When safety groups discuss assault floor, the dialog normally begins in acquainted locations. Servers, identification techniques, VPN entry, cloud workloads, possibly browsers. These are seen. They present up in diagrams and asset inventories.
What will get much less consideration are the on a regular basis instruments folks use to truly get work achieved.
PDF readers. Compression utilities. Distant entry shoppers. Phrase processors. Spreadsheet instruments. Electronic mail shoppers. Browsers. Display screen sharing software program. Replace managers. The background software program that quietly powers regular enterprise exercise.
Most organizations don’t spend a lot time debating whether or not to deploy these. They’re merely a part of working in a digital financial system. Contracts arrive as PDFs. Finance works in spreadsheets. HR evaluations resumes. IT helps customers remotely. Executives stay in electronic mail and browsers. These instruments grow to be a part of the setting virtually by default.
At Action1, the place visibility into third-party software program publicity throughout endpoints is a each day focus, these background instruments persistently emerge as a defining a part of the real-world assault floor.
That commonness is what makes them engaging targets from a menace actor’s perspective.
The worth of being abnormal
From the skin, trendy enterprises look completely different. Networks range. Architectures change. Safety stacks evolve. However, inside most environments, the identical lessons of purposes seem many times, and as a rule, the identical software program titles dominate the vast majority of installations.
It’s tough to operate in trendy enterprise with out an electronic mail consumer, doc processing software program, a browser, and instruments for packaging, previewing, and sharing information. Utilizing comparable merchandise is much less about choice and extra about compatibility.
Enterprise depends upon exchanging info in codecs everybody else can use. With out these requirements, we return to the times of file-format wars, “I cannot open that, we use something else,” and misplaced time simply making an attempt to make knowledge usable. That friction is why the business standardized, and why the identical main names nonetheless dominate.
Attackers take note of that.
Fairly than predicting each customized utility a corporation would possibly run, they search for overlap. If a vulnerability seems in a extensively used PDF engine, spreadsheet parser, electronic mail preview part, or distant entry utility, the probabilities it connects with one thing actual are excessive. The exploit is aimed much less at distinctive structure and extra at familiarity.
Most profitable exploitation doesn’t depend on unique methods. It depends on muscle reminiscence. Customers open PDFs, Phrase information, spreadsheets, and hyperlinks all day lengthy. Attackers are betting these actions really feel routine sufficient that no person hesitates.
That familiarity shapes how campaigns are constructed, and it ought to affect how protection methods are deliberate.
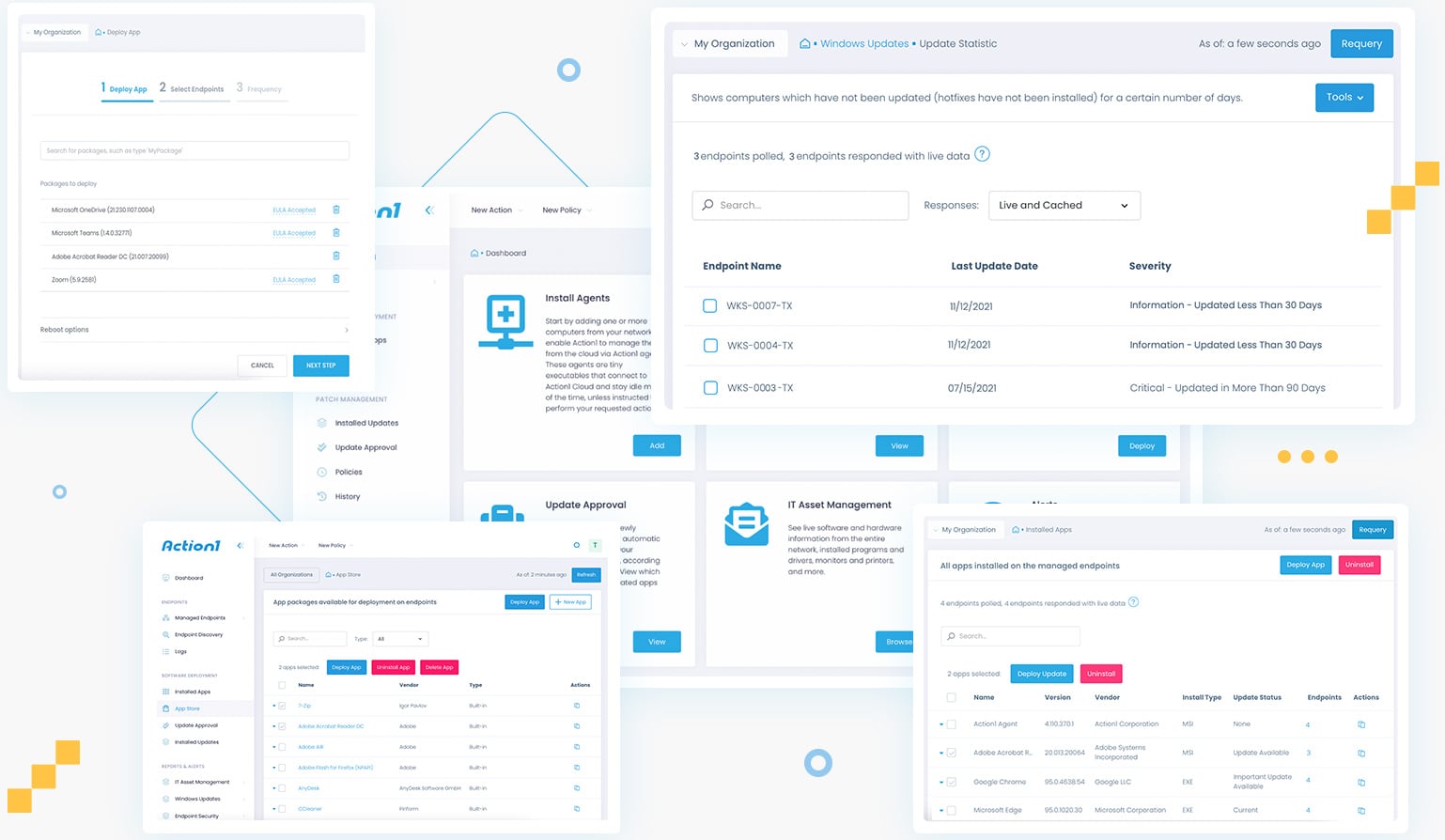
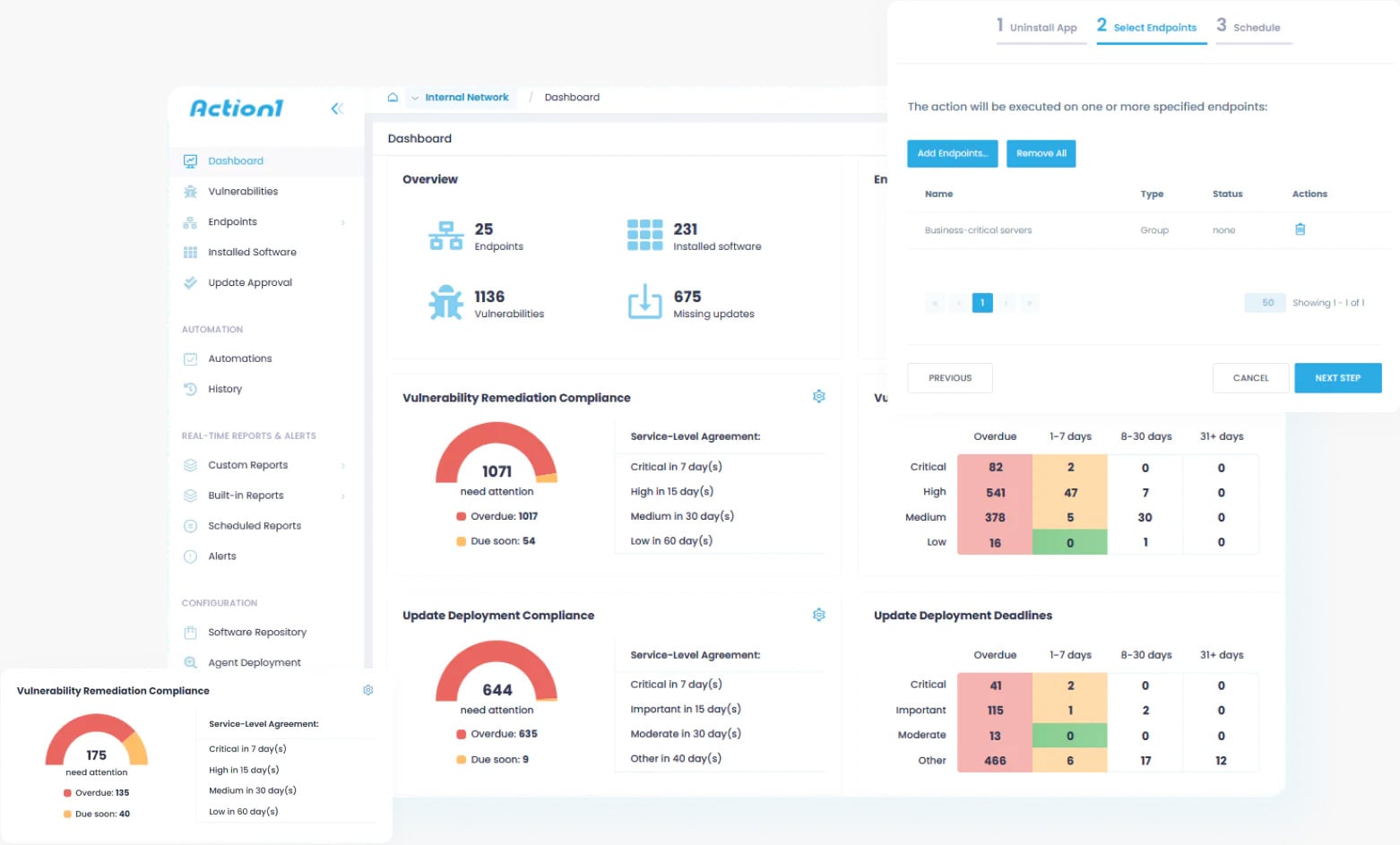
Good factor Action1 does it for you, now on Linux too—alongside Home windows, macOS, and third-party apps.
One platform. Zero infrastructure. Actual-time visibility. Lastly, patching that simply works.
See it in motion »
How chance shapes assaults
Many assaults traditionally regarded like guesswork. An attacker would possibly ship a crafted electronic mail for Outlook, hoping the recipient makes use of Outlook. Or connect a weaponized spreadsheet, hoping Excel is current. Or ship a malicious PDF, hoping the reader is weak.
There may be uncertainty in that strategy. The exploit launches earlier than the attacker actually is aware of what exists on the opposite finish. This will increase probabilities the assault will probably be detected earlier than being efficient, and it dangers beneficial exploit code to failure, the place it might be detected, profiled, then henceforth scanned and detected.
What modifications with frequent utilities is the chance curve.
Electronic mail shoppers, browsers, phrase processors, spreadsheets, PDF readers, and archive instruments seem in most enterprise environments as a result of the work itself requires them. An attacker doesn’t want excellent info to count on one thing appropriate close by.
As an alternative of treating exploitation as a one-off guess, attackers suppose in probability. They make investments effort the place overlap is largest. The extra widespread the instrument, the extra engaging it turns into as an entry level.
That’s the reason vulnerabilities in these utilities transfer rapidly by way of exploit ecosystems. As soon as one thing works in a well-recognized toolchain, it scales. If one consumer depends on Outlook, Phrase, and Adobe, there’s a good probability coworkers and enterprise relations do as nicely for interoperability causes.
The usual enterprise footprint in observe
These instruments additionally journey collectively.
If an electronic mail clearly originated from Outlook, it already hints at a part of the setting. Electronic mail workflows connect with doc workflows. If Outlook is current, Phrase and Excel are sometimes close by.
Every utility reinforces the presence of others.
For attackers, that allows paths relatively than remoted exploits. A problem in an electronic mail consumer connects to attachment dealing with, preview engines, doc renderers, shared libraries, and integrations that are likely to coexist on the identical system.
As an alternative of focusing on a single utility, the assault floor begins to resemble the enterprise footprint itself, the gathering of instruments folks depend on on daily basis.
When vulnerabilities seem in that footprint, they appeal to extra consideration as a result of they match naturally into how folks already work.
Quiet indicators and small leaks
One other a part of the story is info folks don’t notice they share.
Paperwork typically comprise metadata. PDFs reference the engine that produced them. Spreadsheets carry formatting habits tied to particular suites. Electronic mail headers expose consumer particulars. Browser site visitors advertises consumer brokers. File constructions reveal habits and variations.
A single attachment, electronic mail, or shared doc can quietly describe components of the software program stack behind it.
In isolation it doesn’t look delicate. Usually it’s not even seen. Over time it builds an image of what instruments are frequent, what requirements they observe, and the way information are processed.
What created it, what model, how not too long ago, so when outdated software program particulars present in present workflows, the software program processing it’s outdated. And outdated software program typically means years of exploit potential bottled up in a single package deal. That’s typically what turns hypothesis into precision.
These breadcrumbs assist attackers form payloads that align with what exists on the opposite aspect, growing effectiveness whereas lowering noisy experimentation.
Why third-party software program drifts
Most enterprises put actual effort into working system patching. Replace pipelines are understood. Browsers replace typically. Cellular units observe administration insurance policies. Techniques begin with baselines and are monitored.
Third-party utilities stay in a different way.
Distributors ship completely different installers. Some auto-update. Some depend on customers. Some get disabled by packaging techniques. Some keep frozen as a result of workflows rely on a model.
Over time, a number of builds of the identical instrument unfold throughout endpoints. Some grow to be stale. Some stay for years with recognized vulnerabilities just because they fell off the radar.
In Action1’s evaluation of enterprise environments, it’s common to search out a number of variations of the identical third-party utility coexisting, some lagging years behind present safety fixes. This fragmentation quietly accumulates exploit potential with out triggering apparent alerts.
From a safety view, that drift issues as a result of attackers don’t want new exploits. They profit from no matter model nonetheless exists someplace within the footprint. A five-year-old PDF reader quietly carries 5 years of cumulative exploit potential.
What seems like small technical debt widens the chance window for main exploitation.
Belief and on a regular basis habits
There may be additionally a human aspect to those instruments.
Electronic mail, paperwork, browsers, and archives really feel like infrastructure. Folks belief them like desks and keyboards. Opening a PDF doesn’t really feel like operating code. Previewing an electronic mail doesn’t really feel like execution. Extracting a file feels routine.
By the point habits seems to be uncommon, the preliminary interplay already occurred in a spot folks hardly ever query. These actions happen hundreds of instances a day, which makes tracing a compromise again to a doc, electronic mail, or consumer extraordinarily tough.
Wanting on the footprint, not simply the platform
For management groups, the worth right here is perspective, not worry.
Safety methods typically begin with the platform layer, working techniques, networks, identification, cloud infrastructure. These matter, however they don’t inform the total story of how work truly occurs.
Work occurs in electronic mail shoppers, spreadsheets, PDFs, browsers, archive instruments, and distant periods. That’s the place information open, previews render, hyperlinks get clicked, and knowledge strikes between folks.
That makes them predictable.
That’s the reason third-party patching typically carries extra threat weight than anticipated. The working system could also be tightly managed, whereas the instruments on high quietly outline actual publicity.
Wanting on the footprint is much less about assuming weak point and extra about understanding the place on a regular basis work intersects with actual safety issues.
A quieter method to consider patching
Third-party patching typically feels operational relatively than strategic. But these utilities sit on the intersection of individuals, information, and execution.
They’re abnormal, and that’s precisely why they matter.
Not as a result of each group seems to be the identical, however as a result of they appear comparable sufficient that attackers design round that similarity.
When groups study environments, the main target is normally infrastructure. There may be additionally worth in asking what the usual enterprise suite seems to be like throughout endpoints, the way it evolves, and the way persistently it stays present.
Which instruments are literally wanted? That are merely a part of a default deploy? Which keep put in even when unused? Which cease getting up to date as a result of no person notices them?
That is why, in observe, groups working with platforms like Action1 persistently see third-party patching ship a larger discount in real-world threat than many extra seen safety controls. Exploitation hardly ever hinges on a single ignored vulnerability. It’s enabled by years of collected drift throughout third-party purposes that quietly fall old-fashioned whereas remaining embedded in on a regular basis workflows.
These situations exist lengthy earlier than an exploit is written or deployed. They form the sensible assault floor by defining which software program truly executes, which information get opened, and which actions really feel routine sufficient to keep away from scrutiny.
Third-party software program shouldn’t be adjoining to the platform — it’s a part of how the platform operates, and it’s typically the place publicity concentrates when all the things else seems well-managed.
Action1is a founder-led firm, dropped at you by the unique minds behind Netwrix. On the time of this writing, it is among the fastest-growing non-public software program firms within the US as a result of organizations are recognizing that OS and third-party patching can now not be handled as a secondary activity.
Addressing trendy threat requires steady visibility into third-party software program and the flexibility to remediate weak purposes throughout endpoints rapidly and persistently. When groups consider trendy patch administration options, Action1 more and more represents the choice designed round that actuality.
Strive Action1 for free and see how efficient patch administration can rework your group’s safety posture.
Sponsored and written by Action1.



