Key Insights
- AI is the first demand driver for DeCC, as excessive‑worth datasets like scientific trials, buying and selling alerts, medical information, and proprietary mannequin weights can’t safely enter AI pipelines below centralized belief fashions.
- Confidential knowledge marketplaces and privacy-preserving AI workflows have gotten possible with DeCC, enabling establishments to monetize or share insights from their knowledge with out surrendering uncooked entry or regulatory compliance.
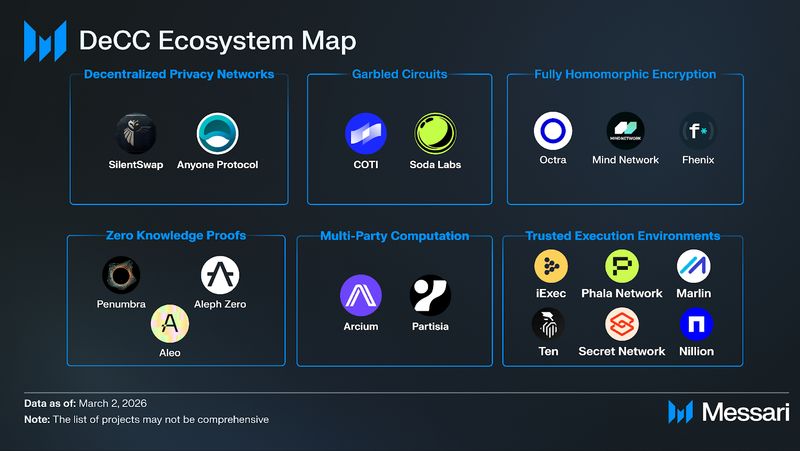
- The DeCC ecosystem has matured right into a multi-hundred-million-dollar class with an trade alliance, almost 30 specialised initiatives, and adoption throughout monetary providers, privateness L1s/L2s, AI infrastructure, and enterprise-focused platforms.
- Rising architectures like NANDA’s “Web3 Quilt” highlights DeCC as a foundational layer for an Web of AI brokers, the place identities, reputations, and computations should span many registries and jurisdictions with out leaking underlying knowledge.
Primer
Customary encryption protects “data at rest” (saved on a disk) and in “transit” (transferring throughout a community), however processing knowledge nonetheless requires decrypting it first, exposing it in plaintext at some point of computation. That is referred to as the “data in use” hole. Decentralized Confidential Computing (DeCC) is a class of know-how that allows blockchain purposes to retailer and compute encrypted knowledge with out revealing it to the community or the general public.
With conventional public blockchains, trustlessness is achieved by means of complete transparency, as all good contract states and transaction inputs are usually seen to everybody. DeCC addresses this limitation by offering a safe infrastructure that retains delicate knowledge encrypted even throughout energetic processing, enabling decentralized purposes to take care of a non-public state onchain.
DeCC eliminates the necessity to belief a single central operator or a clear ledger with delicate info and works by integrating a number of superior cryptographic and hardware-based applied sciences to guard knowledge all through its total lifecycle.
Key technical pillars embrace:
- Trusted Execution Environments (TEEs): {Hardware}-based safe enclaves that isolate and course of delicate knowledge individually from the remainder of the system, defending it even when the working system is compromised.
- Multi-Celebration Computation (MPC): A cryptographic approach that splits knowledge into a number of encrypted shares distributed throughout completely different events, permitting joint computation with out revealing particular person inputs.
- Absolutely Homomorphic Encryption (FHE): An encryption technique that allows computations to be carried out instantly on encrypted knowledge, producing outcomes that stay encrypted and may later be decrypted to disclose the right output.
- Zero-Data Proofs (ZKPs): Cryptographic protocols that enable one celebration to show the validity of a press release to a different with out disclosing any underlying knowledge or secrets and techniques.
- Garbled Circuits (GC): A cryptographic technique that permits a number of events to collectively compute a operate over their non-public inputs with out revealing them.
By combining these instruments, DeCC ensures that at no level through the enter, computation, or output phases does any unauthorized entity achieve entry to the uncooked, delicate info.
AI because the Accelerant
AI has an unresolved knowledge safety downside. Customary encryption secures knowledge at relaxation and in transit, however AI fashions course of it in plaintext for coaching, inference, and fine-tuning, probably exposing delicate inputs to the underlying infrastructure.
At present, high-value datasets like scientific trials, proprietary buying and selling alerts, affected person information, categorised intelligence, and unreleased mannequin weights stay inaccessible to AI because of strict entry controls that stop their use with out publicity. Organizations should both centralize knowledge in trusted cloud environments like AWS Nitro Enclaves or Azure Confidential Computing, accepting counterparty threat, or silo it and forgo the advantages of AI. The choice then turns into extra intense when a number of events have to collaborate. Three pharmaceutical companies can’t collectively prepare a drug-interaction mannequin on mixed affected person knowledge with out one celebration, or a trusted third, seeing all the pieces.
DeCC supplies a 3rd choice by enabling computation over encrypted knowledge. With FHE, a agency can contribute a dataset to a coaching pipeline with out that pipeline ever seeing the info in plaintext. With MPC, a number of organizations can derive insights from pooled knowledge with none single celebration accessing the others’ inputs. With TEEs, AI inference can run in {hardware} enclaves the place even the machine operator can’t observe the workload. These methods enable proprietary knowledge to generate worth by means of AI with out sacrificing confidentiality, making total lessons of datasets that had been beforehand off-limits to mannequin coaching and inference accessible for the primary time.
With AI’s fast adoption throughout Web2 and Web3, fixing this “data in use” vulnerability is changing into pressing. Centralized confidential compute nonetheless requires trusting a single operator to not be compromised, coerced by a authorities, or unilaterally change its phrases of service. This centralized belief mannequin limits how far high-value, multi-party datasets can safely go into AI pipelines, particularly when adversaries, opponents, or cross-border establishments are concerned. DeCC overcomes these constraints by distributing belief throughout unbiased contributors and implementing confidentiality and integrity with cryptography slightly than contracts. By guaranteeing no single operator can entry the info, observe workloads, or unilaterally intrude with computation, DeCC supplies a extra resilient basis for AI that should function on delicate knowledge at scale.
DeCC Use Circumstances
Information as an Asset
A monetary establishment’s mortgage guide, distilled from a long time of proprietary transaction historical past, is commonly a stronger predictor of credit score threat than any public benchmark. A hospital’s imaging archive, constructed from years of scientific observe, can energy diagnostic fashions that far outperform these skilled on open medical datasets. The worth of those belongings depends upon holding them unique and below tight management.
DeCC lets establishments put this sort of confidential knowledge to work with out giving it away. Utilizing methods like FHE and MPC, a financial institution can contribute encrypted transaction histories to a shared fraud detection mannequin, and a analysis hospital can embrace encrypted affected person information in a multi-site scientific examine. In each instances, the info is utilized in computation however by no means uncovered in plaintext to different contributors or the underlying infrastructure.
This unlocks the potential for true confidential knowledge marketplaces, the place knowledge house owners monetize entry to insights derived from their info whereas retaining full custody of the uncooked asset. In distinction to immediately’s digital economic system, the place promoting knowledge normally means completely surrendering management, DeCC allows a mannequin during which knowledge can stay each protected and productively deployed.
Defending Customers and Shoppers
The 2024 Change Healthcare knowledge breach uncovered medical information for tens of hundreds of thousands of People and was one of many largest healthcare knowledge breaches in U.S. historical past. The breach was made attainable as a result of medical information had been processed in plaintext on centralized infrastructure.
Nonetheless, if medical information are processed utilizing FHE or executed inside a TEE, the infrastructure dealing with them by no means holds a decryptable copy, thus there may be nothing value stealing. The identical logic applies to all sorts of confidential knowledge.
For blockchain purposes particularly, DeCC closes a niche that has restricted onchain adoption amongst mainstream customers. Public blockchains are clear and readable to anybody operating a node, which is a function for settlement finality and auditability, however is incompatible with privateness expectations for monetary transactions, well being knowledge, and identification. DeCC allows onchain purposes to inherit the belief ensures of blockchain with out requiring customers to publish all of their delicate knowledge instantly onchain.
Compliance
One of many least seen however strongest brakes on knowledge collaboration is regulatory fragmentation. Monetary establishments, healthcare suppliers, and platforms should navigate overlapping regimes, resembling GDPR in Europe, MiCA for digital belongings, SEC oversight in the USA, and a rising net of native knowledge sovereignty and sector-specific guidelines. These frameworks typically pull in several instructions, forcing organizations to decide on between underusing their knowledge or taking up authorized and reputational threat.
DeCC affords a approach to reconcile collaboration with compliance slightly than forcing a tradeoff. Enabling computation over encrypted knowledge permits establishments in several jurisdictions to take part in shared analytics or mannequin coaching with out ever disclosing uncooked information or transferring plaintext knowledge throughout borders. For instance, a European financial institution and a U.S. financial institution can collectively construct a fraud detection mannequin utilizing an MPC protocol during which every contributes encrypted transaction knowledge. On this situation, the ensuing mannequin is shared, however neither establishment ever sees the opposite’s underlying knowledge, and no plaintext crosses jurisdictions.
For regulators, this creates a brand new enforcement floor. They’ll require that sure checks, controls, or reporting computations be run in verifiable confidential environments, with cryptographic assurances that guidelines had been adopted, with out demanding bulk knowledge entry. On this sense, compliance turns into a local use case for DeCC, turning privacy-preserving infrastructure right into a device that helps establishments fulfill regulatory obligations whereas unlocking cross-border, multi-party collaboration that might in any other case be unattainable.
The DeCC Ecosystem
The DeCC Alliance, fashioned in July 2024, has grown to almost 30 members, with founding contributors together with Aleo, Arcium, Automata, Fairblock, Fhenix, iExec, Inco, Integritee, Marlin, Thoughts Community, Oasis, Partisia, Phala, Secret Community, TEN, Ternoa, and Zama. Cumulative funding within the sector, together with enterprise capital, token allocations, ecosystem funds, and public sale proceeds, approaches $1 billion.
Monetary Companies
HSBC and Citibank use FHE for personal asset tokenization, the place transactions stay confidential whereas nonetheless totally auditable by regulators. Since 2020, ING has used zero-knowledge vary proofs (ZKRPs) in mortgage processing, permitting the financial institution to confirm borrower particulars whereas preserving the privateness of delicate monetary info.
Fhenix has emerged as a number one FHE infrastructure supplier with purposes spanning institutional finance and DeFi. Its CoFHE coprocessor went reside on Base on February 5, 2026, offloading FHE operations from the primary blockchain to enhance effectivity with out compromising decentralization. On December 30, 2025, Fhenix additionally launched its Decomposable BFV scheme, which vastly reduces the price of performing arithmetic on encrypted knowledge, thus making DeCC extra scalable. Its broader ecosystem consists of confidential lending and personal buying and selling purposes, with a give attention to DeFi, confidential transactions, and privacy-preserving AI.
Zama, a confidential blockchain protocol that permits builders to construct privacy-enabled good contracts, already helps a large ecosystem of monetary purposes, together with banking apps like Raycash, stablecoin issuers like Tokenised GBP, and funds networks like Zaïffer.
Blockchains and Rollups
Aleo, a privacy-preserving Layer-1, compiles packages into ZK circuits executed by its SnarkVM. The ecosystem focuses on funds and helps stablecoins resembling USDCx, a USDC-backed non-public stablecoin, and Paxos’ USAD, a privateness stablecoin that shields person balances. On the identification facet, Aleo helps zPass, an identification verification app that doesn’t leak private knowledge. zPass has already secured integrations with GeniiDAO for tutorial credential verification, Three of Cups for personal identification verification, and Humine for medical analysis and scientific trial eligibility proofs.
Aztec, a privacy-focused Ethereum Layer-2, launched its Ignition Chain mainnet on November 19, 2025. Alongside mainnet, the group performed a token sale that raised 19,476 ETH (over $60 million USD) from greater than 16,700 contributors through a Steady Clearing Public sale on Uniswap. The sale used ZkPassport Noir circuits to run sanctions checks whereas preserving participant privateness.
Secret Community runs each good contract inside Intel SGX enclaves, making it one of many unique privacy-native chains. In November 2025, the community deployed a 2B-parameter “Solidity-LLM” inside SecretVM for personal good contract improvement and auditing. Secret’s DeFi ecosystem consists of the Shade Protocol suite and privacy-preserving NFTs through Stashh, with partnerships together with Webisoft for darkish pool buying and selling and Fluid Tokens for collateralized lending. On the AI agent facet, Secret has fashioned partnerships with Aethir, Eliza OS, Zekret, and Kuvi.ai for verifiable agent infrastructure. Complete funding within the community stands at upwards of $400 million.
COTI, in partnership with Soda Labs, implements garbled circuits onchain as an Ethereum Layer-2 privateness overlay throughout over 70 networks. Penumbra operates as a Cosmos-based privateness zone for DeFi, supporting shielded swaps and MEV-resistant buying and selling.
Id, Compliance, and Selective Disclosure
One among DeCC’s extra sensible capabilities is selective disclosure: proving a property about your self with out revealing the underlying knowledge. A person can show they’re over 18 with out disclosing their birthdate, or show they don’t seem to be on a sanctions checklist with out revealing their identification.
A number of of the initiatives coated above are constructing on this functionality. Aleo’s zPass (described within the Blockchains and Rollups part) handles credential verification for tutorial, medical, and identification use instances. Aztec’s ZkPassport demonstrated compliance-grade sanctions screening throughout its token sale. Secret Community has pursued decentralized identification initiatives, together with partnering with DataHaven to create an end-to-end privateness pipeline for storing, computing on, and validating delicate knowledge with out public disclosure.
AI and Confidential Compute
Phala Community is a decentralized confidential computing platform that makes use of TEE-based infrastructure to allow privacy-preserving good contract execution, AI inference, and offchain computation. Based in 2019, Phala constructed one of many largest decentralized TEE networks earlier than pivoting in 2025 towards full-stack confidential AI infrastructure and becoming a member of NVIDIA’s Inception Program. On January 29, 2026, Phala shipped ERC-8004 agent deployment, a normal that extends agent-to-agent protocols with a Web3 belief layer, enabling onchain agent identification, discovery, and TEE-backed attestation.
Thoughts Community is an FHE-based belief and safety layer for autonomous AI agent economies, backed by Binance Labs, Animoca Manufacturers, and Chainlink, with two Ethereum Basis grants for FHE analysis. Its “AgenticWorld” framework allows AI brokers to transact and collaborate on encrypted knowledge. In 2025, Thoughts Community grew to become the primary FHE venture built-in by DeepSeek through its FHE Rust SDK, signed an MOU with BytePlus (ByteDance’s cloud arm) to embed FHE-protected inference into enterprise platforms, partnered with Ant Digital on encrypted RWA messaging, and revealed its x402z Manifesto outlining HTTPZ, a zero-trust web protocol for quantum-resistant, totally encrypted AI computation.
Nillion combines MPC, FHE, and TEEs right into a unified “Blind Compute” stack by means of its Petnet community, enabling non-public AI inference through nilAI and encrypted storage through nilDB. After launching its alpha mainnet and TGE in March 2025, Nillion shipped its Part 1 improve in This fall, introducing nilCC for general-purpose blind computation, and introduced its migration to Ethereum.
iExec is a decentralized cloud platform that executes workloads inside TEEs. Its DataProtector toolkit allows confidential knowledge monetization, whereas a 1 million RLC ecosystem fund helps builder adoption. In This fall 2025, iExec deployed its TEE privateness framework on Arbitrum and launched Core v9.2.0 with bulk multi-dataset processing in TEE classes, a function designed to cut back AI coaching prices whereas preserving knowledge privateness. The venture is now advancing Intel TDX and GPU TEE help for confidential AI inference.
In Q1 2025, Secret Community launched SecretAI, a set of open-source LLM fashions operating inside confidential digital machines powered by NVIDIA H100 and H200 GPUs paired with Intel TDX processors. Just like Phala’s confidential computing infrastructure for AI inference, SecretAI supplies end-to-end privateness throughout inference, immediate historical past, coaching knowledge, and computation, whereas additionally supporting encrypted agentic workloads. Later in November 2025, Secret shipped SecretVM, a general-purpose confidential VM framework that allows builders to deploy customized fashions, brokers, and purposes with hardware-backed privateness and cryptographic verifiability.
Enterprises and Establishments
Partisia Blockchain has collaborated with the Okinawa Institute of Science and Know-how (OIST) on joint cryptographic analysis, making use of MPC-based privateness to enterprise use instances. Partisia raised $50 million in 2021 for this infrastructure.
The Confidential Computing Consortium, whose members embrace Intel, AMD, NVIDIA, Microsoft, and blockchain initiatives like iExec and Secret Community, is focusing in 2026 on delivering technical steerage paperwork to speed up enterprise adoption.
NANDA and the Web3 Quilt
Probably the most forward-looking problem for DeCC lies within the rising “Internet of AI Agents.” The variety of autonomous AI brokers working throughout enterprise and client purposes is rising quick. As agent populations scale from 1000’s to probably billions, they might want to uncover, authenticate, and transact with one another throughout organizational boundaries. No present system handles this.
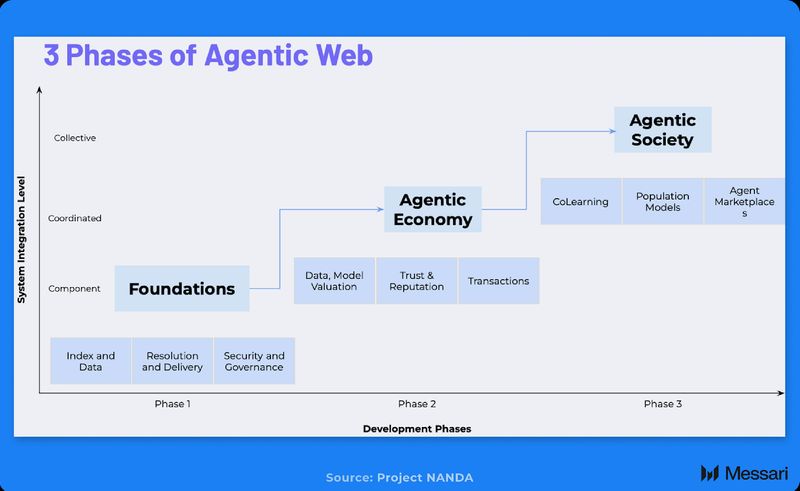
MIT’s Mission NANDA, a Media Lab initiative constructing foundational infrastructure for an web of AI brokers, is setting up the index, protocols, and instruments to handle this. NANDA’s structure facilities on a “Quilt of Registries,” a federation layer that stitches many autonomous agent registries, each Web2 and Web3, into one globally discoverable cloth with out making a single level of management. The NANDA Index resolves agent handles to dynamic, cryptographically verifiable AgentFacts, offering discoverability and authentication at a scale that DNS-centered methods can’t help.
The Superior AI Society (previously Decentralized AI Society) has collaborated with Mission NANDA on the “Web3 Quilt,” the decentralized part of this agent infrastructure. The Web3 Quilt programming, offered at NANDA’s MIT Summit in July 2025, included proposals for an “Index for Decentralized AI Agents” (I4DA) with technical discussions on verifying agent status, identification, and capabilities throughout heterogeneous, decentralized hubs.
With out decentralized status infrastructure, brokers working throughout completely different hubs can create aliases, fragment belief, and undermine accountability. If an agent’s status is barely legitimate inside a single centralized platform, the agentic net turns into a patchwork of walled gardens. Hubs could also be geographical (brokers working below EU versus U.S. regulatory regimes) or topic-based (DeFi brokers versus healthcare brokers), and reputations have to be transportable throughout all of them.
DeCC applied sciences are the pure infrastructure layer right here. MPC allows a number of registries to collectively confirm agent credentials with out exposing their inner knowledge. ZKPs enable brokers to show attributes like compliance standing or historic reliability with out revealing delicate operational particulars. TEEs present hardware-enforced isolation for safe agent execution. This convergence is already being prototyped in NANDA’s Part 3 roadmap, which incorporates “Society of Agents” capabilities, together with co-learning, brokers working throughout knowledge silos with privateness ensures, inhabitants AI, and privacy-preserving machine studying.
Closing Abstract
DeCC started as a response to a slender technical hole— compute on encrypted knowledge with out trusting a single operator—however it has rapidly grown into a definite ecosystem with actual capital, requirements, and manufacturing deployments. It now spans monetary providers, privateness layer-1s and layer-2s, FHE and MPC suppliers, and enterprise-focused networks.
Moreover, the adoption of AI is popping this know-how into an necessary a part of onchain and on-line infrastructure. Fashions are operating up towards knowledge that’s beneficial, regulated, or reputation-sensitive, and centralized confidential computing can’t totally remedy the belief downside when a number of jurisdictions, opponents, or adversarial events are concerned. DeCC lets AI methods prepare and infer on that knowledge with out exposing it, anchoring belief in cryptography and decentralization as an alternative of single operators or authorized jurisdictions.
As DeCC turns into extra extensively adopted, it’s doubtless that establishments like banks will use confidential compute for tokenization and compliance, privateness chains will make shielded belongings and identification proofs routine, DeCC-native platforms will energy non-public AI inference and agent economies, and enterprises will plug zero-trust compute into present stacks. Over time, DeCC is prone to fade as a buzzword and turn into an assumption, underpinning blockchains with non-public state, knowledge marketplaces the place knowledge by no means leaves the proprietor’s management, and AI brokers that act throughout domains with out leaking the info that powers them. In that world, decentralized confidential computing is just not a function however the base layer that retains an AI-driven, globally related economic system usable and protected.