Flare researchers monitoring underground Telegram channels and cybercrime boards have noticed menace actors quickly sharing proof-of-concept exploits, offensive instruments, and stolen administrator credentials associated to not too long ago disclosed SmarterMail vulnerabilities, offering perception into how rapidly attackers weaponize new safety flaws.
The exercise occurred inside days of the vulnerabilities being disclosed, with menace actors sharing and promoting exploit code and compromised entry tied to CVE-2026-24423 and CVE-2026-23760, crucial flaws that allow distant code execution and authentication bypass on uncovered e mail servers.
These vulnerabilities have since been confirmed in real-world assaults, together with ransomware campaigns, highlighting how attackers more and more goal e mail infrastructure as an preliminary entry level into company networks, permitting them to maneuver laterally and set up persistent footholds.
CVE-2026-24423 and CVE-2026-23760: Essential RCE and Auth Bypass Flaws
A number of not too long ago disclosed SmarterMail vulnerabilities created an ideal storm that made the platform extremely enticing to attackers. Amongst them, CVE-2026-24423 stands out as a crucial unauthenticated distant code execution flaw affecting variations previous to Construct 9511.
With a CVSS rating of 9.3 and no person interplay required, the flaw is especially fitted to automation, large-scale scanning, and mass exploitation campaigns.
In parallel, extra vulnerabilities CVE-2026-23760 (CVSS 9.3) embody authentication bypass and password reset logic flaws. It permits attackers to reset administrator credentials or achieve privileged entry to the platform. Analysis additionally reveals that attackers have been rapidly reverse-engineering patches to establish and weaponize these weaknesses inside days of launch.
When mixed, these points enabled full server takeover situations, the place attackers might transfer from application-level entry to working system management and doubtlessly domain-level compromise in linked environments.
From an attacker’s perspective, this mix is good: SmarterMail is a network-exposed service, usually holds a excessive belief place inside enterprise environments, and in lots of circumstances is monitored much less aggressively than endpoint techniques protected by EDR.
As soon as proof-of-concept exploit code turns into accessible, exploitation could be quickly operationalized – that means the timeline from vulnerability disclosure to ransomware deployment can shrink to days.
SmarterTools Breached by Personal Product Flaw, Ransomware Teams Comply with
Latest incidents reveal precisely how this pipeline performs out.
In line with a SmarterTools report, SmarterTools was breached in January 2026 after attackers exploited an unpatched SmarterMail server working on an inside VM that was uncovered inside their community.
The compromised atmosphere included workplace and lab networks and a data-center phase linked by way of Lively Listing, the place attackers moved laterally and impacted round a dozen Home windows servers.
The corporate shut down the affected infrastructure, restored techniques from backup, rotated credentials, and eliminated some Home windows/AD dependencies. Having mentioned that, it was reported that core buyer providers and information have been unaffected. Attackers gained an inside community foothold and tried typical ransomware-style post-exploitation actions; it wasn’t profitable, due to community segmentation.
In one other investigation revealed by Bleeping Laptop, ransomware operators gained preliminary entry by way of SmarterMail vulnerabilities and waited earlier than triggering encryption payloads, a traditional affiliate habits sample.
This sample is vital:
- Preliminary entry through e mail server vulnerability
- Credential harvesting or token extraction
- Lateral motion through Lively Listing
- Persistence through scheduled duties or DFIR software abuse
- Ransomware deployment after staging interval
Some campaigns have been linked to the Warlock ransomware group, with overlaps noticed with nation-state-aligned exercise clusters.
Flare screens underground boards and Telegram channels the place menace actors share PoCs, exploits, and compromised credentials inside hours of disclosure.
Get early warning when your infrastructure is mentioned or focused by ransomware operators.
Begin Free Trial
E-mail Servers: Id Infrastructure Attackers Goal First
E-mail servers sit at a novel intersection of belief and visibility.
They usually present:
- Area authentication tokens
- Password reset capabilities
- Exterior communication channels
- Entry to inside contact graphs
- Integration with id and listing providers
Attackers perceive that e mail ecosystems depend on multi-component authentication chains the place a single weak hyperlink can break total belief. Compromise the e-mail infrastructure and also you successfully compromise id.
1,200+ Weak Servers Recognized on Shodan
We discovered ~34,000 servers on Shodan with indications of working SmarterMail. Out of the 34,000, there have been 17,754 distinctive servers.
An additional inspection of those servers reveals that 1,185 are susceptible to authentication bypass or RCE flaws. Different publications speak about ~6,000 susceptible servers.
A geo-location evaluation of those 1,185 servers reveals US dominance:

An additional evaluation of the ISPs and Organizations reveals a really numerous distribution of open SmarterMail servers, many self-hosted admin panels, shared internet hosting, VPS suppliers, and general-purpose cloud networks, typical of deployment by people moderately than organizations.
This will point out that after the robust safety hype over the previous weeks, organizations have been fast to react and block this assault floor.
Underground Boards Share Exploits Inside Days of Disclosure
The underground ecosystems are quick to react to such publications. The CVEs have been revealed across the starting of January, and on the identical day, there have been mentions and references to those vulnerabilities. Up to now, we’ve seen dozens of publications and references to those vulnerabilities.
That is regular underground habits in relation to crucial vulnerabilities.
Now we have additionally seen some extra malicious references. A number of days after the primary publication, there have been references to Proof of Idea or exploit of the vulnerabilities. As an example, an Arabic-speaking Telegram channel reveals PoC.
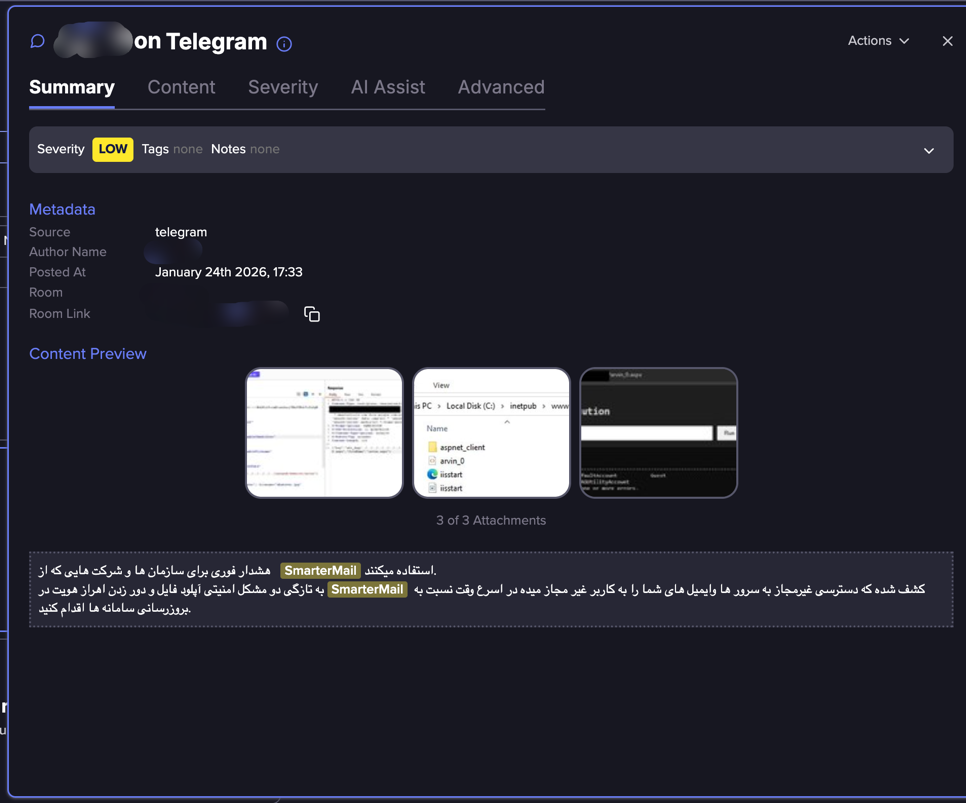
You too can see how the menace actor is exhibiting proof of idea:
And one other menace actor is exhibiting a proof of idea to this vulnerability:
In a Spanish-speaking Telegram group, we noticed references to an Offensive Safety Software:
On one other Telegram group, we noticed a knowledge dump of admin credentials highlighted because it comes from a compromised SmarterMail server:
When accessing one of many hyperlinks, you’ll be able to certainly see an extended checklist of admin credentials and the domains (or login) to which they belong.
CISA Confirms Lively Exploitation in Ransomware Campaigns
These vulnerabilities have been revealed to start with of 2026, CISA added CVE-2026-24423 to the Identified Exploited Vulnerabilities catalog to start with of February 2026, after confirming energetic ransomware exploitation.
This confirms that attackers are fast to use newly found crucial RCE- associated vulnerabilities:
- Vulnerability disclosure
- PoC written and launched
- Mass scanning operation
- Weaponization: Information exfiltration, Ransomware and many others.
Timeline shrinking from months/weeks to days.
The best way to Defend E-mail Infrastructure From Ransomware Entry
Many organizations nonetheless deal with e mail servers as “ONLY application infrastructure”. Properly, they don’t seem to be!
They’re id infrastructures that allow many follow-up assault vectors, in addition to containing secrets and techniques and enterprise logic. Defensive priorities ought to embody:
- Patch Urgency: Essential e mail server vulnerabilities needs to be handled like area controller vulnerabilities.
- Id Telemetry: Organizations ought to monitor these environments for:
- Admin password resets
- API calls to exterior hosts
- Sudden outbound HTTP from mail servers
- Community Segmentation: E-mail infrastructure ought to by no means have unrestricted entry to inside networks.
- Menace Looking Apply:
- API abuse patterns
- Scheduled process persistence
- Sudden tooling like DFIR frameworks or distant admin instruments
E-mail Servers Are Id Infrastructure—Safe Them Accordingly
The SmarterMail circumstances present as soon as once more how fashionable cybercrime operations are fast so as to add newly found preliminary entry to their ongoing operation.
It additionally re-emphasizes the crucial position e mail servers take within the fashionable group:
- Id brokers
- Belief anchors
- Enterprise logic
- Invaluable reconnaissance information for follow-up cybercrime
Organizations that proceed treating them as simply “messaging systems” will stay susceptible to this new technology of intrusion pipelines.
Be taught extra by signing up for our free trial.
Sponsored and written by Flare.