North Korean hackers are deploying newly uncovered instruments to maneuver knowledge between internet-connected and air-gapped programs, unfold by way of detachable drives, and conduct covert surveillance.
The malicious marketing campaign has been named Ruby Jumper and is attributed to the state-backed group APT37, also referred to as ScarCruft, Ricochet Chollima, and InkySquid.
Air-gapped computer systems are disconnected from exterior networks, particularly the general public web. Bodily isolation is achieved on the {hardware} stage by eradicating all connectivity (Wi-Fi, Bluetooth, Ethernet), whereas logical segregation depends on numerous software-defined controls, like VLANs and firewalls.

In a bodily air-gap setting, typical in important infrastructure, army, and analysis sectors, knowledge switch is completed by way of detachable storage drives.
Researchers at cloud safety firm Zscaler analyzed the malware employed in APT37’s Ruby Jumper marketing campaign and recognized a toolkit of 5 malicious instruments: RESTLEAF, SNAKEDROPPER, THUMBSBD, VIRUSTASK, and FOOTWINE.
Bridging the air hole
The an infection chain begins when the sufferer opens a malicious Home windows shortcut file (LNK), which deploys a PowerShell script that extracts payloads embedded within the LNK file. To divert consideration, the script additionally launches a decoy doc.
Though the researchers didn’t specify any victims, they notice that the doc is an Arabic translation of a North Korean newspaper article in regards to the Palestine-Israel battle.
The PowerShell script hundreds the primary malware part, known as RESTLEAF, an implant that communicates with APT37’s command-and-control (C2) infrastructure utilizing Zoho WorkDrive.
RESTLEAF fetches encrypted shellcode from the C2 to obtain the next-stage payload, a Ruby-based loader named SNAKEDROPPER.
The assault continues with putting in the Ruby 3.3.0 runtime setting – full with the interpreter, commonplace libraries, and gem infrastructure – disguised as a official USB-related utility named usbspeed.exe.
“SNAKEDROPPER is primed for execution by replacing the RubyGems default file operating_system.rb with a maliciously modified version that is automatically loaded when the Ruby interpreter starts,” by way of a scheduled activity (rubyupdatecheck) that executes each 5 minutes, the researchers say.
The THUMBSBD backdoor is downloaded as a Ruby file named ascii.rb, in addition to the VIRUSTASK malware because the bundler_index_client.rb file.
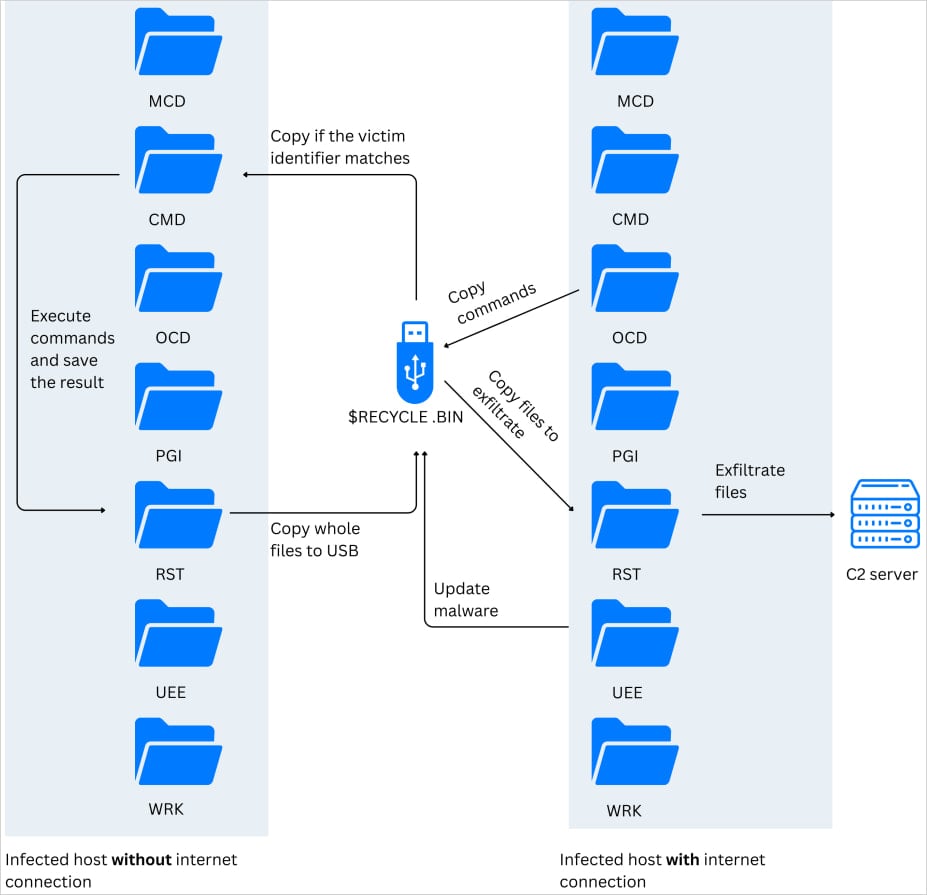
The function of THUMBSBD is to gather system data, stage command information, and put together knowledge for exfiltration. Its most important operate is to create hidden directories on detected USB drives and replica information to them.
In line with the researchers, the malware turns detachable storage gadgets “into a bidirectional covert C2 relay.” This enables the risk actor to ship instructions to air-gapped programs in addition to extract knowledge from them.
Supply: Zscaler
“By leveraging removable media as an intermediary transport layer, the malware bridges otherwise air-gapped network segments,” Zscaler researchers say.
VIRUSTASK’s function is to unfold the an infection to new air-gapped machines, weaponizing detachable drives by hiding official information and changing them with malicious shortcuts that execute the embedded Ruby interpreter when opened.
The module will solely set off an an infection course of if the inserted detachable media has a minimum of 2GB of free area.
.jpg)
Supply: Zscaler
Zscaler stories that THUMBSBD additionally delivers FOOTWINE, a Home windows adware backdoor disguised as an Android package deal file (APK) that helps keylogging, screenshot seize, audio and video recording, file manipulation, registry entry, and distant shell instructions.
One other piece of malware additionally noticed within the APT37’s RubyJumper marketing campaign is BLUELIGHT, a full-fledged backdoor beforehand related to the North Korean risk group.
Zscaler has excessive confidence attributing the RubyJumper marketing campaign to APT37 based mostly on a number of indicators, together with using the BLUELIGHT malware, preliminary vector counting on LNK information, two-stage shellcode supply approach, and C2 infrastructure sometimes noticed in assaults from this actor.
The researchers additionally notice that the decoy doc signifies that the goal of the RubyJumper exercise is excited by North Korean media narratives, which aligns with the sufferer profile of this risk group.

Trendy IT infrastructure strikes sooner than handbook workflows can deal with.
On this new Tines information, find out how your workforce can scale back hidden handbook delays, enhance reliability by way of automated response, and construct and scale clever workflows on prime of instruments you already use.



