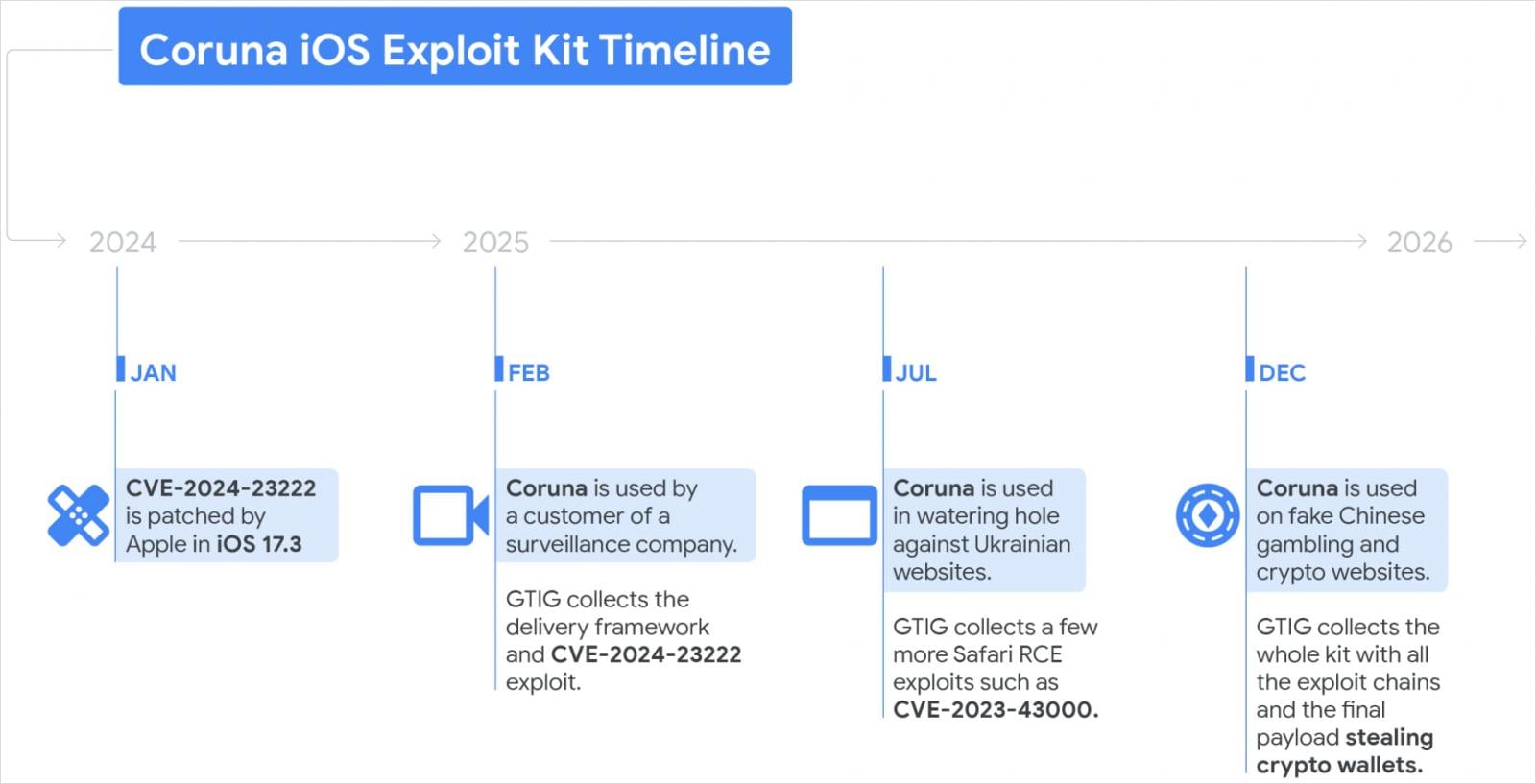
A beforehand undocumented set of 23 iOS exploits named “Coruna” has been deployed by a number of menace actors in focused espionage campaigns and financially motivated assaults.
The Coruna equipment comprises 5 full iOS exploit chains, essentially the most refined leveraging personal strategies and mitigation bypasses, for iOS variations 13.0 by way of 17.2.1 (launched in December 2023).
Google Risk Intelligence Group (GTIG) researchers first noticed exercise associated to the Coruna exploit equipment in February 2025, in exercise attributed to a surveillance vendor buyer.
On the time, researchers obtained the JavaScript supply framework together with the exploit for CVE-2024-23222, a WebKit vulnerability that allows distant code execution on iOS 17.2.1. Apple had addressed the flaw in iOS 17.3 on January 22, 2024, after it was exploited in zero-day assaults.
The identical obfuscated framework was noticed once more in summer time, when suspected Russian cyberspies tracked as UNC6353 deployed it in watering gap assaults concentrating on iPhone customers visiting compromised Ukrainian web sites for ecommerce, industrial tools and retail instruments, and native companies.
In late 2025, the exploit equipment appeared on varied pretend Chinese language playing and crypto web sites. Google attributes the exercise to the financially motivated Chinese language menace actor UNC6691.
Supply: Google
Coruna exploit equipment capabilities
After acquiring the entire exploit equipment in late 2025, GTIG analysts discovered that it included 5 full exploit chains utilizing a set of 23 exploits, together with:
- WebKit distant code execution
- Pointer Authentication Code (PAC) bypasses
- Sandbox escapes
- Kernel privilege escalation
- PPL (Web page Safety Layer) bypasses
“The exploits feature extensive documentation, including docstrings and comments authored in native English. The most advanced ones are using non-public exploitation techniques and mitigation bypasses,” GTIG researchers say.
A few of the exploits reuse vulnerabilities first recognized throughout Operation Triangulation, which was uncovered in June 2023 by Kaspersky after the cybersecurity agency found that a number of iPhones on its community had been compromised.
The corporate later found that the exploits abused undocumented {hardware} options in Apple’s gadgets.
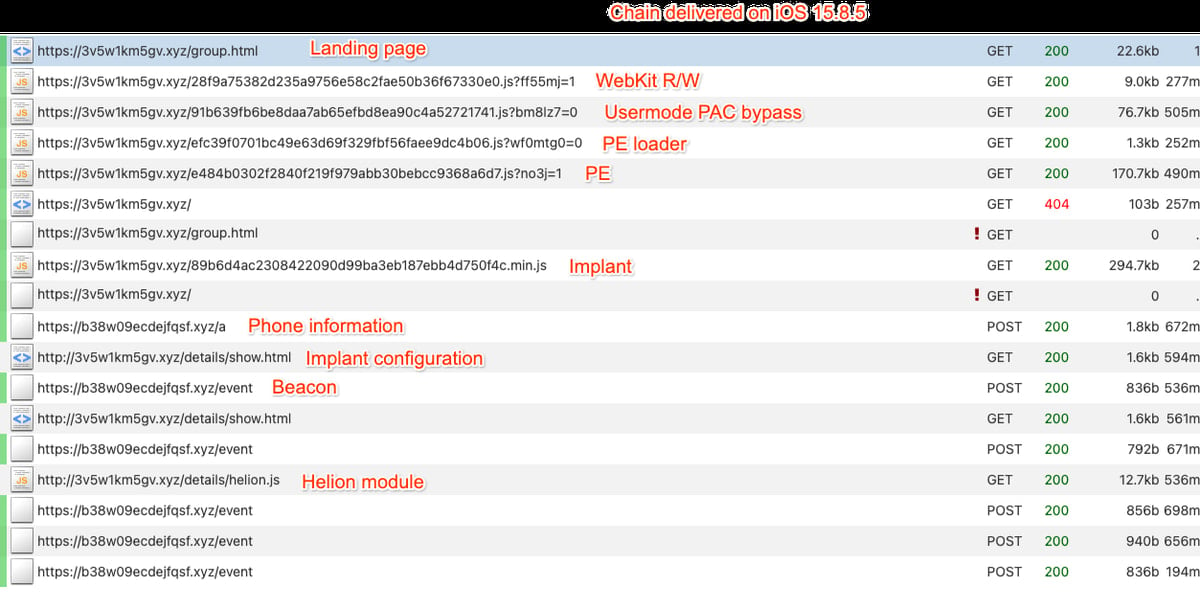
In keeping with GTIG researchers, Coruna fingerprints the gadget and OS model, after which selects the suitable exploit chain to execute.
If the Lockdown Mode anti-spyware safety characteristic or personal searching is lively on the gadget, the framework stops.
Supply: Google
Dropping PlasmaGrid
GTIG’s evaluation discovered that one of many remaining payloads delivered after a Coruna exploit chain was a stager loader known as PlasmaLoader, which the researchers observe as PlasmaGrid, that’s injected into the ‘powerd’ iOS root daemon.
Nonetheless, the malware doesn’t have capabilities in step with a adware operation. It downloads from a command-and-control (C2) server further modules that concentrate on cryptocurrency pockets apps equivalent to MetaMask, Phantom, Exodus, BitKeep, and Uniswap.
The menace actor used pretend finance and crypto-related web sites to ship the exploit equipment by making an attempt to persuade guests to make use of iOS gadgets when loading the pages.
The focused information contains pockets restoration phrases (BIP39), delicate textual content strings equivalent to “backup phrase” and “bank account,” and information saved in Apple Memos.
The stolen information is encrypted with AES previous to exfiltration and despatched to hardcoded C2 addresses. For takedown resilience, the implant additionally features a area technology algorithm (DGA) seeded with the string “lazarus” that produces .xyz domains.
GTIG could not decide how the Coruna exploit equipment moved from serving adware campaigns linked to a surveillance vendor to financially motivated malicious actions geared toward cryptocurrency customers.
“How this proliferation occurred is unclear, but suggests an active market for ‘second-hand’ zero-day exploits,” GTIG notes within the report.
Surveillance distributors hold exploit kits like Coruna beneath strict restricted entry and use them in merchandise for presidency clients working extremely focused operations. Apple has at all times claimed that such safety points had been leveraged in restricted assaults geared toward high-value people.
Cell safety firm iVerify says that Coruna is without doubt one of the clearest examples so far of “sophisticated spyware-grade capabilities” that migrated “from commercial surveillance vendors into the hands of nation-state actors and, ultimately, mass-scale criminal operations.”
This reinforces iVerify’s long-standing perception that the cell menace panorama is evolving quickly, “and the tools once reserved for targeting heads of state are now being deployed against ordinary iPhone users.”
Google has added to Secure Looking all web sites and domains recognized whereas analyzing the Coruna exploit equipment, and recommends iOS customers to improve to the newest model. If updating just isn’t doable, the recommendation is to allow Lockdown Mode.
Other than the vulnerabilities included within the Corona exploit equipment and their codenames, GTIG’s report additionally contains indicators of compromise for the implant and modules delivered through the cryptocurrency-related web sites, and assault infrastructure.

Malware is getting smarter. The Pink Report 2026 reveals how new threats use math to detect sandboxes and conceal in plain sight.
Obtain our evaluation of 1.1 million malicious samples to uncover the highest 10 strategies and see in case your safety stack is blinded.



