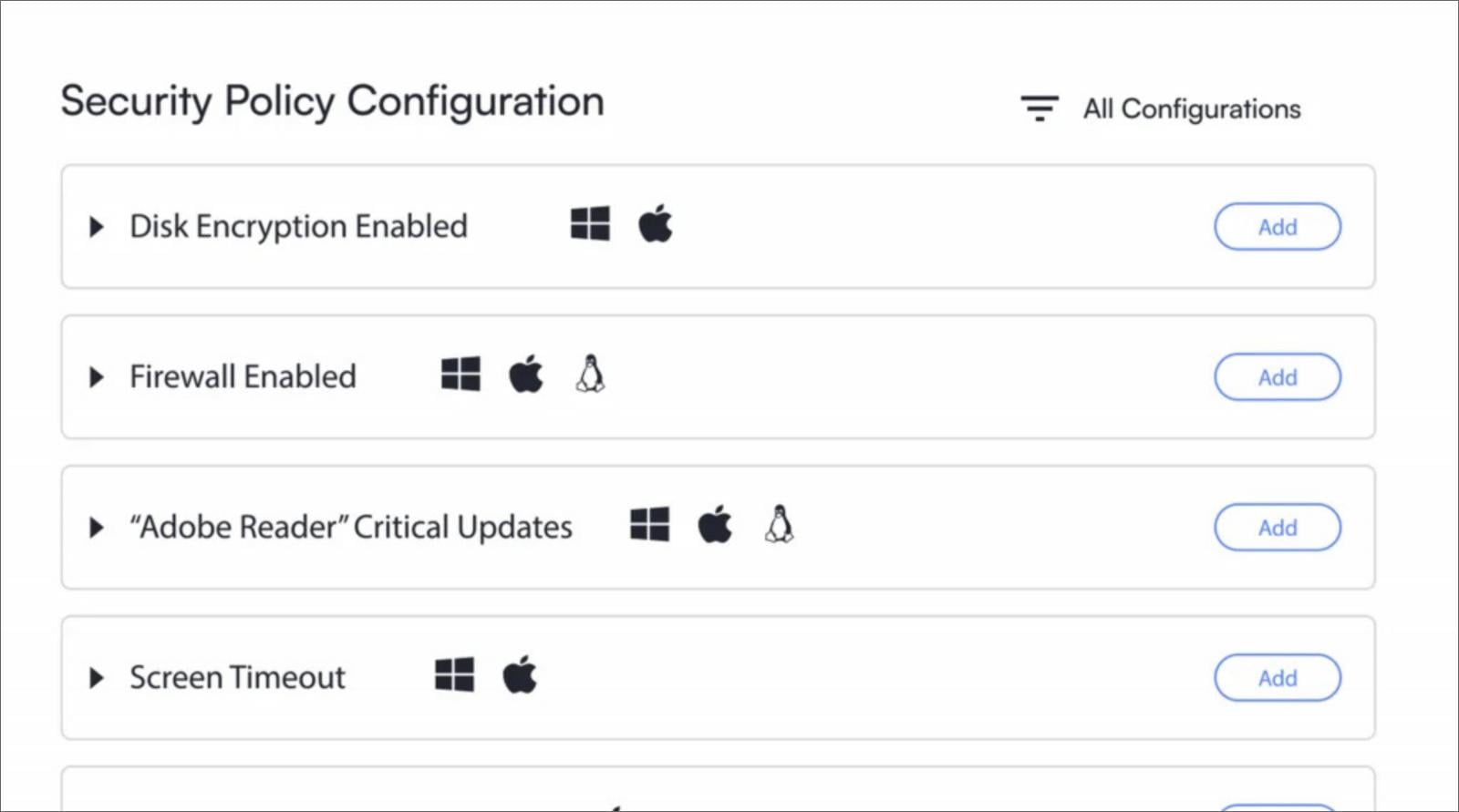
- Apply device-based entry controls: Gadget-based entry controls make it attainable to enroll authorized {hardware}, restrict the quantity and kind of gadgets per consumer, and differentiate between company, private, and third-party endpoints. This prevents attackers from reusing legitimate credentials from untrusted gadgets.
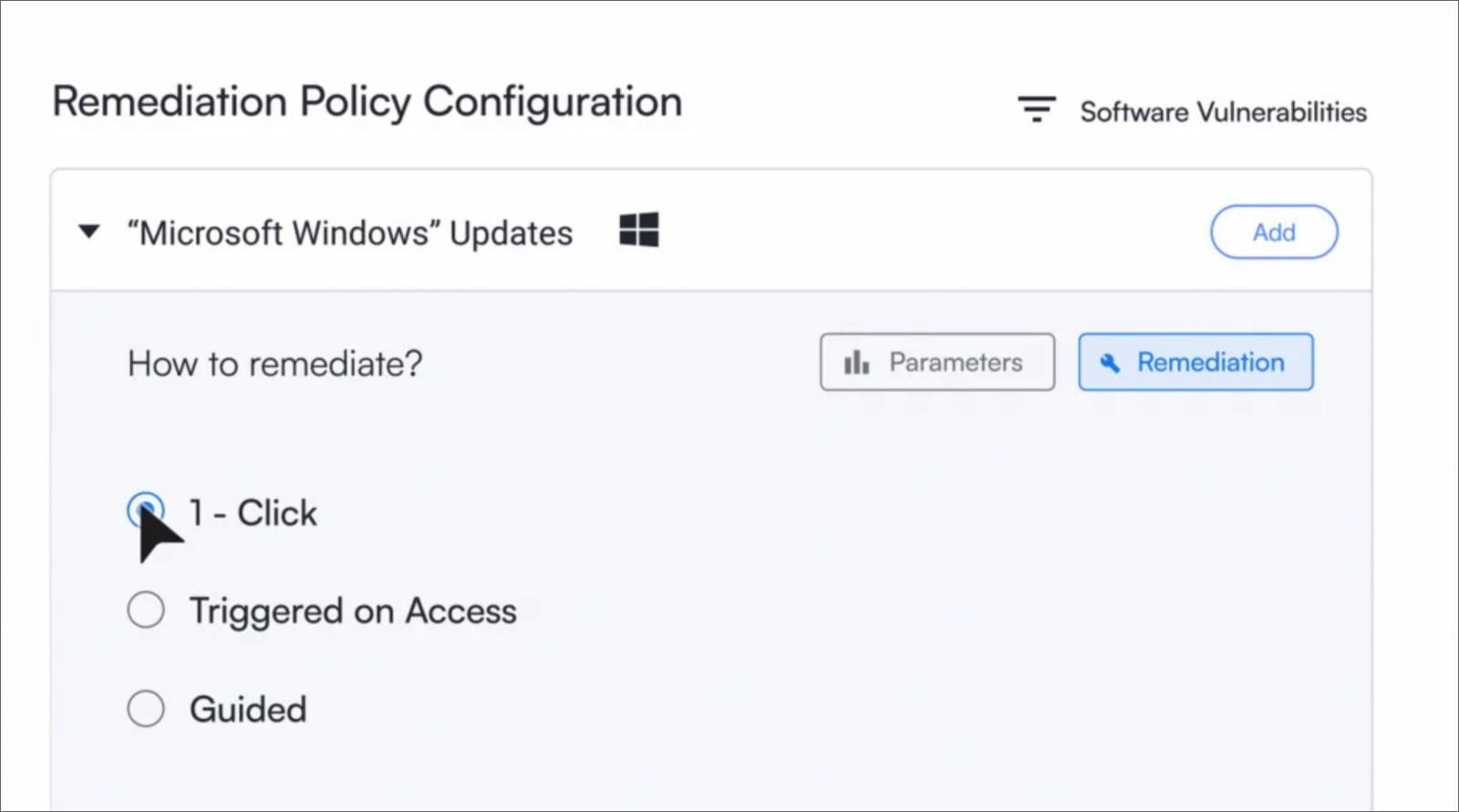
- Implement safety with out defaulting to disruption: Proportionate enforcement permits organizations to answer danger with out unnecessarily interrupting official work. This contains conditional restrictions and charm durations that give customers time to resolve points whereas sustaining safety controls.
- Allow self-service remediation to revive belief: Self-guided, one-click remediation for actions similar to enabling encryption or updating working methods permits belief to be restored effectively, decreasing assist tickets and demand on IT groups whereas maintaining safety requirements intact.
Specops, the Identification and Entry Administration division of Outpost24, delivers these controls by Infinipoint, enabling zero belief workforce entry that verifies each customers and gadgets at each entry level and constantly all through every session throughout Home windows, macOS, Linux, and cellular platforms.
Discuss to a Specops knowledgeable about implementing device-based Zero Belief entry past identification.
Sponsored and written by Specops Software program.



