An elusive hacker who glided by the deal with “UNKN” and ran the early Russian ransomware teams GandCrab and REvil now has a reputation and a face. Authorities in Germany say 31-year-old Russian Daniil Maksimovich Shchukin headed each cybercrime gangs and helped perform not less than 130 acts of laptop sabotage and extortion in opposition to victims throughout the nation between 2019 and 2021.
Shchukin was named as UNKN (a.ok.a. UNKNOWN) in an advisory revealed by the German Federal Prison Police (the “Bundeskriminalamt” or BKA for brief). The BKA mentioned Shchukin and one other Russian — 43-year-old Anatoly Sergeevitsch Kravchuk — extorted almost $2 million euros throughout two dozen cyberattacks that brought about greater than 35 million euros in whole financial injury.
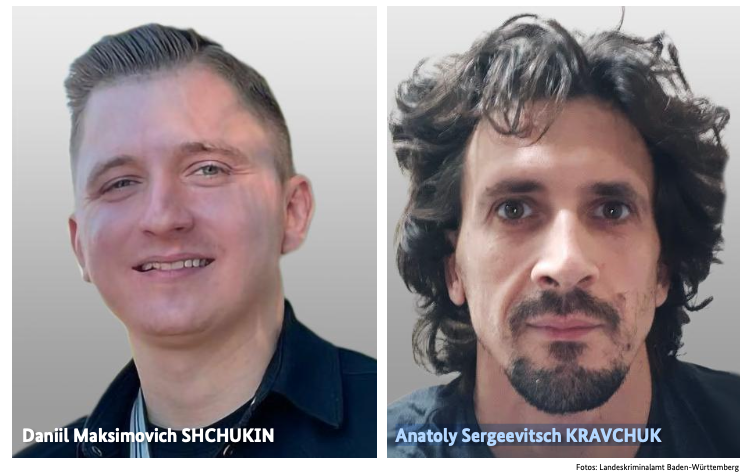
Daniil Maksimovich SHCHUKIN, a.ok.a. UNKN, and Anatoly Sergeevitsch Karvchuk, alleged leaders of the GandCrab and REvil ransomware teams.
Germany’s BKA mentioned Shchukin acted as the top of one of many largest worldwide working ransomware teams GandCrab and REvil, which pioneered the apply of double extortion — charging victims as soon as for a key wanted to unlock hacked techniques, and a separate fee in trade for a promise to not publish stolen knowledge.
Shchukin’s title appeared in a Feb. 2023 submitting (PDF) from the U.S. Justice Division looking for the seizure of assorted cryptocurrency accounts related to proceeds from the REvil ransomware gang’s actions. The federal government mentioned the digital pockets tied to Shchukin contained greater than $317,000 in ill-gotten cryptocurrency.
The Gandcrab ransomware associates program first surfaced in January 2018, and paid enterprising hackers big shares of the earnings only for hacking into consumer accounts at main firms. The Gandcrab group would then attempt to develop that entry, usually siphoning huge quantities of delicate and inner paperwork within the course of. The malware’s curators shipped 5 main revisions to the GandCrab code, every corresponding with sneaky new options and bug fixes aimed toward thwarting the efforts of laptop safety corporations to stymie the unfold of the malware.
On Might 31, 2019, the GandCrab group introduced the group was shutting down after extorting greater than $2 billion from victims. “We are a living proof that you can do evil and get off scot-free,” GandCrab’s farewell deal with famously quipped. “We have proved that one can make a lifetime of money in one year. We have proved that you can become number one by general admission, not in your own conceit.”
The REvil ransomware associates program materialized across the similar as GandCrab’s demise, fronted by a consumer named UNKNOWN who introduced on a Russian cybercrime discussion board that he’d deposited $1 million within the discussion board’s escrow to indicate he meant enterprise. By this time, many cybersecurity consultants had concluded REvil was little greater than a reorganization of GandCrab.
UNKNOWN additionally gave an interview to Dmitry Smilyanets, a former malicious hacker employed by Recorded Future, whereby UNKNOWN described a rags-to-riches story unencumbered by ethics and morals.
“As a child, I scrounged through the trash heaps and smoked cigarette butts,” UNKNOWN informed Recorded Future. “I walked 10 km one way to the school. I wore the same clothes for six months. In my youth, in a communal apartment, I didn’t eat for two or even three days. Now I am a millionaire.”
As described in The Ransomware Looking Staff by Renee Dudley and Daniel Golden, UNKNOWN and REvil reinvested vital earnings into bettering their success and mirroring practices of reliable companies. The authors wrote:
“Just as a real-world manufacturer might hire other companies to handle logistics or web design, ransomware developers increasingly outsourced tasks beyond their purview, focusing instead on improving the quality of their ransomware. The higher quality ransomware—which, in many cases, the Hunting Team could not break—resulted in more and higher pay-outs from victims. The monumental payments enabled gangs to reinvest in their enterprises. They hired more specialists, and their success accelerated.”
“Criminals raced to join the booming ransomware economy. Underworld ancillary service providers sprouted or pivoted from other criminal work to meet developers’ demand for customized support. Partnering with gangs like GandCrab, ‘cryptor’ providers ensured ransomware could not be detected by standard anti-malware scanners. ‘Initial access brokerages’ specialized in stealing credentials and finding vulnerabilities in target networks, selling that access to ransomware operators and affiliates. Bitcoin “tumblers” supplied reductions to gangs that used them as a most popular vendor for laundering ransom funds. Some contractors had been open to working with any gang, whereas others entered unique partnerships.”
REvil would evolve right into a feared “big-game-hunting” machine able to extracting hefty extortion funds from victims, largely going after organizations with greater than $100 million in annual revenues and fats new cyber insurance coverage insurance policies that had been identified to pay out.
Over the July 4, 2021 weekend in america, REvil hacked into and extorted Kaseya, an organization that dealt with IT operations for greater than 1,500 companies, nonprofits and authorities businesses. The FBI would later announce they’d infiltrated the ransomware group’s servers previous to the Kaseya hack however couldn’t tip their hand on the time. REvil by no means recovered from that core compromise, or from the FBI’s launch of a free decryption key for REvil victims who couldn’t or didn’t pay.
Shchukin is from Krasnodar, Russia and is assumed to reside there, the BKA mentioned.
“Based on the investigations so far, it is assumed that the wanted person is abroad, presumably in Russia,” the BKA suggested. “Travel behaviour cannot be ruled out.”
There may be little that connects Shchukin to UNKNOWN’s varied accounts on the Russian crime boards. However a evaluate of the Russian crime boards listed by the cyber intelligence agency Intel 471 exhibits there may be a lot connecting Shchukin to a hacker id known as “Ger0in” who operated giant botnets and bought “installs” — permitting different cybercriminals to quickly deploy malware of their option to 1000’s of PCs in a single go. Nevertheless, Ger0in was solely lively between 2010 and 2011, effectively earlier than UNKNOWN’s look because the REvil entrance man.
A evaluate of the mugshots launched by the BKA on the picture comparability website Pimeyes discovered a match on this birthday celebration from 2023, which includes a younger man named Daniel carrying the identical fancy watch as within the BKA pictures.

Photographs from Daniil Shchukin’s party celebration in Krasnodar in 2023.