Trendy fraud assaults appear like a relay race the place completely different instruments and actors deal with every stage of the journey from signup to cash-out.
If you solely examine one sign at a time, comparable to IP or e mail, attackers merely shift to a special a part of the chain and nonetheless succeed.

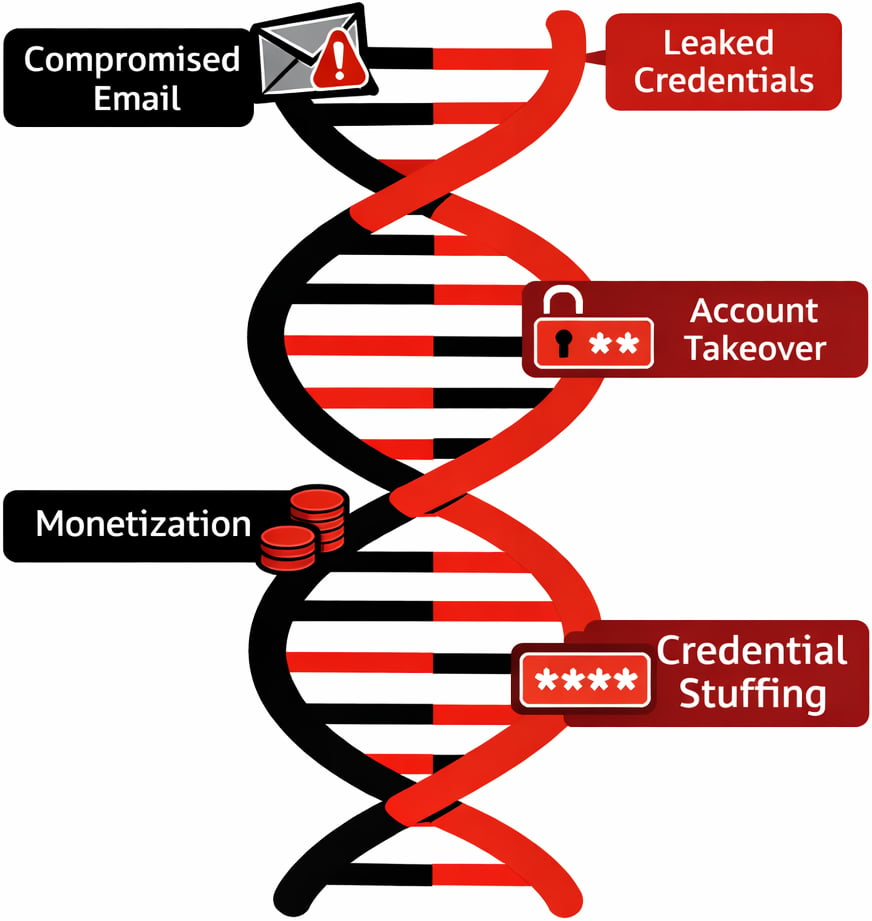
Anatomy of a Trendy Fraud Chain
A typical assault chain begins with automation to create scale. Attackers use bots and scripts to open giant numbers of accounts with minimal human effort, typically rotating infrastructure to keep away from price limits and easy bot guidelines.
These bots are often powered by “aged” or compromised emails and leaked credentials so that each account seems prefer it belongs to a protracted standing person as an alternative of one thing created yesterday.
Residential proxies then masks visitors behind actual shopper IP ranges, making visitors appear as if regular residence customers somewhat than information facilities or recognized VPN companies.
As soon as these accounts are established, they shift ways from automation to slower, human pushed classes to mix into regular utilization.
At this level the chain reaches account takeover and monetization, utilizing malware hyperlinks, phishing, and credential stuffing outputs to log in, change particulars, and push by way of excessive worth transactions.
All through this lifecycle, the instruments are blended and matched. A single actor might transfer from a headless browser and proxy at signup to a cellular machine emulator and completely different proxy supplier at login, then hand off entry to a different occasion who makes a speciality of draining funds or exploiting promo campaigns.
That is precisely why a time limit, single sign test not often tells the total story
False Positives from Siloed Checks
When groups lean on one dominant sign, comparable to IP status, false positives turn out to be a each day downside. Respectable customers on shared Wi Fi, cellular service NATs, or company VPNs can inherit the poor status of a small variety of unhealthy actors on the identical ranges, despite the fact that their intent is clear.
Blocking by e mail alone has related points, since free webmail domains are utilized by each refined attackers and fully regular prospects.
Id centric controls on their very own additionally hit a wall. Static information checks, like easy identify and doc matches, are simple to spoof for artificial identities constructed from actual information fragments.
Machine centric controls that solely search for rooted telephones or emulators can miss fraudsters working on seemingly regular gadgets which were compromised earlier within the chain. Even bot particular options can create blind spots once they work alone.
As soon as a credential stuffing marketing campaign ends and attackers pivot to guide logins with the identical stolen credentials, pure bot instruments see solely “human” visitors and approve it. The result’s a sample the place excessive threat customers are blocked whereas decided adversaries adapt and slip by way of.
Multi-Sign Correlation in Apply
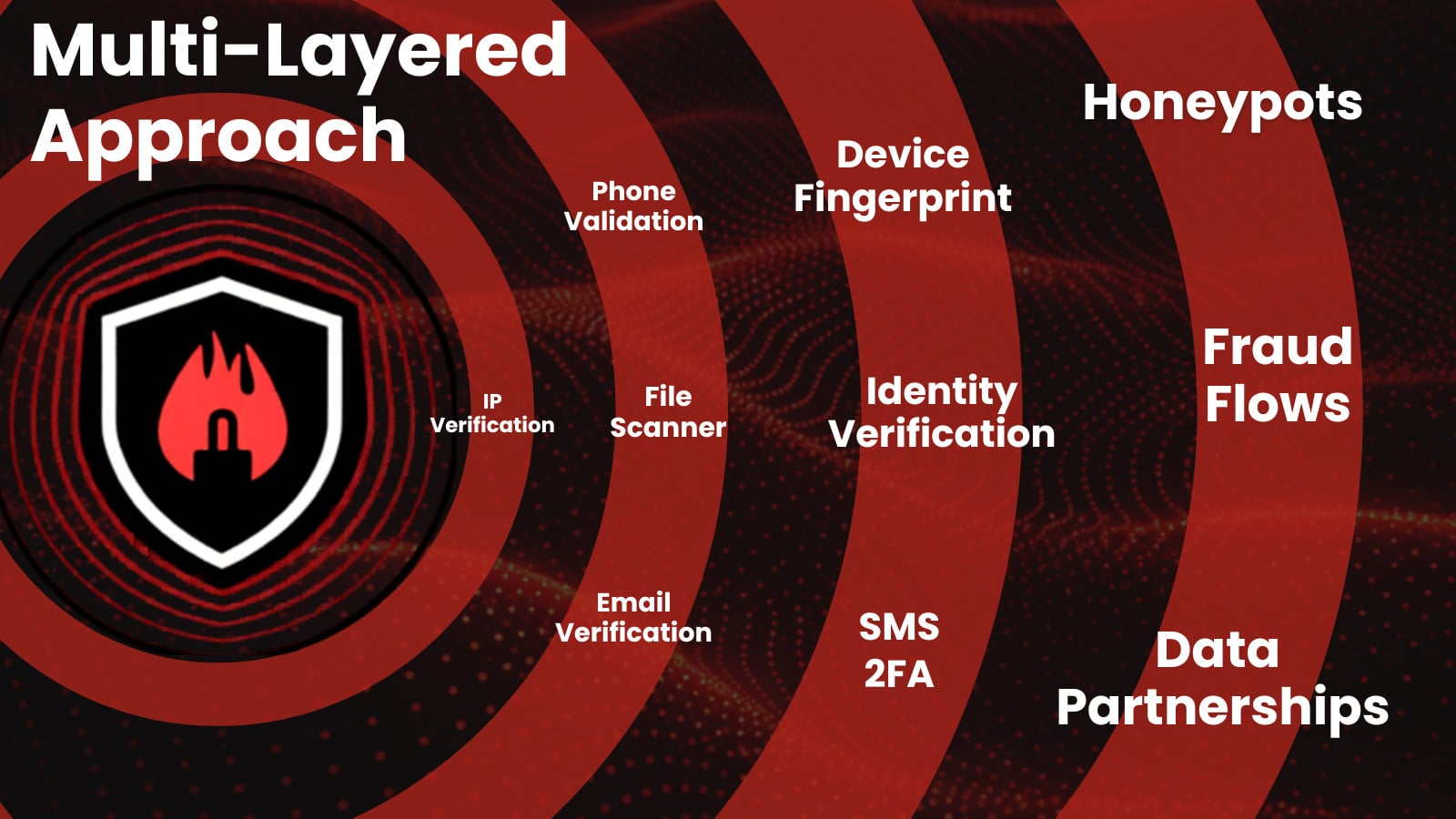
Efficient fraud protection comes from correlating IP, id, machine, and behavioral indicators at each step of the journey as an alternative of evaluating every one in isolation.
An IP that appears barely suspicious by itself turns into clearly abusive when tied to dozens of recent accounts on the identical machine fingerprint and related behavioral patterns in the course of the first session.
Likewise, a person with an apparently regular machine and clear e mail status can nonetheless be high-risk if login conduct displays credential stuffing patterns or entry follows recognized malware distribution campaigns.
Trendy resolution engines enhance accuracy by weighing lots of or 1000’s of information factors collectively somewhat than implementing inflexible guidelines on a single attribute.
For organizations, meaning unifying what have been as soon as separate views. IP intelligence, machine fingerprinting, id verification, and behavioral analytics ought to feed the identical threat mannequin so that every occasion is scored in context, not as a disconnected log line.
This multi sign strategy is essentially the most dependable technique to increase the bar for attackers whereas decreasing friction for real prospects.
Forestall chargebacks. Cease account takeover. Recuperate income.
Main enterprises use IPQS information to energy their fraud prevention methods, don’t go away your self susceptible. Seamlessly combine with our APIs to scale back friction, forestall extra fraud, and safe your enterprise.
Free Signal Up
Case Examine: Stopping Coordinated Signup Abuse
Think about a self service SaaS platform that provides a beneficiant free tier and trials. Because the product grows, abuse seems within the type of 1000’s of signups used to scrape information, take a look at stolen playing cards, or resell entry below the radar.
Early countermeasures depend on blocking sure IP ranges and apparent disposable e mail domains, however this solely dents the issue and begins to affect small groups and freelancers on shared networks.
By shifting to a multi-signal mannequin, the platform begins scoring signups throughout IP, machine, id, and conduct collectively.
New accounts that reuse the identical machine fingerprint with completely different emails, come from IPs not too long ago seen in automated visitors, or instantly exhibit scripted conduct are grouped into coordinated abuse clusters as an alternative of being evaluated one after the other.
This lets the staff apply exact responses, comparable to difficult solely excessive threat clusters with further verification or silently limiting their capabilities whereas letting low threat signups proceed with out friction.
Over time, suggestions from confirmed abuse and confirmed good customers trains the scoring mannequin, driving down false positives whereas pushing organized attackers to spend extra effort for much less return.
Outpacing Fraud Tendencies
Attackers are not tied to a single instrument or weak level in your stack. They mix proxies, bots, artificial identities, leaked credentials, and malware infrastructure throughout a number of phases, which signifies that single sign defenses will at all times lag behind.
To maintain tempo, fraud groups want correlation throughout IP, id, machine, and conduct in a single coherent threat view somewhat than a group of disconnected checks.
From right here, the dialog shifts to tips on how to operationalize that unified mannequin, combine it into current workflows, and measure its affect on each loss discount and buyer expertise.
E-book a free session with a fraud professional right this moment!
About IPQS
IPQS is a founder-led, self-funded firm constructed on a easy precept: fraud prevention ought to be pushed by actual intelligence and a multi-layered strategy. From day one, we’ve centered on proudly owning the total lifecycle of our expertise—creating and sustaining our personal world information community, honeypots, and fraud intelligence specialists. This strategy offers our prospects a definite benefit: sooner insights, better accuracy, and full transparency into how choices are made. By staying impartial, we prioritize long-term innovation over short-term positive aspects, repeatedly evolving our platform to cease fraud earlier than it begins.
Sponsored and written by IPQS.