Apple account change notifications are being abused to ship pretend iPhone buy phishing scams inside reputable emails despatched from Apple’s servers, rising legitimacy and probably permitting them to bypass spam filters.
A reader shared an e-mail with BleepingComputer that seemed to be a regular Apple safety notification that acknowledged their account info had been up to date.
Nonetheless, embedded inside the message was a phishing lure claiming that an $899 iPhone buy had been made through PayPal, together with a telephone quantity to name to cancel the transaction.

“Dear User 899 USD iPhone Purchase Via Pay-Pal To Cancel 18023530761,” reads the Apple account phishing e-mail.
“The following changes to your Apple Account, hxfedna24005@icloud.com, were made on April 14, 2026 at 7:01:40 PM GMT:”
“Shipping Information”
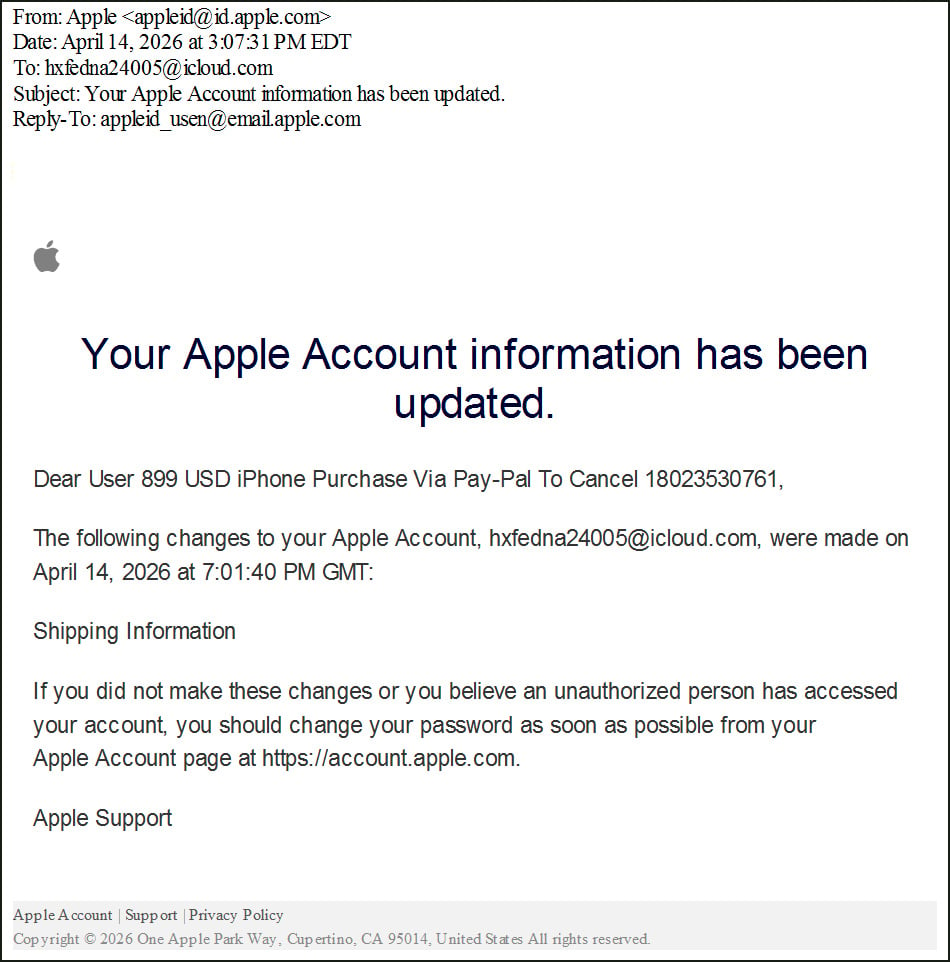
Supply: BleepingComputer
These emails are designed to trick recipients into pondering their accounts had been used for fraudulent purchases and scare them into calling the scammer’s “support” quantity.
When calling the quantity, scammers usually attempt to persuade victims that their accounts have been compromised and will instruct them to put in distant entry software program or present monetary info.
In earlier callback phishing campaigns, this distant entry has been used to steal funds from financial institution accounts, deploy malware, or steal information.
Abusing Apple account notifications
Whereas the phishing lure isn’t new, the marketing campaign illustrates how risk actors proceed to evolve their ways by exploiting reputable web site options to conduct assaults.
The phishing e-mail was despatched from Apple’s infrastructure utilizing the deal with appleid@id.apple.com and handed SPF, DKIM, and DMARC authentication checks, indicating it was a reputable e-mail from Apple.
dkim=go header.d=id.apple.com header.i=@id.apple.com header.b=o3ICBLWN
spf=go (spf.icloud.com: area of uatdsasadmin@e-mail.apple.com designates 17.111.110.47 as permitted sender) smtp.mailfrom=uatdsasadmin@e-mail.apple.com
Additional evaluation of the e-mail headers reveals that the message originated from Apple mail infrastructure and was not spoofed.
Preliminary server: rn2-txn-msbadger01107.apple.com
Outbound relay: outbound.mr.icloud.com
IP deal with: 17.111.110.47 (Apple-owned)To conduct the assault, the risk actor creates an Apple ID and inserts the phishing message into the account’s private info fields, splitting the textual content throughout the primary and final identify fields.
BleepingComputer was in a position to replicate this habits by making a check Apple account and including comparable callback phishing language to the primary and final identify fields. That is as a result of every area can’t include the whole rip-off message.
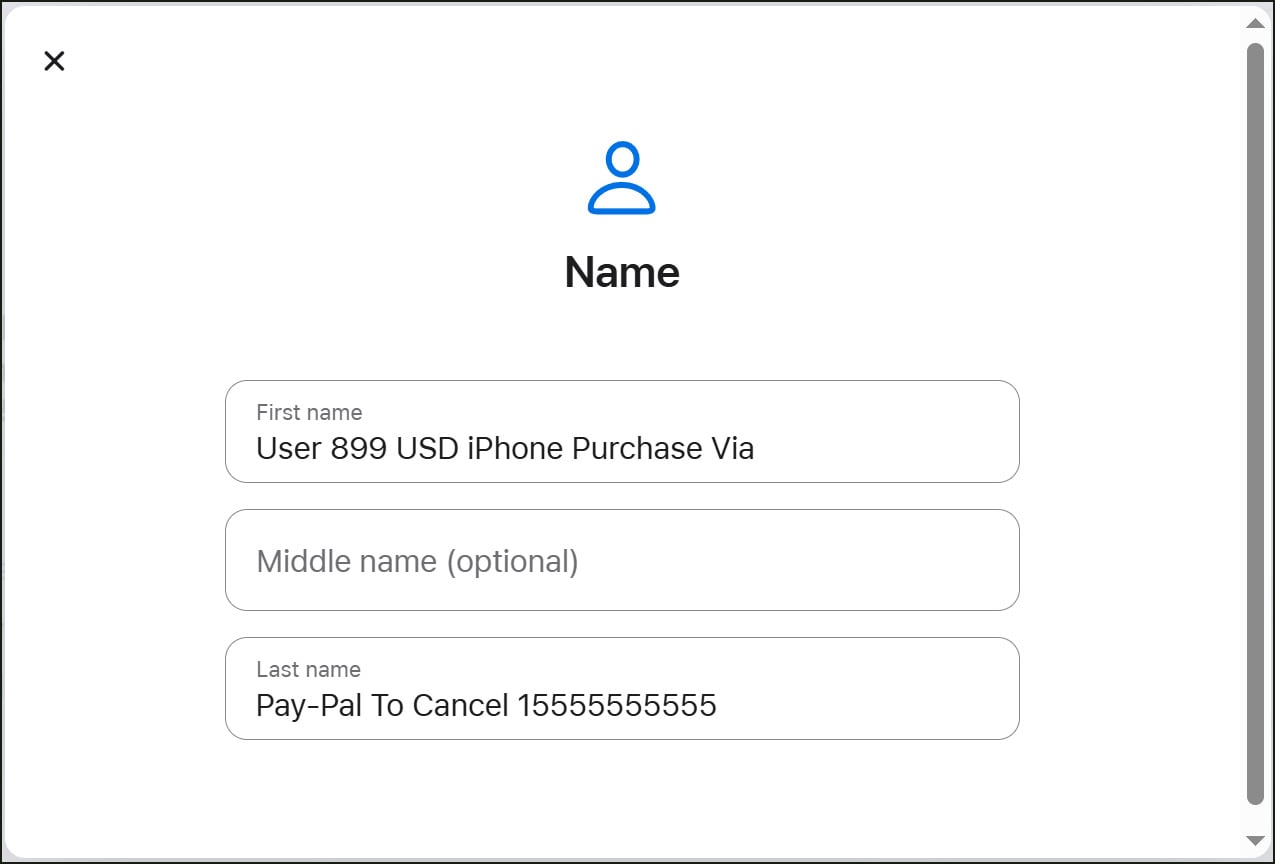
Supply: BleepingComputer
To set off the Apple account profile change notification, the attacker modifies the account’s delivery info, which causes Apple to ship a safety alert notifying the consumer of the change.
As a result of Apple consists of the user-supplied first and final identify fields inside these notifications, the phishing message is embedded immediately into the e-mail and delivered as a part of a reputable alert.
Whereas the goal of the assaults obtained the message, the e-mail was initially despatched to an iCloud e-mail deal with related to the attacker’s account. This e-mail deal with can also be included within the notification e-mail, making the e-mail look extra regarding and probably main somebody to consider the account was hacked.
Header evaluation reveals that the unique recipient differs from the ultimate supply deal with, indicating that the attacker is probably going utilizing a mailing listing to distribute the emails to a number of targets.
This marketing campaign is much like a earlier phishing marketing campaign that abused iCloud Calendar invitations to ship pretend buy notifications by Apple’s servers.
As a normal rule, customers ought to deal with surprising account alerts claiming purchases or urging them to name help numbers with warning, particularly if they didn’t provoke any current adjustments or in the event that they include uncommon e-mail addresses.
BleepingComputer contacted Apple on Friday about this marketing campaign, however didn’t obtain a response, and the abuse remains to be attainable.

AI chained 4 zero-days into one exploit that bypassed each renderer and OS sandboxes. A wave of latest exploits is coming.
On the Autonomous Validation Summit (Could 12 & 14), see how autonomous, context-rich validation finds what’s exploitable, proves controls maintain, and closes the remediation loop.



