Overview
Kubernetes has basically remodeled how enterprises deploy and handle enterprise workloads. As organizations construct manufacturing functions at scale on Kubernetes, cluster measurement and complexity proceed to develop—creating unprecedented challenges in making certain cluster safety, compliance, and operational consistency.
Kubernetes natively allows builders to deploy workloads declaratively on demand, scale functions dynamically, and iterate quickly. In contrast to conventional IT governance fashions that depend on handbook approval gates, Kubernetes DevSecOps processes have to be automated and embedded immediately into utility growth and supply workflows to raised notice the worth of cloud native. Kubernetes additionally gives policy-based admission management mechanisms akin to Admission Controllers and ValidatingAdmissionPolicy.
Coverage governance frameworks present built-in safety controls based mostly on industry-standard coverage engines. This permits enterprise safety and operations groups to implement widespread governance necessities in a codified and automatic method. Moreover, predefined coverage rule libraries are sometimes accessible to cut back the educational curve of coverage languages and streamline growth and operations workflows.
As Coverage-as-Code turns into extra extensively adopted in manufacturing, a extra versatile answer is required to cowl extra advanced eventualities and obtain a greater stability between coverage enforcement and developer productiveness—Kyverno provides a Kubernetes-native strategy to addressing these challenges.
Why Kyverno?
Kyverno is a Kubernetes-native coverage engine. It makes use of normal CRDs to outline and handle insurance policies, offering an easier and extra user-friendly expertise. Key advantages embody:
- Easy coverage language: Insurance policies are written in normal YAML, according to Kubernetes manifests. There isn’t a have to be taught specialised coverage languages akin to Rego, decreasing the barrier to entry. Kyverno additionally extends the CEL perform library, offering extra capabilities for advanced coverage expressions.
- Wealthy characteristic set: Kyverno natively helps Validate, Mutate, Generate, and Cleanup, protecting a broader vary of automation and Coverage-as-Code eventualities. It additionally gives strong caching mechanisms, exterior knowledge calls, and different capabilities to fulfill enterprise extension wants in particular Coverage-as-Code use instances.
- Complete coverage library: Kyverno helps Kubernetes-native and a number of coverage sorts, and the Kyverno group gives coverage libraries protecting many widespread Kubernetes utility eventualities.
- Standardized governance reporting and observability: Whereas imposing guardrails, enterprises typically place even larger emphasis on the “visibility” of coverage governance as a foundation for repeatedly enhancing cluster safety posture. Kyverno gives a Reporting mechanism aligned with the Kubernetes Coverage Working Group specs, serving to audit whether or not workloads deployed within the cluster adjust to requirements and offering well timed suggestions to builders. Kyverno additionally integrates with normal cloud-native observability instruments and may seamlessly combine with cloud platform observability options.
For example these capabilities, let’s discover how Kyverno addresses widespread manufacturing governance challenges.
Actual-world use instances
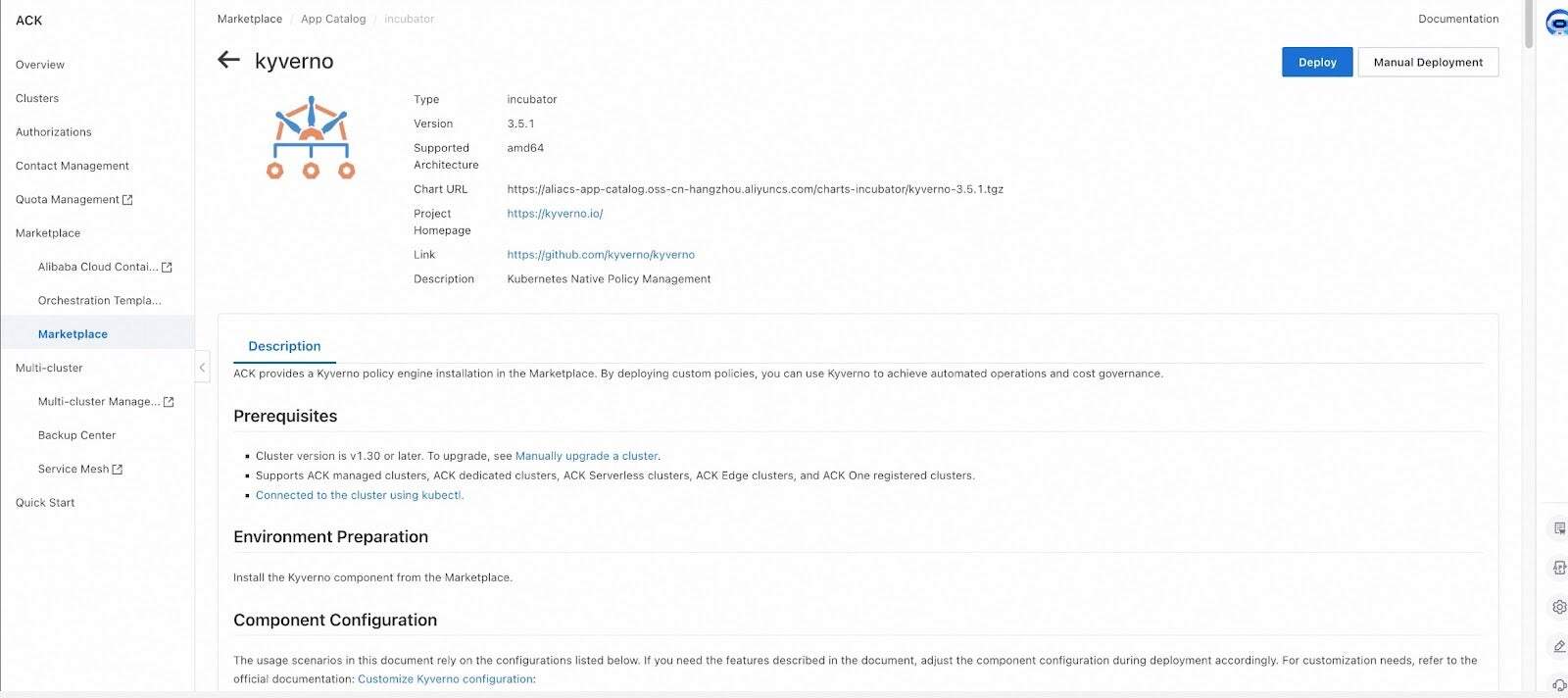
Kyverno gives native assist for Kubernetes and has been built-in by a number of cloud-native coverage governance frameworks. It’s now formally accessible for deployment on Kubernetes clusters by means of normal set up strategies and platform marketplaces.
The next examples reveal how Kyverno addresses widespread manufacturing challenges.
Case 1: Implementing Customized Useful resource (CRD) Deletion Safety
Pushed by enterprise wants, enterprises typically deploy a lot of CRD assets in manufacturing clusters. Stopping unintentional deletion of crucial manufacturing CR cases is a key requirement for safety and operations groups.
Inside cloud-native coverage governance frameworks, pre-built coverage libraries sometimes can not concentrate on customers’ customized useful resource definitions (CRDs). This limitation requires extending by way of external-provider mechanisms and likewise requires customers to jot down and deploy particular insurance policies to finish the workflow.
With Kyverno, this may be achieved utilizing clear YAML expressions—pleasant to cluster operators who’re already aware of Kubernetes manifests. Insurance policies additionally assist fine-grained useful resource matching and exemption mechanisms:
apiVersion: insurance policies.kyverno.io/v1alpha1
sort: ValidatingPolicy
metadata:
title: protect-critical-database-deletion
spec:
autogen:
podControllers:
controllers: []
matchConstraints:
resourceRules:
- apiGroups: ['db.example.com']
apiVersions: ['*']
assets: ['databases']
operations: ['DELETE']
matchConditions:
- title: critical-database-instances
expression: "oldObject.metadata.name in ['critical-db', 'prod-main-db']"
validationActions: ['Deny']
validations:
- expression: "oldObject.metadata.?annotations['kyverno.io/allow-delete'].orValue('') == 'true'"
messageExpression: '''Deletion of crucial database occasion '' + oldObject.metadata.title + '' just isn't allowed until annotated with kyverno.io/allow-delete: "true"'''
Case 2: Auto-mutating runAsNonRoot and producing community insurance policies
In manufacturing operations, routinely making use of associated useful resource modifications, including labels/annotations, and dynamically hardening safety for particular actions are widespread necessities. Through the use of a coverage engine along with Kubernetes mutating admission capabilities, enterprises can shift these processes from handbook operations to automation.
Kyverno gives a extra user-friendly mutation expertise. Builders can carry out useful resource mutations in an easy approach utilizing easy YAML patch operations. It additionally helps:
- Masking current assets: Scan, report on, mutate, and generate for current assets within the cluster.
- Computerized technology of associated assets: Routinely create associated assets akin to NetworkPolicies and ConfigMaps based mostly on insurance policies to allow automated configuration.
The next is a typical instance of automating a secure-by-default baseline. With the MutatingPolicy beneath, runAsNonRoot is routinely added to the Pod securityContext when Pods are created:
apiVersion: insurance policies.kyverno.io/v1alpha1
sort: MutatingPolicy
metadata:
title: add-pod-run-as-non-root
spec:
matchConstraints:
resourceRules:
- apiGroups: ['']
apiVersions: ['v1']
operations: ['CREATE', 'UPDATE']
assets: ['pods']
mutations:
- patchType: ApplyConfiguration
applyConfiguration:
expression: >-
Object{
spec: Object.spec{
securityContext: Object.spec.securityContext{
runAsNonRoot: has(object.spec.securityContext) && has(object.spec.securityContext.runAsNonRoot)
? object.spec.securityContext.runAsNonRoot
: true
}
}
}
The GeneratingPolicy beneath allows routinely creating namespace-scoped assets when a Namespace is created or up to date:
apiVersion: insurance policies.kyverno.io/v1alpha1
sort: GeneratingPolicy
metadata:
title: add-networkpolicy
annotations:
insurance policies.kyverno.io/title: Add Community Coverage
insurance policies.kyverno.io/topic: NetworkPolicy
insurance policies.kyverno.io/minversion: 1.15.0
spec:
analysis:
synchronize:
enabled: true
matchConstraints:
resourceRules:
- apiGroups: ['']
apiVersions: ['v1']
operations: ['CREATE', 'UPDATE']
assets: ['namespaces']
variables:
- title: targetNs
expression: 'object.metadata.title'
- title: downstream
expression: >-
[
{
"kind": dyn("NetworkPolicy"),
"apiVersion": dyn("networking.k8s.io/v1"),
"metadata": dyn({
"name": "default-deny",
}),
"spec": dyn({
"podSelector": dyn({}),
"policyTypes": dyn(["Ingress", "Egress"])
})
}
]
generate:
- expression: generator.Apply(variables.targetNs, variables.downstream)
The Kyverno group’s insurance policies undertaking gives consultant insurance policies throughout a variety of Kubernetes utility eventualities and greatest practices. readers can discover it to find extra prospects with Kyverno.
Clever Insurance policies × Safety Governance Closed Loop
Within the evolution of cloud-native safety governance, Kyverno and AI Brokers transcend a unidirectional toolchain—they type golden companions in establishing a dynamic “Perceive-Decide-Protect-Evolve” closed-loop system.
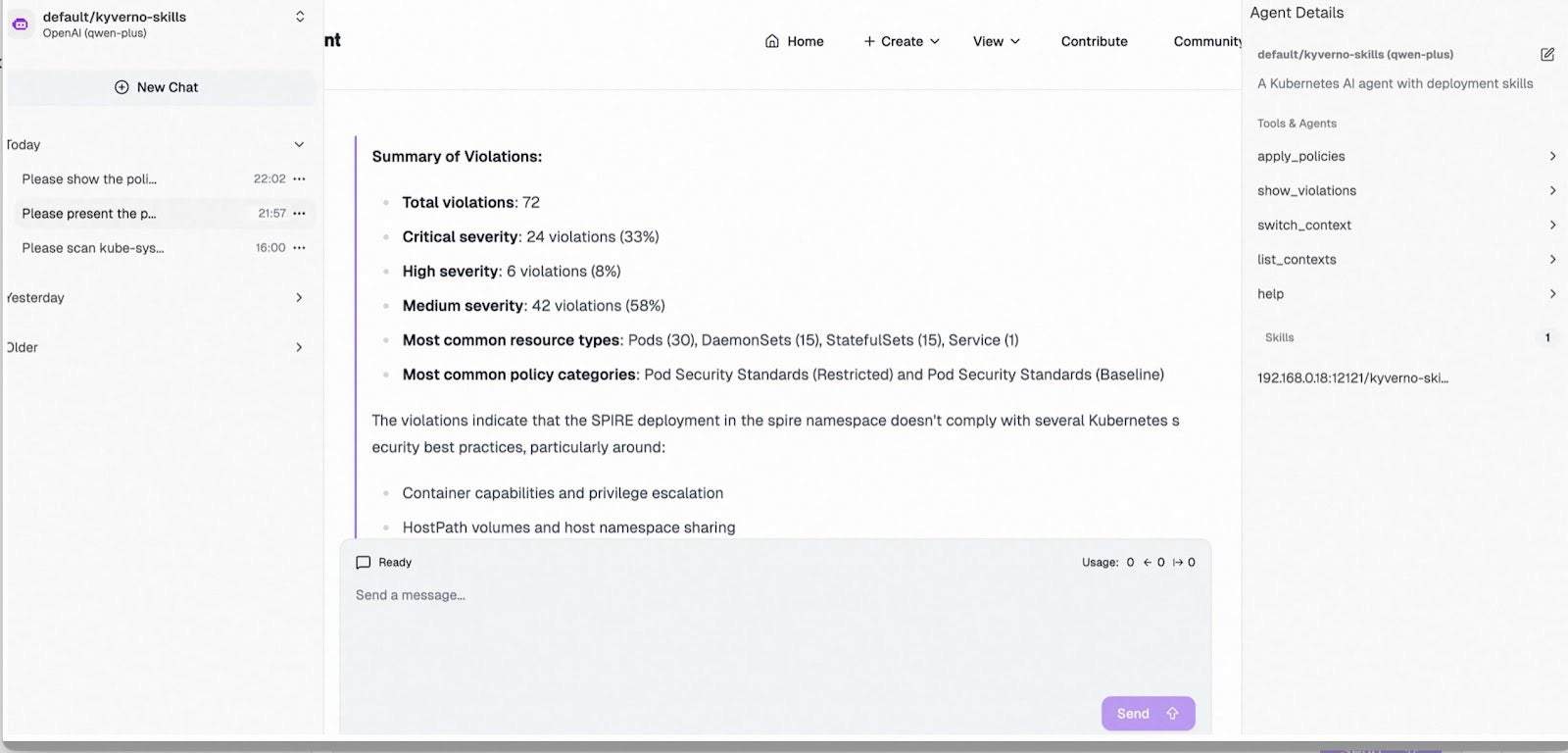
AI Agent Empowers Kyverno: From “Policy Configuration” to “Intelligent Governance”
Leveraging MCP/Expertise built-in throughout the Agent and powered by LLM, SecOps groups can obtain one-click deployment of Kyverno alongside coverage units tailor-made for typical eventualities. The answer routinely scans workload configurations throughout outlined cluster scopes for numerous compliance and baseline necessities, producing visualized safety posture studies to exactly establish high-risk parts (e.g., privileged containers, delicate quantity mounts) and misconfigured authorizations. This transforms conventional “manual inspections” into “minute-level intelligent insights,” enabling safety coverage design with each foresight and precision.
Fashionable Kubernetes clusters assist automated set up, deployment, and configuration capabilities for Kagent. Cluster safety personnel can streamline the end-to-end lifecycle of constructing, deploying, and managing AI Brokers inside Kubernetes environments. Primarily based on standardized MCP/Expertise specs, groups flexibly develop and function Kyverno policy-focused Brokers and MCP Servers immediately in-cluster.
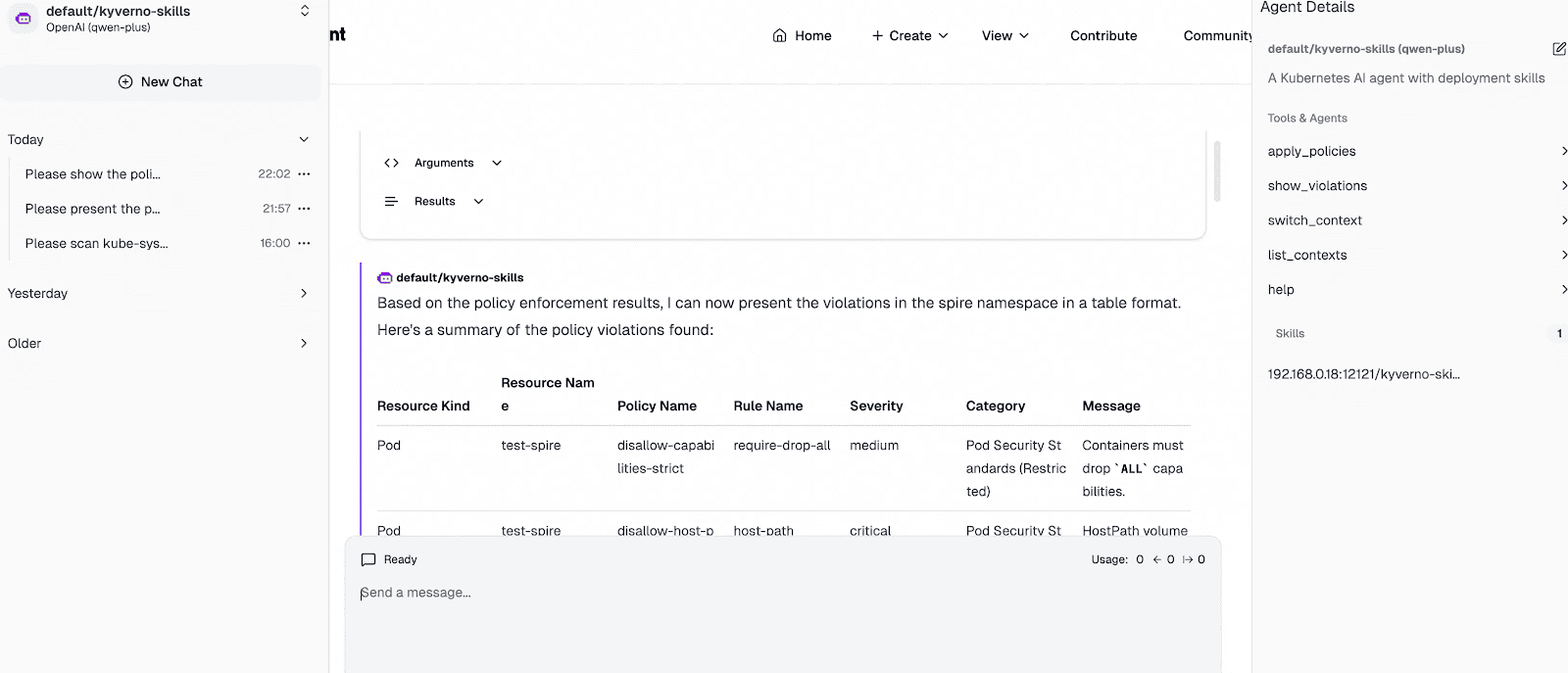
The determine beneath illustrates a Kyverno Agent occasion deployed within the cluster. Built-in with Instruments from kyverno-mcp, it helps context loading and switching throughout multi-cluster environments and allows coverage governance inspection by way of the kyverno CLI for speedy safety and compliance threat detection. Enhanced with Kyverno-specific Expertise, the Agent optimizes coverage governance workflows: as demonstrated within the interplay snapshot, it swiftly invokes Instruments to guage namespace-level dangers in opposition to best-practice coverage units, in the end delivering tabular compliance studies and consolidated violation summaries.
Kyverno Safeguards AI Brokers: From “Risk Prevention” to “Secure Operation”
When AI Brokers, related MCP Servers, and gateway containers are deployed throughout the cluster, Kyverno insurance policies immediately step in because the vigilant "security gatekeeper":
- Actual-time interception of high-risk configurations: Routinely audit or reject Agent Pods launched with privileged mode, root privileges, lacking securityContext, or mounting delicate host directories.
- Nice-grained AI gateway authorization: Leveraging Envoy’s Exterior Authorization mechanism, Kyverno insurance policies empower AI gateways to implement identity-aware authorization, attaining fine-grained entry management over AI inbound visitors.
- Closed-loop hardening and remediation: Upon threat detection, Kyverno not solely blocks non-compliant deployments but in addition delivers automated hardening and remediation templates—making certain Brokers function as safe, ruled utility items throughout the cluster, not assault vectors.
In as we speak’s period of deep AI and cloud-native convergence, Brokers infuse Kyverno insurance policies with contextual intelligence, whereas Kyverno empowers Brokers with operational belief—collectively closing the loop on a dynamically evolving, self-reinforcing safety framework.
Conclusion
Within the cloud-native period, safety and effectivity are not a binary trade-off. Kyverno brings coverage governance nearer to the Kubernetes person expertise by expressing validation, mutation, technology, and cleanup logic in Kubernetes-native assets, enabling groups to implement requirements whereas preserving workflows easy and scalable.
Trying forward, the Kyverno group will proceed working with cloud distributors to advance interoperable governance capabilities throughout numerous environments. By co-building open coverage libraries, standardized reporting and observability, and seamless integrations with vendor platforms and toolchains, organizations can set up constant safety and compliance baselines – making coverage governance a shared, repeatable basis for cloud-native operations.